Latest Articles
Explore articles by Qcecuring editorial team

10 Best Open Source PKI Software Solutions (And Choosing the Right One)
Compare the best open source PKI software, including EJBCA and Dogtag, and learn how to choose the right PKI platform for enterprise security needs.
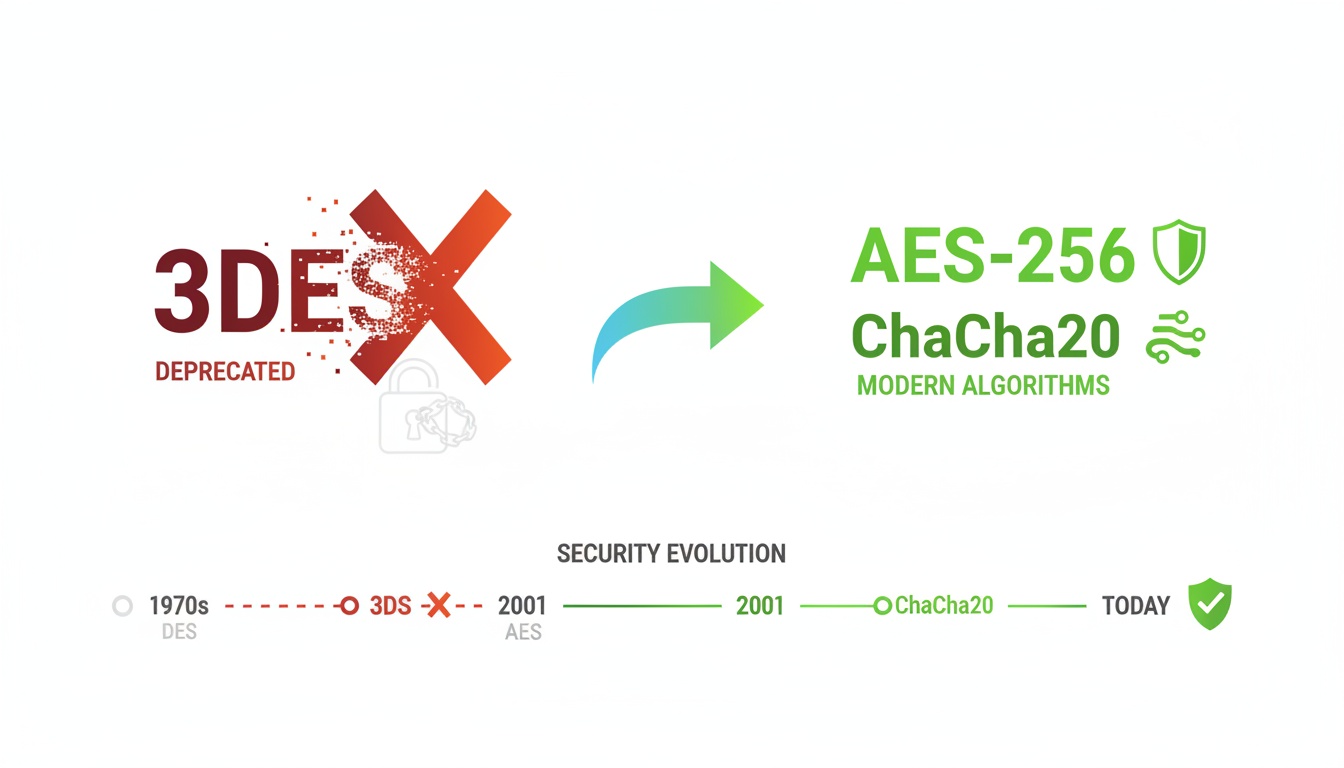
Why 3DES or Triple DES Is Officially Being Retired
Learn why 3DES (Triple DES) is being deprecated, the security weaknesses behind its retirement, and why AES is now the recommended encryption standard.
