Introduction
Digital certificates are the foundation of modern internet security, enabling encrypted communications, authentication, and data integrity. However, managing these certificates at scale presents significant challenges for organizations. This guide covers everything you need to know about certificate management.
What is Certificate Management?
Certificate management is the process of creating, distributing, storing, monitoring, renewing, and revoking digital certificates throughout their lifecycle. It encompasses all activities required to maintain a secure and operational certificate infrastructure.
Why Certificate Management Matters
Poor certificate management can lead to:
- Service outages from expired certificates
- Security vulnerabilities from weak or compromised certificates
- Compliance violations failing audit requirements
- Operational inefficiency from manual processes
- Financial losses from downtime and breaches
The Certificate Lifecycle
Understanding the certificate lifecycle is crucial for effective management.
1. Certificate Request
The lifecycle begins when an entity needs a certificate:
Steps:
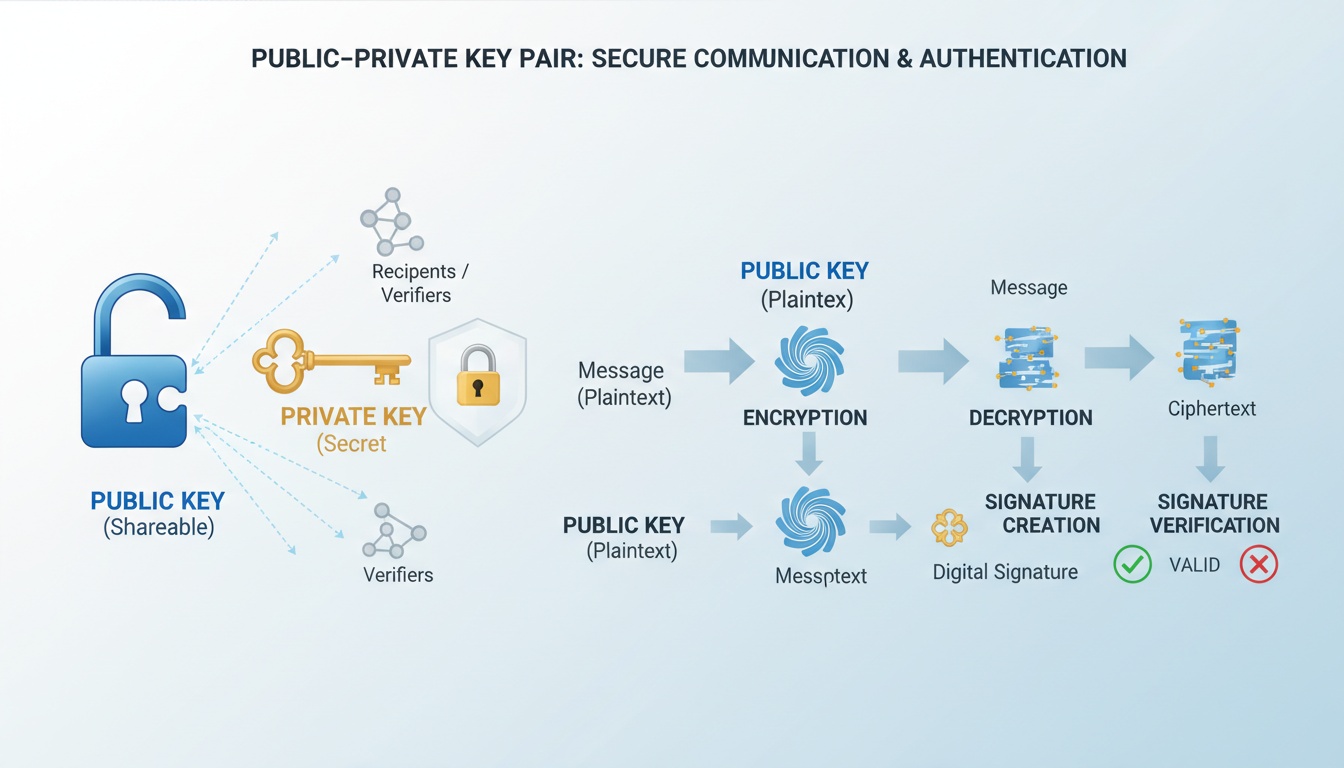
- Generate a key pair (public and private keys)
- Create a Certificate Signing Request (CSR)
- Submit CSR to Certificate Authority (CA)
- CA validates the request
Best Practices:
- Use strong key lengths (minimum 2048-bit RSA or 256-bit ECC)
- Protect private keys with encryption
- Include accurate subject information
- Document the purpose and owner
2. Certificate Issuance
After validation, the CA issues the certificate:
What Happens:
- CA signs the certificate with its private key
- Certificate is published to repository
- Certificate is delivered to requester
- Certificate is installed on target system
Validation Levels:
- Domain Validation (DV): Basic domain ownership check
- Organization Validation (OV): Verifies organization details
- Extended Validation (EV): Rigorous identity verification
3. Certificate Deployment
Installing and configuring certificates correctly:
Deployment Checklist:
- Install certificate on correct server/device
- Install intermediate certificates (chain)
- Configure proper cipher suites
- Test certificate installation
- Verify certificate chain
- Check for common issues (name mismatch, expired, etc.)
