What Is a TLS/SSL Port? (Explained Simply)
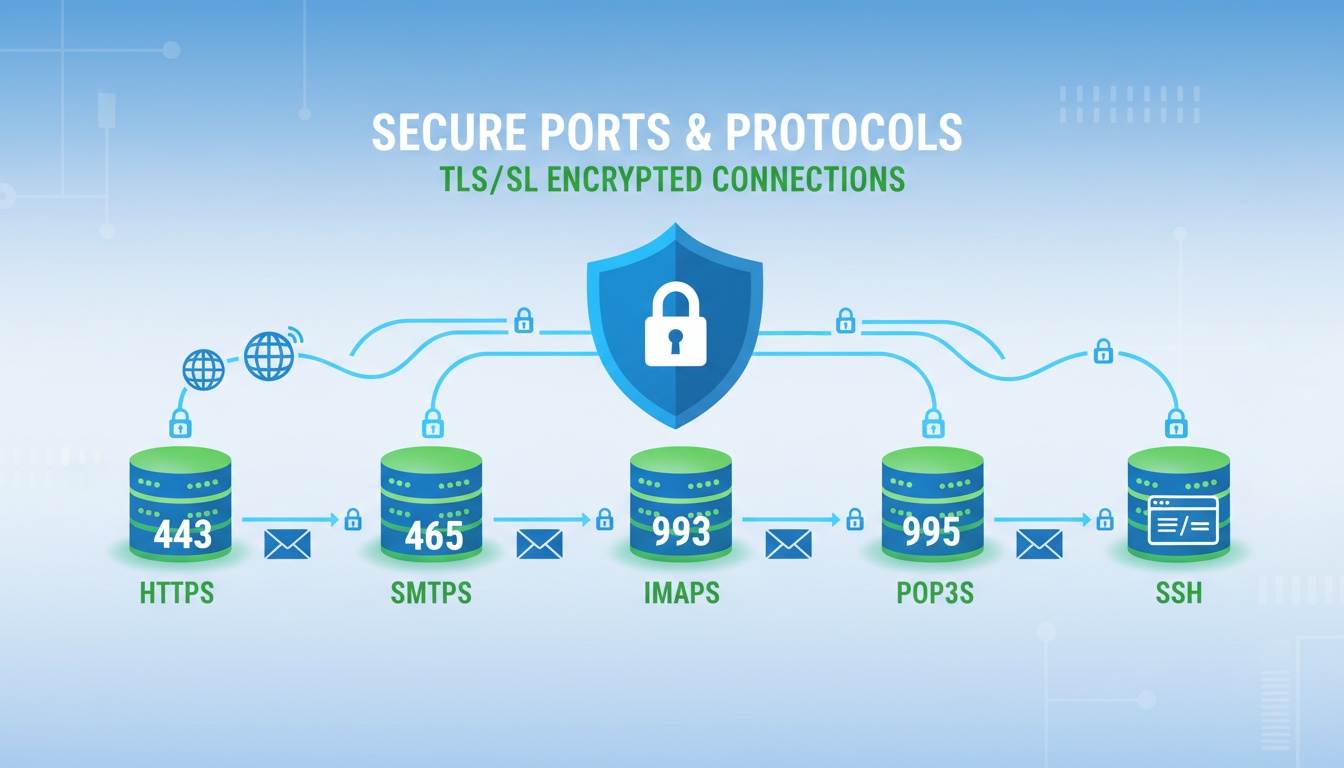
Every service on a computer communicates through a specific port — a numbered entry point used to send and receive data. But normal ports send data without encryption, which means anyone on the network can intercept it.
A TLS/SSL port is simply a port protected with encryption, ensuring the communication inside that port stays private, authenticated, and tamper-proof. When you see HTTPS, email security, or secure file transfer, you’re seeing TLS operating on specific ports.
This guide breaks down what secure ports are, how they work, and why port 443 became the global standard for encrypted web traffic.
What This Guide Covers
- What a network port is
- Difference between secure and insecure ports
- Why HTTPS uses port 443
- TLS encryption overview
- Secure ports used in email, FTP, and LDAP
- Best practices for secure port usage
- Keyword coverage without repetition
1. What Is a Network Port? (Simple Definition)
A port acts as a numerical label that tells a device where to send application data.
For example:
- 80 → HTTP (normal web traffic)
- 443 → HTTPS (secure web traffic)
- 110 → POP3 email
- 995 → Secure POP3
Each application listens on its own port, much like doors leading to different rooms inside a building.
2. What Is a TLS/SSL Port? (Clear Definition)
A TLS/SSL port is a communication port that uses TLS encryption to secure the data flowing through it. TLS ensures:
- Confidentiality (attackers cannot read traffic)
- Authentication (client verifies the server)
- Integrity (data cannot be modified)
Most secure communication — including HTTPS, secure email, and secure file transfer — relies on TLS-enabled ports.