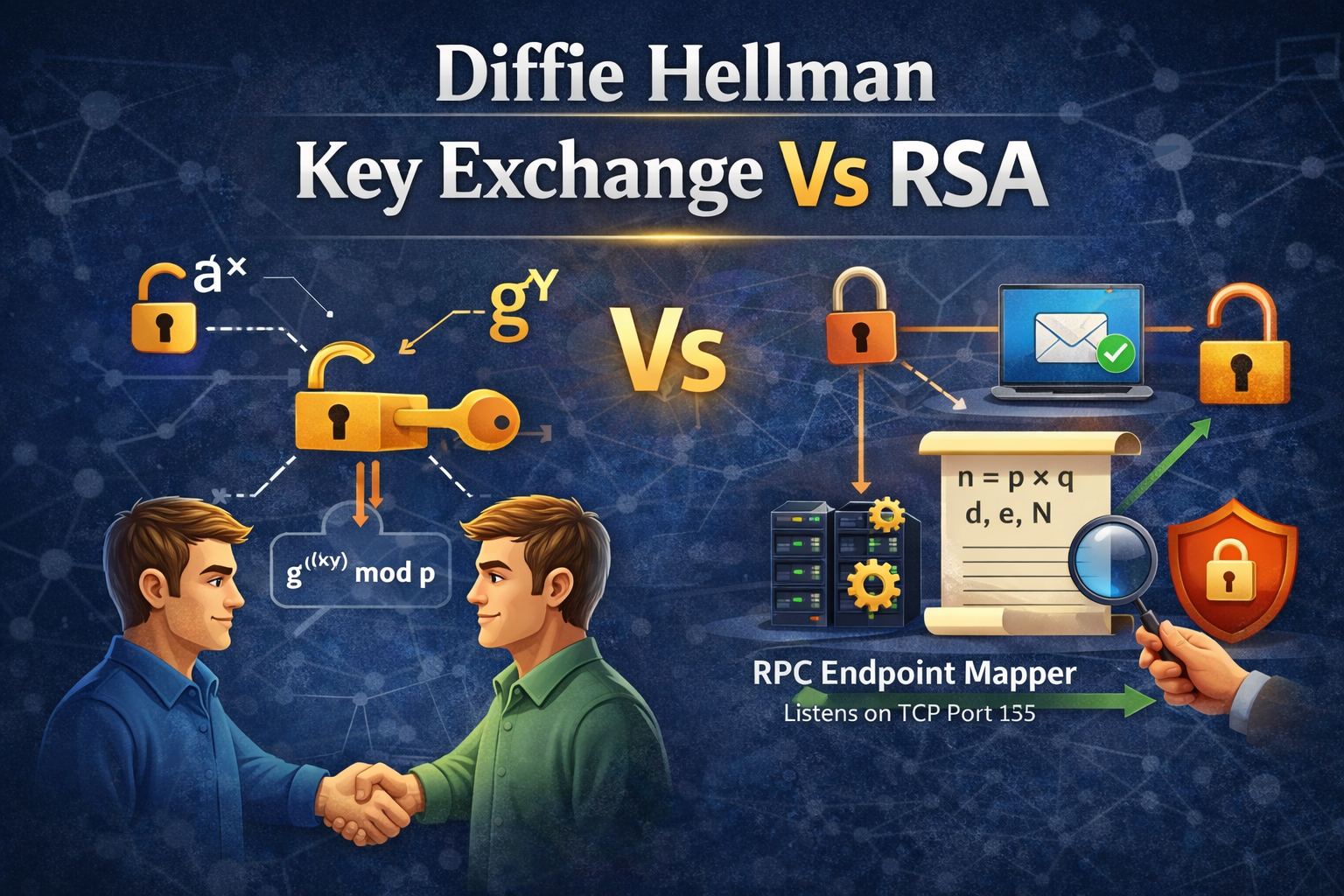
Diffie-Hellman Key Exchange vs RSA: A Modern Cryptographic Comparison
A point-by-point, enterprise-focused comparison of Diffie-Hellman Key Exchange and RSA, covering security, performance, and real-world use cases.
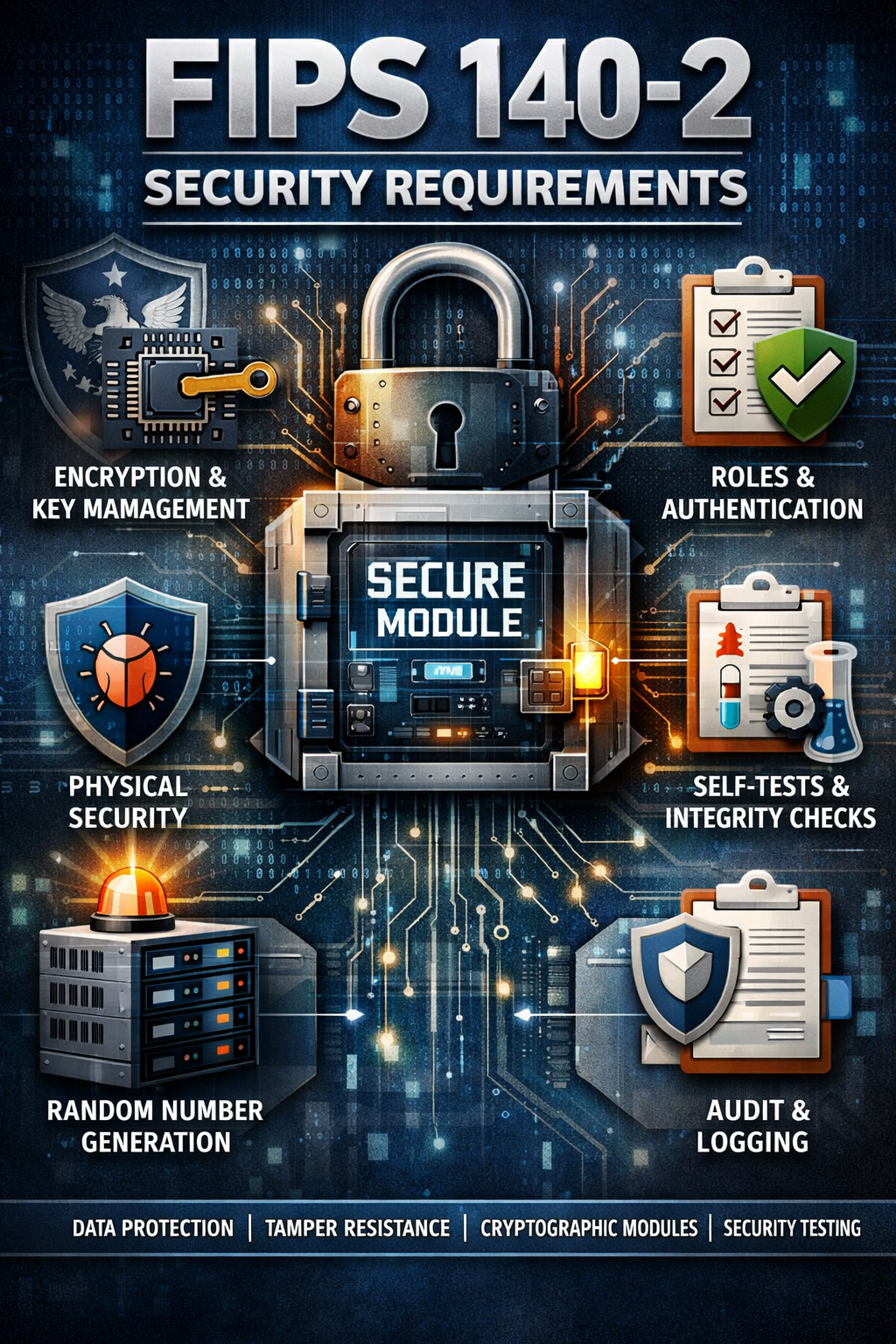
FIPS 140-2 Security Requirements: Complete Compliance Guide