Common Deployment Locations:
- Web servers (Apache, Nginx, IIS)
- Load balancers
- API gateways
- Email servers
- VPN concentrators
- Code signing platforms
4. Certificate Monitoring
Continuous monitoring prevents outages:
What to Monitor:
- Expiration dates (alert 90, 60, 30 days before)
- Certificate revocation status
- Certificate usage and traffic
- Security vulnerabilities (weak algorithms, key length)
- Compliance status
Monitoring Tools:
- Certificate management platforms
- Network scanning tools
- SIEM integration
- Custom scripts and automation
5. Certificate Renewal
Replacing certificates before expiration:
Renewal Timeline:
- 90 days before: Initial renewal planning
- 60 days before: Generate new CSR
- 30 days before: Install new certificate
- 7 days before: Emergency renewal if needed
Renewal Methods:
- Manual renewal (small deployments)
- Automated renewal (ACME protocol)
- Bulk renewal (enterprise tools)
6. Certificate Revocation
Invalidating certificates before expiration:
Revocation Reasons:
- Private key compromise
- CA compromise
- Change in affiliation
- Certificate superseded
- Cessation of operation
Revocation Methods:
- Certificate Revocation Lists (CRLs)
- Online Certificate Status Protocol (OCSP)
- OCSP Stapling
Common Certificate Management Challenges
Challenge 1: Certificate Sprawl
Problem: Organizations lose track of certificates across their infrastructure.
Impact:
- Unknown certificate inventory
- Unexpected expirations
- Security blind spots
- Compliance gaps
Solution:
- Implement certificate discovery tools
- Maintain centralized inventory
- Automate certificate tracking
- Regular audits and reconciliation
Challenge 2: Manual Processes
Problem: Manual certificate operations don’t scale.
Impact:
- Human errors
- Slow deployment
- Inconsistent configurations
- High operational costs
Solution:
- Automate certificate lifecycle
- Use certificate management platforms
- Implement ACME protocol
- Create self-service portals
Challenge 3: Expiration Management
Problem: Certificates expire, causing outages.
Statistics:
- 80% of organizations experienced certificate-related outages
- Average cost of certificate outage: $15 million
- Most outages are preventable
Solution:
- Automated expiration monitoring
- Multi-channel alerting (email, SMS, Slack)
- Automated renewal workflows
- Buffer time for renewals (90+ days)
Challenge 4: Compliance Requirements
Problem: Meeting regulatory and audit requirements.
