What is PKI?
Public Key Infrastructure (PKI) is a comprehensive framework of policies, procedures, hardware, software, and people that work together to create, manage, distribute, use, store, and revoke digital certificates. At its core, PKI enables secure electronic transfer of information for a range of network activities.
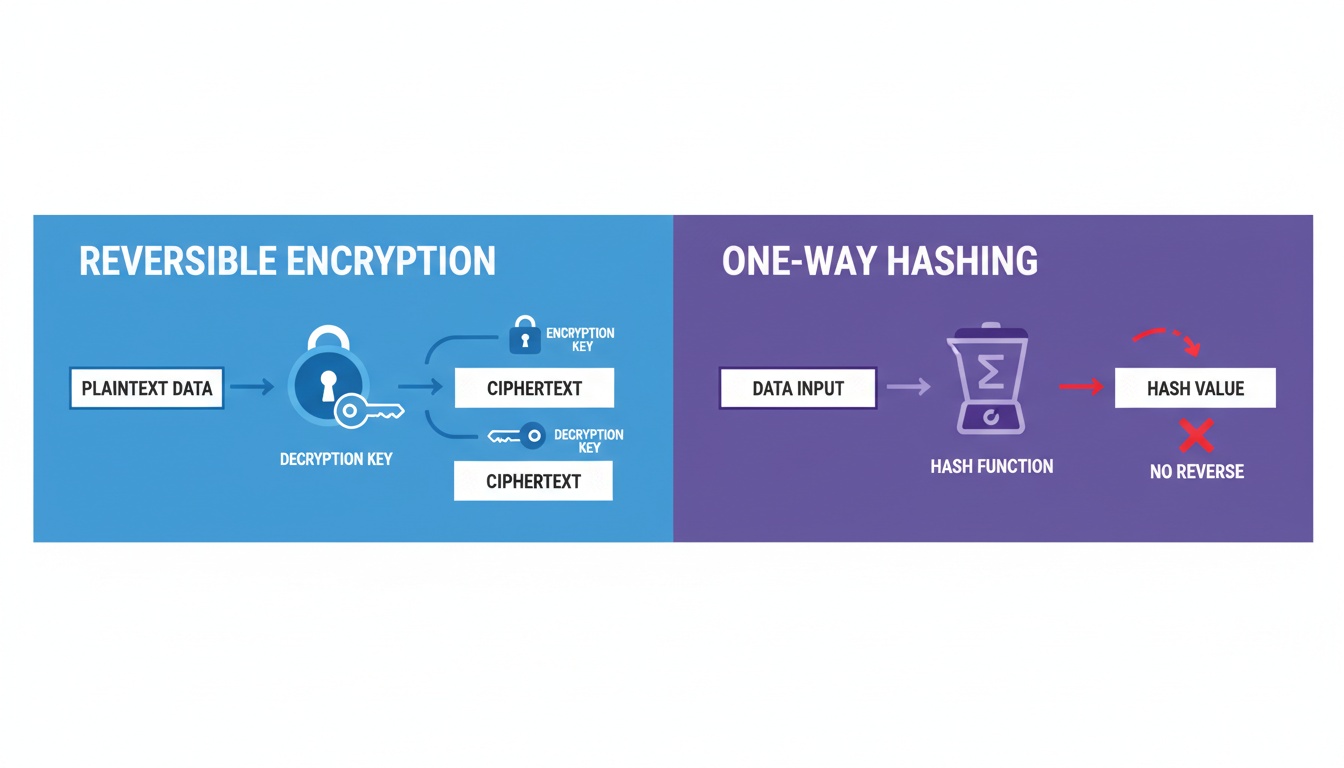
PKI uses a pair of cryptographic keys—a public key and a private key—to encrypt and decrypt data. The public key is openly distributed, while the private key remains confidential to its owner. This asymmetric encryption ensures that only the intended recipient can decrypt messages encrypted with their public key.
Why PKI Matters
In today’s digital landscape, PKI serves as the backbone of secure communications:
- Authentication: Verifies the identity of users, devices, and services
- Confidentiality: Ensures data remains private during transmission
- Integrity: Guarantees data hasn’t been tampered with
- Non-repudiation: Prevents parties from denying their actions
Components of PKI
Understanding PKI requires familiarity with its key components:
1. Certificate Authority (CA)
The Certificate Authority is the trusted entity that issues digital certificates. The CA:
- Validates the identity of certificate requesters
- Issues, signs, and publishes certificates
- Maintains certificate status information
- Publishes Certificate Revocation Lists (CRLs)
Types of CAs:
- Root CA: The top-level CA in the hierarchy, self-signed and highly protected
- Intermediate CA: Subordinate CAs that issue certificates on behalf of the Root CA
- Issuing CA: The CA that directly issues end-entity certificates
2. Registration Authority (RA)
The Registration Authority acts as a verifier for the CA. The RA:
- Accepts certificate requests
- Authenticates the identity of certificate requesters
- Approves or rejects certificate requests
- Does not issue certificates directly
This separation of duties enhances security by distributing trust responsibilities.