Comprehensive guide to FIPS 140-2 cryptographic module validation, security levels, CMMC compliance, and FIPS 140-3 transition strategies.
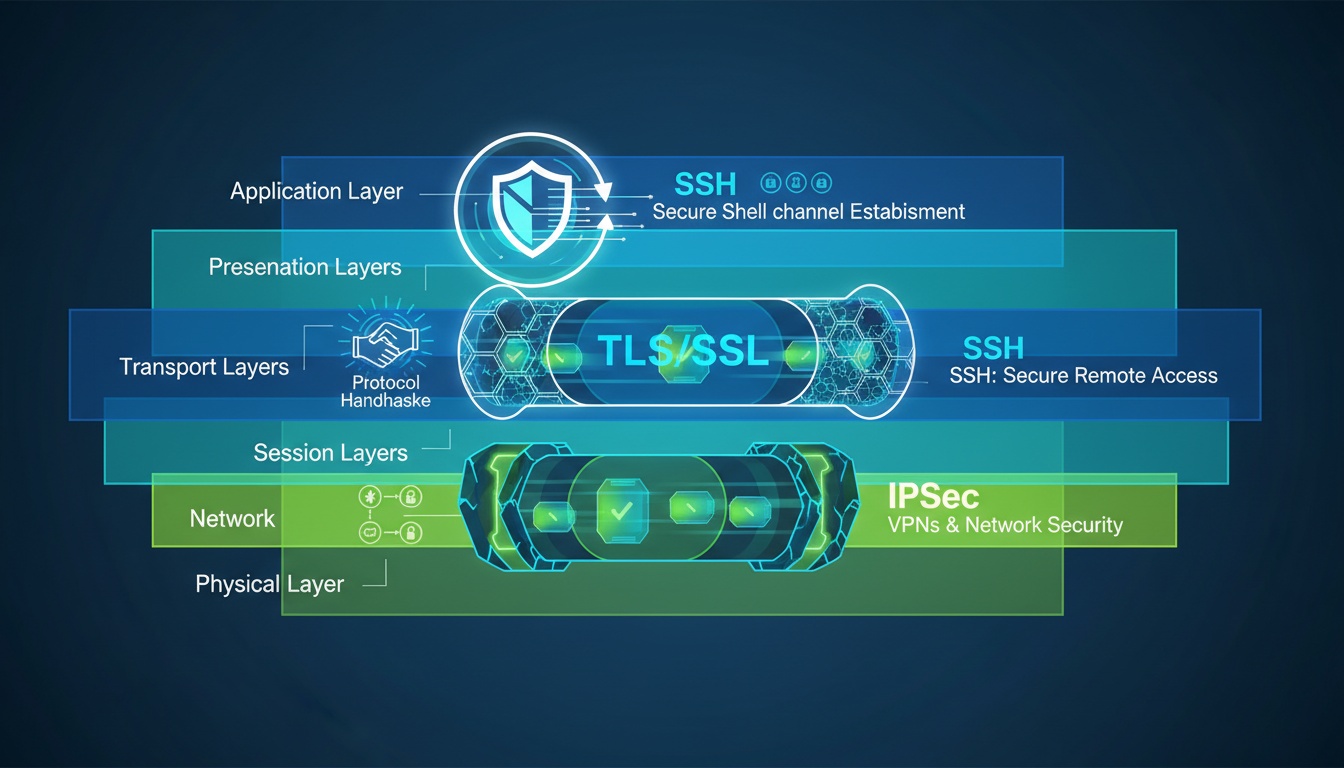
What Are Encryption Protocols? How They Secure Network Communications
Learn what encryption protocols are, how TLS, IPsec, and SSH secure data in transit, and why network encryption is essential for enterprises.