Requirements:
- PCI DSS: Certificate inventory and monitoring
- SOC 2: Certificate lifecycle documentation
- HIPAA: Encryption and certificate management
- ISO 27001: Cryptographic controls
Solution:
- Automated compliance reporting
- Audit trail maintenance
- Policy enforcement
- Regular compliance assessments
Certificate Management Best Practices
1. Centralize Certificate Management
Benefits:
- Single source of truth
- Consistent policies
- Simplified operations
- Better visibility
Implementation:
- Deploy certificate management platform
- Integrate with existing tools
- Establish governance model
- Train operations team
2. Automate the Lifecycle
Automation Opportunities:
- Certificate discovery
- Expiration monitoring
- Renewal workflows
- Deployment processes
- Compliance reporting
Tools and Protocols:
- ACME (Automated Certificate Management Environment)
- SCEP (Simple Certificate Enrollment Protocol)
- EST (Enrollment over Secure Transport)
- REST APIs
3. Implement Strong Policies
Policy Areas:
- Key length requirements (minimum 2048-bit)
- Validity periods (maximum 398 days for public TLS)
- Approved CAs and certificate types
- Naming conventions
- Renewal timelines
- Revocation procedures
4. Monitor Continuously
Monitoring Strategy:
- Real-time certificate discovery
- Expiration tracking with alerts
- Security vulnerability scanning
- Compliance status monitoring
- Usage analytics
5. Plan for Incidents
Incident Response Plan:
- Certificate compromise procedures
- Emergency renewal process
- Revocation workflows
- Communication templates
- Escalation paths
Certificate Management Tools
Enterprise Solutions
Commercial Platforms:
- Venafi Trust Protection Platform
- DigiCert CertCentral
- Sectigo Certificate Manager
- AppViewX CERT+
Features:
- Automated discovery
- Lifecycle automation
- Policy enforcement
- Compliance reporting
- Multi-CA support
Open Source Tools
Popular Options:
- Certbot (Let’s Encrypt client)
- Boulder (ACME CA)
- CFSSL (CloudFlare’s PKI toolkit)
- OpenSSL (cryptographic toolkit)
Use Cases:
- Small to medium deployments
- Development environments
- Custom integrations
- Learning and testing
Cloud-Native Solutions
Cloud Provider Services:
- AWS Certificate Manager (ACM)
- Azure Key Vault
- Google Cloud Certificate Manager
- Let’s Encrypt (free, automated)
Advantages:
- Integrated with cloud services
- Automated renewal
- No additional cost (some services)
- Scalable and reliable
Certificate Types and Use Cases
SSL/TLS Certificates
Purpose: Secure web communications
Types:
- Single domain
- Wildcard (*.example.com)
- Multi-domain (SAN)
- Extended Validation (EV)
Use Cases:
- Websites and web applications
- APIs and microservices
- Load balancers
- CDN endpoints
Code Signing Certificates
Purpose: Verify software authenticity
Platforms:
- Windows (Authenticode)
- macOS (Apple Developer)
- Java (JAR signing)
- Mobile apps (iOS, Android)
Benefits:
- Proves software origin
- Detects tampering
- Builds user trust
- Required for distribution
Email Certificates (S/MIME)
Purpose: Secure email communications
Features:
- Email encryption
- Digital signatures
- Sender authentication
- Non-repudiation
Use Cases:
- Executive communications
- Financial transactions
- Healthcare (HIPAA)
- Legal documents
Client Certificates
Purpose: User and device authentication
Applications:
- VPN access
- Wi-Fi authentication (802.1X)
- API authentication
- Zero-trust networks
Benefits:
- Strong authentication
- No passwords needed
- Device binding
- Centralized management
Measuring Certificate Management Success
Key Metrics
Operational Metrics:
- Certificate inventory accuracy (target: 100%)
- Average time to issue certificate (target: < 1 hour)
- Renewal success rate (target: 100%)
- Outages due to certificates (target: 0)
Security Metrics:
- Certificates with weak algorithms (target: 0)
- Expired certificates in production (target: 0)
- Time to revoke compromised certificate (target: < 1 hour)
- Compliance score (target: 100%)
Business Metrics:
- Cost per certificate
- Staff time saved through automation
- Downtime prevented
- Audit findings reduced
Future of Certificate Management
Emerging Trends
Shorter Certificate Lifespans:
- Current: 398 days maximum
- Trend: Moving toward 90 days or less
- Impact: Automation becomes mandatory
Certificate Transparency:
- Public logging of all certificates
- Detect mis-issued certificates
- Improve ecosystem security
Post-Quantum Cryptography:
- Quantum-resistant algorithms
- Migration planning required
- Hybrid approaches during transition
Zero Trust Architecture:
- Certificate-based authentication
- Continuous verification
- Micro-segmentation
Conclusion
Effective certificate management is essential for maintaining security, ensuring availability, and meeting compliance requirements. By understanding the certificate lifecycle, implementing best practices, and leveraging automation tools, organizations can:
- Prevent certificate-related outages
- Reduce operational costs
- Improve security posture
- Maintain compliance
- Scale certificate operations
The key to success is treating certificate management as a critical operational discipline, not an afterthought. Start with visibility, automate where possible, and continuously improve your processes.
Ready to modernize your certificate management? Contact our team for expert guidance on implementing automated certificate lifecycle management solutions.