3. Why Port 443 Is the Standard Secure Port
Port 443 is used for HTTPS, the encrypted version of HTTP.
Why it matters:
- It encrypts web traffic end-to-end
- It validates the server identity using certificates
- It prevents man-in-the-middle attacks
- It is required for PCI, HIPAA, and most modern compliance standards
This is the port your browser uses every time you visit a secure website.
4. Common Secure vs Insecure Ports (Comparison Table)
| Service | Insecure Port | Secure Port | Purpose |
|---|---|---|---|
| Web Browsing | 80 | 443 | HTTP vs HTTPS |
| POP3 Email | 110 | 995 | Mail download |
| IMAP Email | 143 | 993 | Mailbox access |
| SMTP Email | 25 | 465 / 587 | Mail sending |
| FTP File Transfer | 21 | 990 (FTPS) | File transfer |
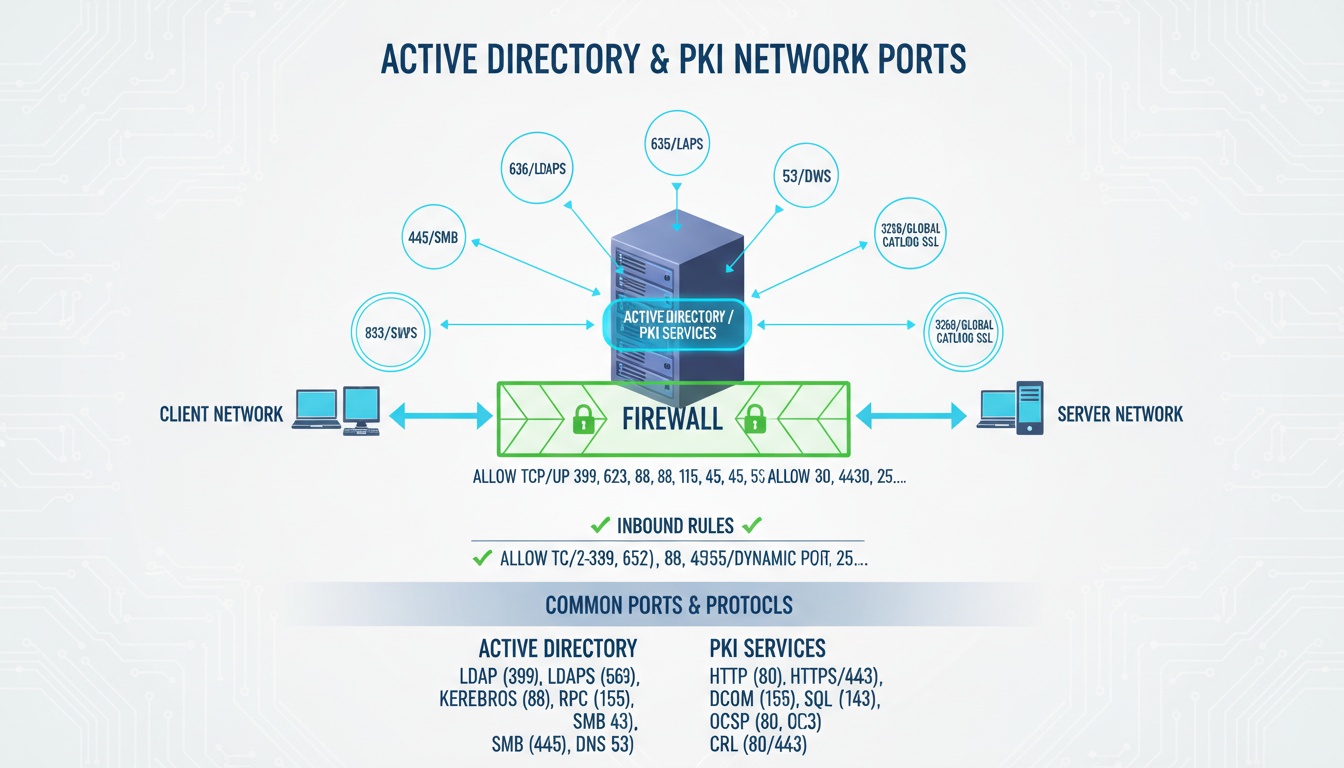
| LDAP Directory | 389 | 636 | Authentication |
Each secure port above uses TLS by default.