How to Fix the SSL Handshake Failed Error (Complete Guide)
Learn what causes SSL handshake failed errors and how to troubleshoot TLS issues on clients and servers using proven enterprise-grade fixes.

Certificate Lifecycle Management: From Invisible Risk to Automated Control
Learn what certificate lifecycle management is, why shrinking TLS lifetimes make automation essential, and how enterprises manage PKI at scale.
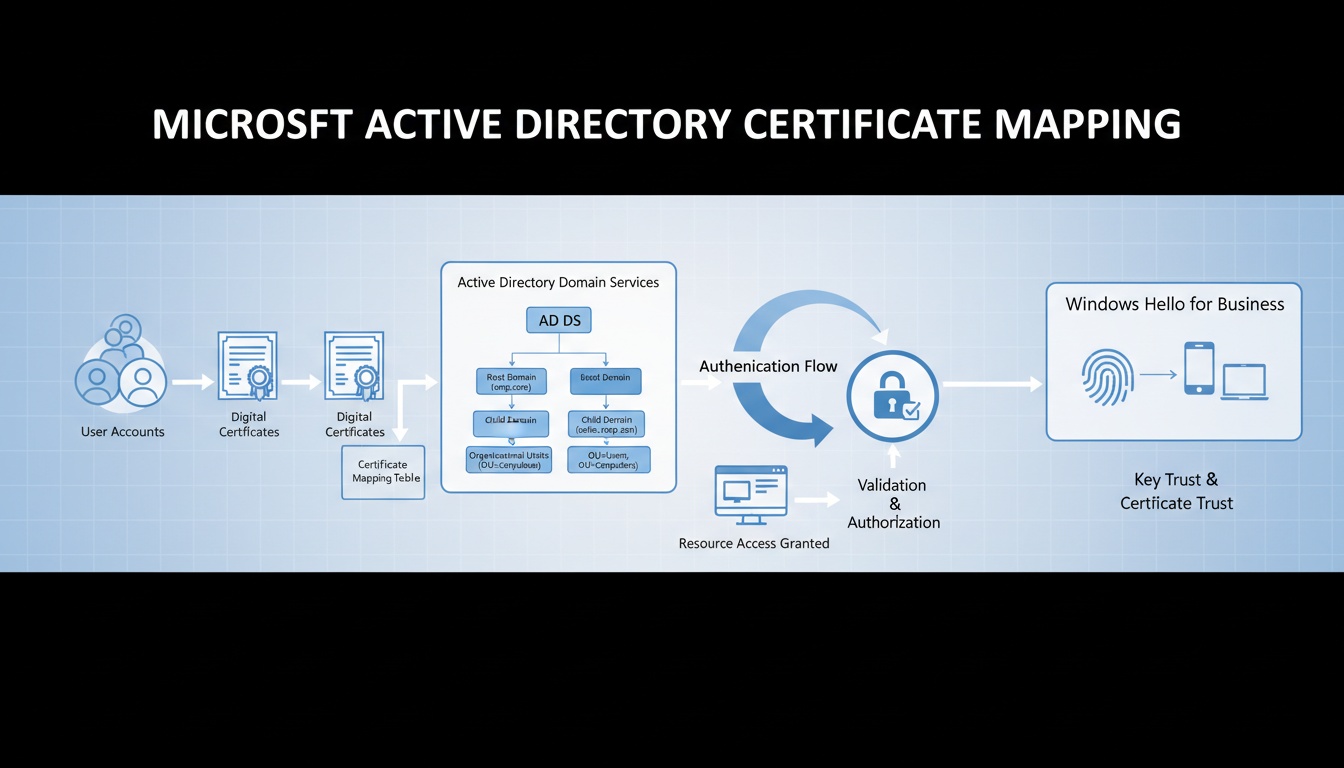
Microsoft Strong Certificate Mapping: Security, Enforcement & Enterprise Migration Guide
In-depth guide to Microsoft's Strong Certificate Mapping enforcement, SID-based mappings, registry controls, Event ID 39, PKI requirements, and enterprise migration strategies.