3. Digital Certificates
Digital certificates are electronic documents that bind a public key to an identity. A standard X.509 certificate contains:
- Subject: The entity the certificate represents
- Public Key: The subject’s public key
- Issuer: The CA that issued the certificate
- Validity Period: Start and end dates
- Serial Number: Unique identifier
- Signature: CA’s digital signature
4. Certificate Revocation List (CRL)
A CRL is a list of certificates that have been revoked before their expiration date. Reasons for revocation include:
- Private key compromise
- CA compromise
- Change in affiliation
- Certificate superseded
- Cessation of operation
5. Certificate Repository
A centralized directory where certificates and CRLs are stored and published. This allows:
- Easy certificate distribution
- Public access to certificate status
- Centralized certificate management
How Certificate Issuance Works
The certificate issuance process follows a well-defined workflow:
Step 1: Key Pair Generation
The end entity (user, device, or service) generates a public-private key pair. The private key must be:
- Generated securely using cryptographically strong random number generators
- Stored securely, often in hardware security modules (HSMs)
- Never transmitted or shared
Step 2: Certificate Signing Request (CSR)
The entity creates a CSR containing:
- Public key
- Subject information (name, organization, location)
- Additional attributes
- Digital signature created with the private key
The CSR proves the entity possesses the corresponding private key without revealing it.
Step 3: Identity Verification
The RA receives the CSR and performs identity verification:
For Domain Validation (DV):
- Verifies domain ownership through DNS records or email
- Minimal validation, fastest issuance
For Organization Validation (OV):
- Verifies organization’s legal existence
- Confirms organization controls the domain
- Typically takes 1-3 days
For Extended Validation (EV):
- Rigorous verification of legal, physical, and operational existence
- Confirms exclusive domain control
- Requires 2-7 days
Step 4: Certificate Issuance
Once verified, the CA:
- Creates the certificate with the provided information
- Signs the certificate with its private key
- Publishes the certificate to the repository
- Delivers the certificate to the requester
Step 5: Certificate Installation
The entity installs the certificate on their server, device, or application. The certificate is now ready to:
- Establish secure TLS/SSL connections
- Sign documents and code
- Authenticate users and devices
Step 6: Certificate Lifecycle Management
Throughout its lifetime, the certificate requires:
- Monitoring: Track expiration dates
- Renewal: Replace before expiration
- Revocation: Invalidate if compromised
- Auditing: Maintain compliance records
Real-World Use Cases
PKI powers numerous security applications across industries:
1. Secure Web Communications (TLS/SSL)
Scenario: E-commerce website securing customer transactions
When you visit an HTTPS website:
- Your browser requests the server’s certificate
- The server sends its certificate signed by a trusted CA
- Your browser verifies the certificate’s validity
- A secure encrypted connection is established
- All data transmitted is encrypted
Business Impact:
- Protects customer payment information
- Builds trust with visual security indicators
- Required for PCI DSS compliance
- Improves SEO rankings
2. Email Security (S/MIME)
Scenario: Healthcare organization securing patient communications
S/MIME certificates enable:
- Encryption: Only intended recipients can read emails
- Digital Signatures: Verify sender identity and message integrity
- Non-repudiation: Proof of email origin
Business Impact:
- HIPAA compliance for patient data
- Protection against email spoofing
- Legal validity of electronic communications
3. Code Signing
Scenario: Software vendor distributing applications
Code signing certificates:
- Prove software authenticity
- Verify code hasn’t been modified
- Enable trust warnings to be bypassed
- Required for app store distribution
Business Impact:
- Prevents malware distribution
- Builds customer confidence
- Meets platform requirements (Windows, macOS, iOS, Android)
4. Document Signing
Scenario: Financial institution processing loan applications
Digital signatures on PDF documents:
- Legally binding in most jurisdictions
- Tamper-evident seals
- Audit trails for compliance
- Faster processing than physical signatures
Business Impact:
- Accelerates business processes
- Reduces paper and storage costs
- Meets regulatory requirements (eIDAS, ESIGN Act)
5. IoT Device Authentication
Scenario: Manufacturing company securing industrial IoT devices
Device certificates enable:
- Mutual authentication between devices and servers
- Secure firmware updates
- Protection against device spoofing
- Encrypted sensor data transmission
Business Impact:
- Prevents unauthorized device access
- Protects intellectual property
- Ensures operational integrity
- Meets IEC 62443 standards
6. VPN and Network Access
Scenario: Enterprise securing remote workforce access
Certificate-based authentication:
- Stronger than password-only authentication
- Enables zero-trust network access
- Supports multi-factor authentication
- Scales to thousands of users
Business Impact:
- Reduces credential theft risk
- Simplifies user experience
- Centralized access management
- Compliance with security frameworks
7. Cloud Service Authentication
Scenario: SaaS provider securing API access
API certificates provide:
- Service-to-service authentication
- Encrypted data in transit
- Rate limiting and access control
- Audit logging
Business Impact:
- Protects customer data
- Enables secure integrations
- Meets SOC 2 requirements
- Supports microservices architecture
Best Practices for PKI Implementation
To maximize PKI effectiveness:
- Establish Clear Policies: Define certificate issuance, usage, and revocation policies
- Implement Strong Key Management: Use HSMs for CA keys, enforce key length requirements
- Automate Certificate Lifecycle: Reduce manual errors and prevent outages
- Monitor Certificate Inventory: Maintain visibility across all certificates
- Plan for Disaster Recovery: Backup CA keys and configuration securely
- Regular Audits: Ensure compliance with policies and standards
- User Training: Educate staff on PKI concepts and procedures
Conclusion
Public Key Infrastructure is fundamental to modern cybersecurity. By understanding its components, certificate issuance process, and real-world applications, organizations can leverage PKI to:
- Establish trust in digital interactions
- Protect sensitive data
- Meet compliance requirements
- Enable secure digital transformation
As cyber threats evolve, PKI remains a critical technology for ensuring the confidentiality, integrity, and authenticity of digital communications.
Ready to implement PKI in your organization? Contact our security experts for a personalized consultation on certificate management solutions.