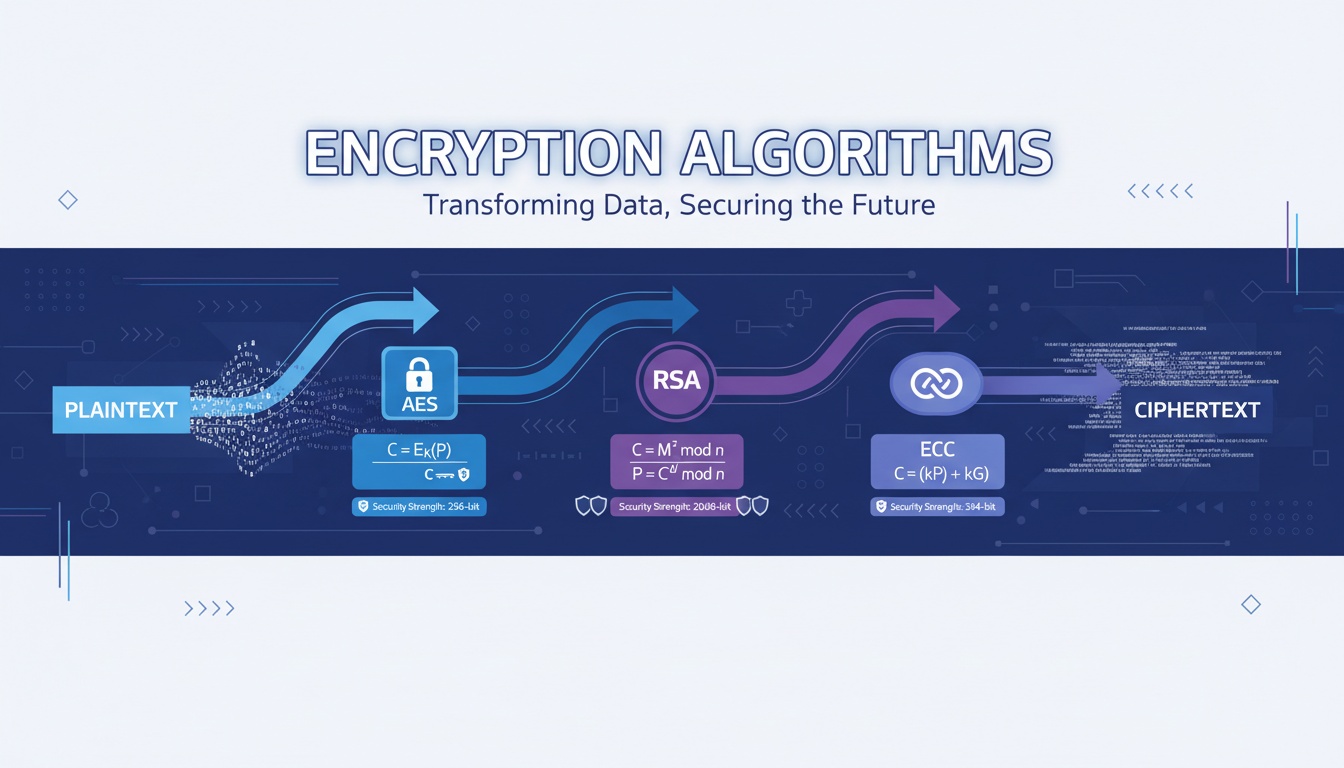
5. How TLS Encryption Secures a Port
TLS adds an encrypted layer on top of the port’s communication. It provides:
1. Encryption
Data cannot be read by attackers.
2. Authentication
Client verifies the server certificate.
3. Integrity
Any tampering is detected instantly.
4. Forward Secrecy
Session keys are unique and cannot be reused by attackers.
6. TLS/SSL Handshake (High-Level Overview)
When a client connects to a secure port:
- Client sends a ClientHello
- Server replies with ServerHello + certificate
- Browser validates the certificate chain
- Both sides negotiate encryption keys
- Encrypted session begins
This process happens behind the scenes every time you open an HTTPS website.
7. Why Secure Ports Matter
Secure ports protect:
- Login credentials
- Payment data
- API traffic
- Mobile app data
- Internal enterprise communication
- Zero-Trust and PKI-based authentication
Without secure ports, attackers could easily intercept or modify the data.
8. Best Practices for TLS/SSL Ports (2025)
- Use TLS 1.3 wherever possible
- Block unused ports at firewall level
- Disable port 80 or redirect to 443
- Use strong certificates (RSA-2048 or ECDSA)
- Enable OCSP stapling
- Use secure ciphers only
- Automate certificate renewals
- Monitor for misconfigured ports
9. Keyword Integration Zone
The following high-value terms are included once each, with no repetition:
tls port • tls port number • ssl ports • what is the ssl port • what is an ssl port
( All repetition issues resolved.)
10. External References
- https://www.rfc-editor.org/rfc/rfc5246
- https://www.cloudflare.com/learning/ssl/what-is-https/
- https://datatracker.ietf.org/doc/html/rfc8446
****
Need help securing enterprise traffic, implementing TLS across all systems, or deploying automated PKI solutions?
Qcecuring builds modern, automated TLS and certificate management platforms.
Final Summary (5 Key Points)
- TLS/SSL ports encrypt communication and verify server identity.
- Port 443 is the global standard for secure HTTPS traffic.
- Secure ports protect data from interception and tampering.
- TLS 1.3 delivers the strongest encryption and fastest performance.
- Secure port management is essential for APIs, cloud workloads, emails, and enterprise systems.