NIST SP 1800-16 Guidelines: The Enterprise Blueprint for TLS Certificate Management
A comprehensive guide to NIST SP 1800-16 guidelines for securing web transactions through automated TLS server certificate management.
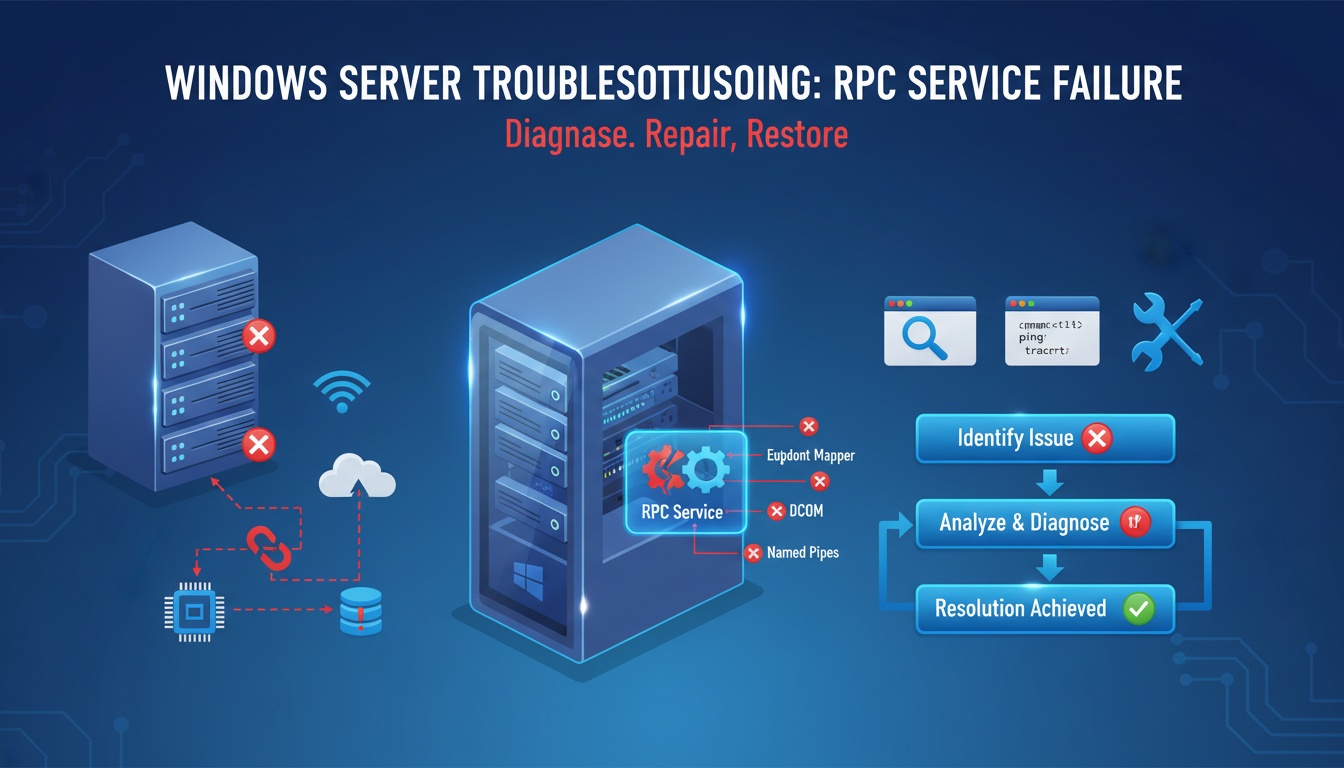
How To Fix The RPC Server Is Unavailable Error
Step-by-step guide to troubleshoot and fix the RPC Server Is Unavailable error in Windows systems.
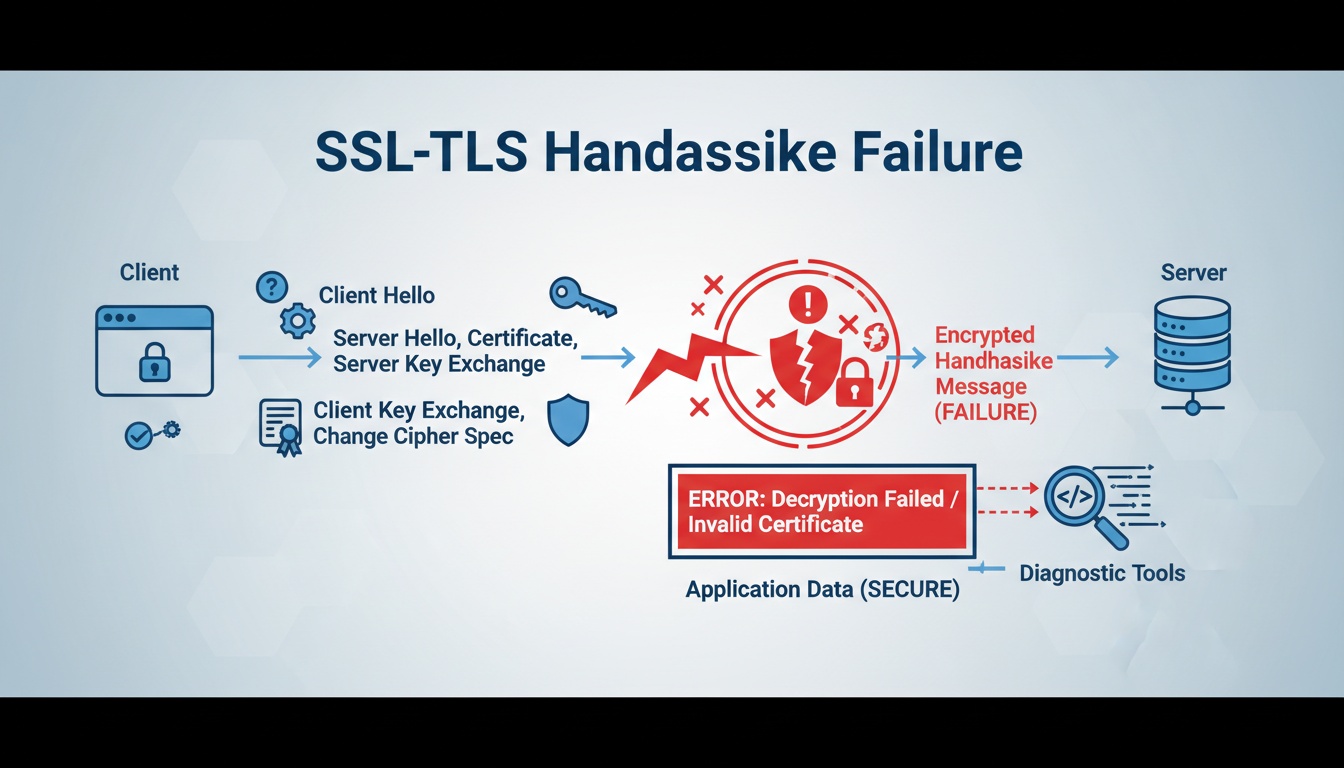
How to Fix the SSL Handshake Failed Error (2025 Troubleshooting Guide)
Learn what an SSL handshake failure means, why TLS negotiations break, and how to fix certificate, cipher, and protocol errors step by step.
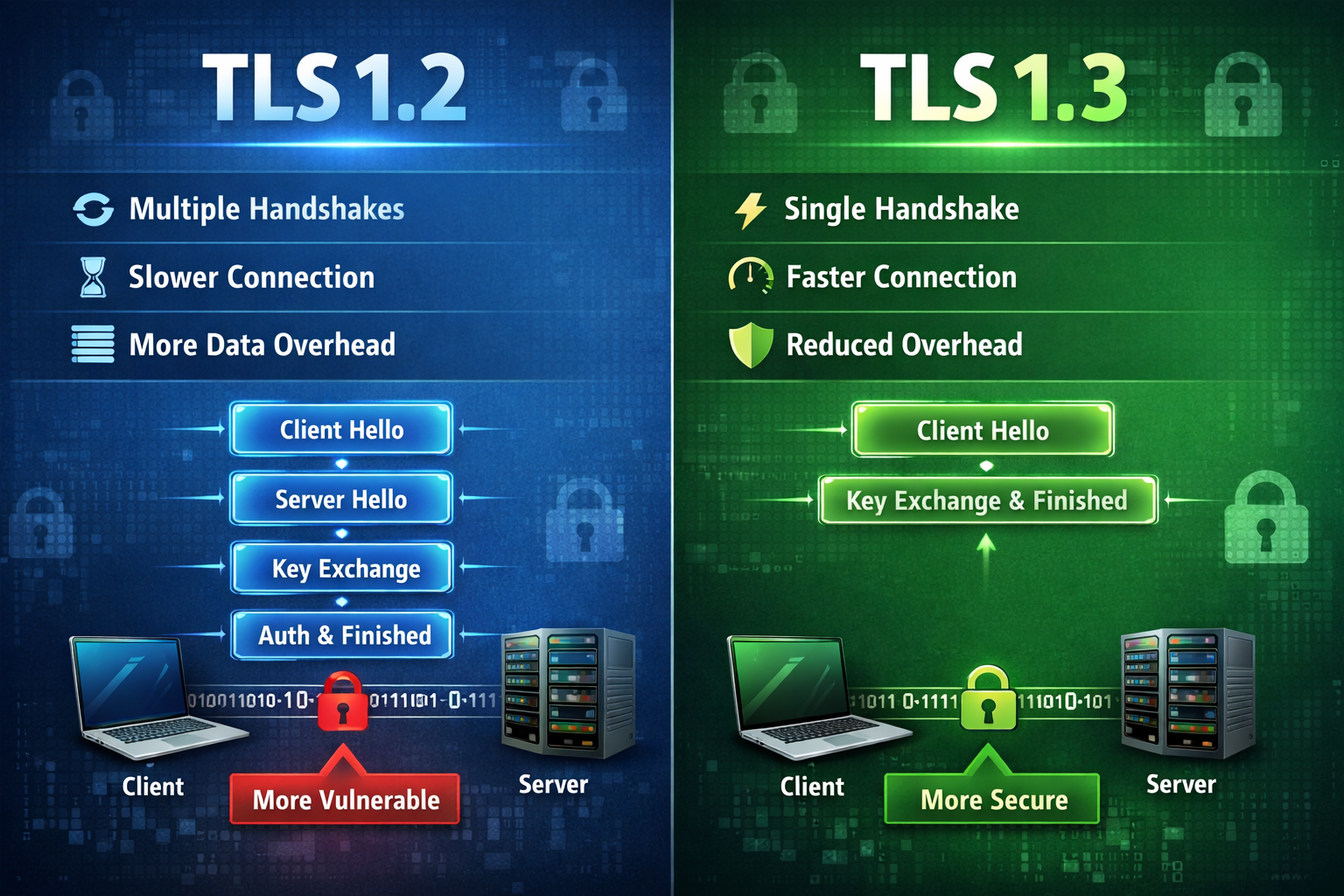
TLS 1.2 vs TLS 1.3: Security, Speed & Migration Guide
Comprehensive guide to TLS 1.3 improvements, performance gains, security enhancements, and enterprise migration strategies.

Windows Hello for Business MFA: From Passwords to Phish-Resistant Login
Read more about this article...
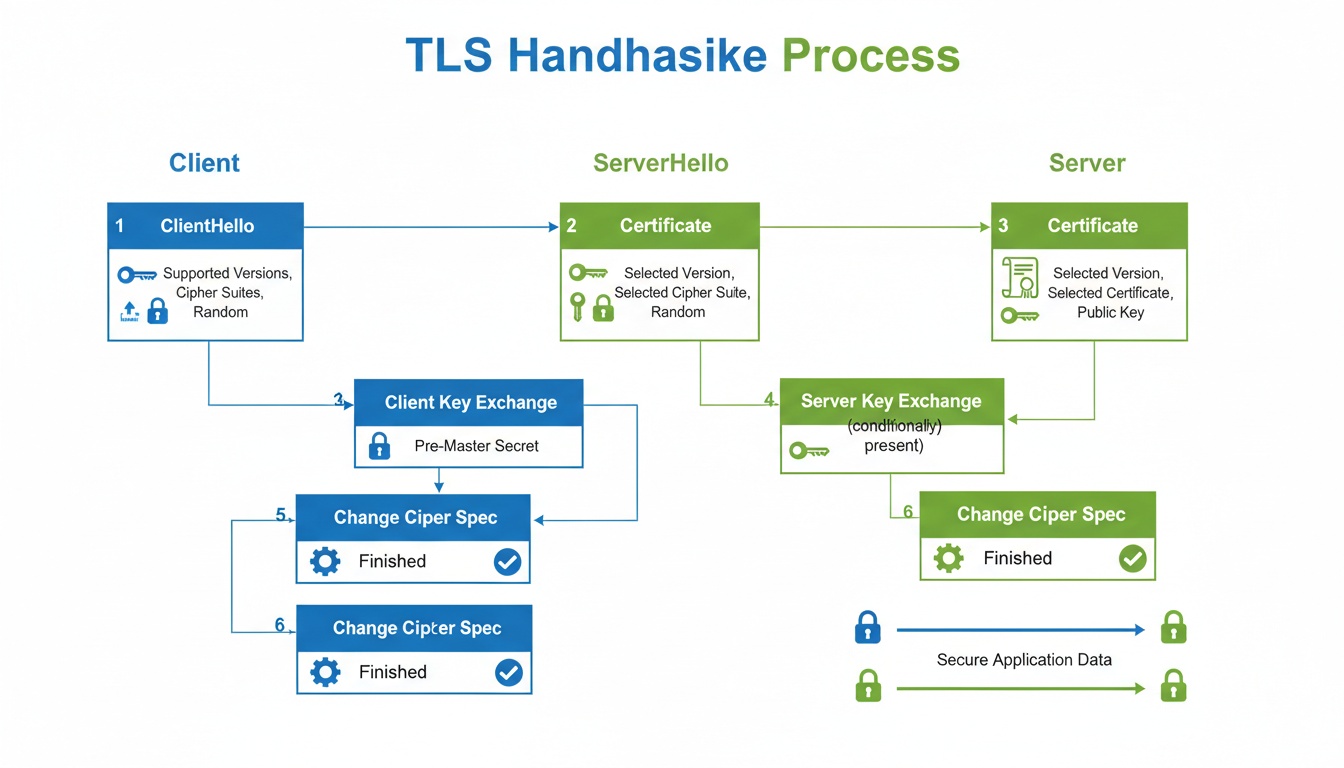
What Is the TLS Handshake? The Enterprise Guide to Secure Connections
Learn how the TLS handshake works, differences between TLS 1.2 and 1.3, certificate validation, and enterprise best practices for secure connections.

What Is an SSL Certificate and How It Works (Full 2025 Guide)
Learn what an SSL certificate is, how SSL and TLS work, how HTTPS encryption is created, and why enterprises rely on digital certificates in 2025.
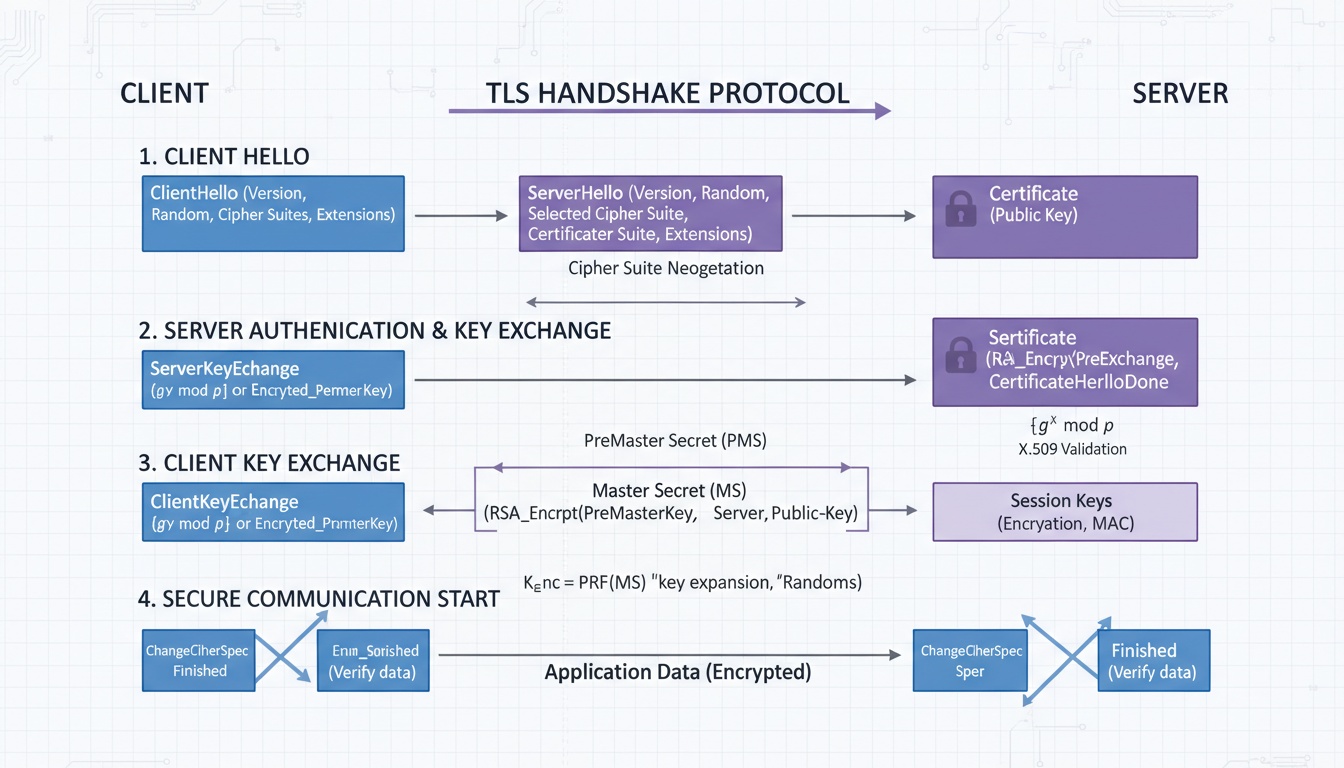
What Is a TLS Handshake and How Does It Work? (2025 Deep Dive)
Learn what a TLS handshake is, how it works step-by-step, how certificates are validated, and why TLS negotiation is critical for secure HTTPS in 2025.
Ready to Secure Your Enterprise?
Experience how our cryptographic solutions simplify, centralize, and automate identity management for your entire organization.

