Introduction
In cybersecurity and cryptography, two concepts that are constantly mentioned together – and just as often mixed up – are encryption and hashing. Both transform readable data into another form, and at a quick glance they can look similar, but under the hood they solve very different problems. Knowing when to use encryption vs hashing is a core skill for anyone designing secure systems, storing passwords, or protecting sensitive information.
This guide breaks down the encryption and hashing difference in clear, practical terms. You will learn what each technique does, how they work, where they are used, and why security engineers often combine them for stronger protection. By the end, you should be comfortable answering questions like “Is hashing encryption?”, “What is the difference between hashing and encryption?”, “How is hashing different from encryption?”, and “When should I encrypt vs when should I hash?”.
In this article, we will cover:
- What encryption is in cryptography
- What hashing is in cybersecurity and cryptography
- Hash vs encrypt — the key conceptual and technical differences
- Why hashing is one-way and encryption is two-way
- Common algorithms such as AES, RSA, SHA-256, and Bcrypt
- Real-world use cases: passwords, file protection, integrity checks, and more
What is Encryption?
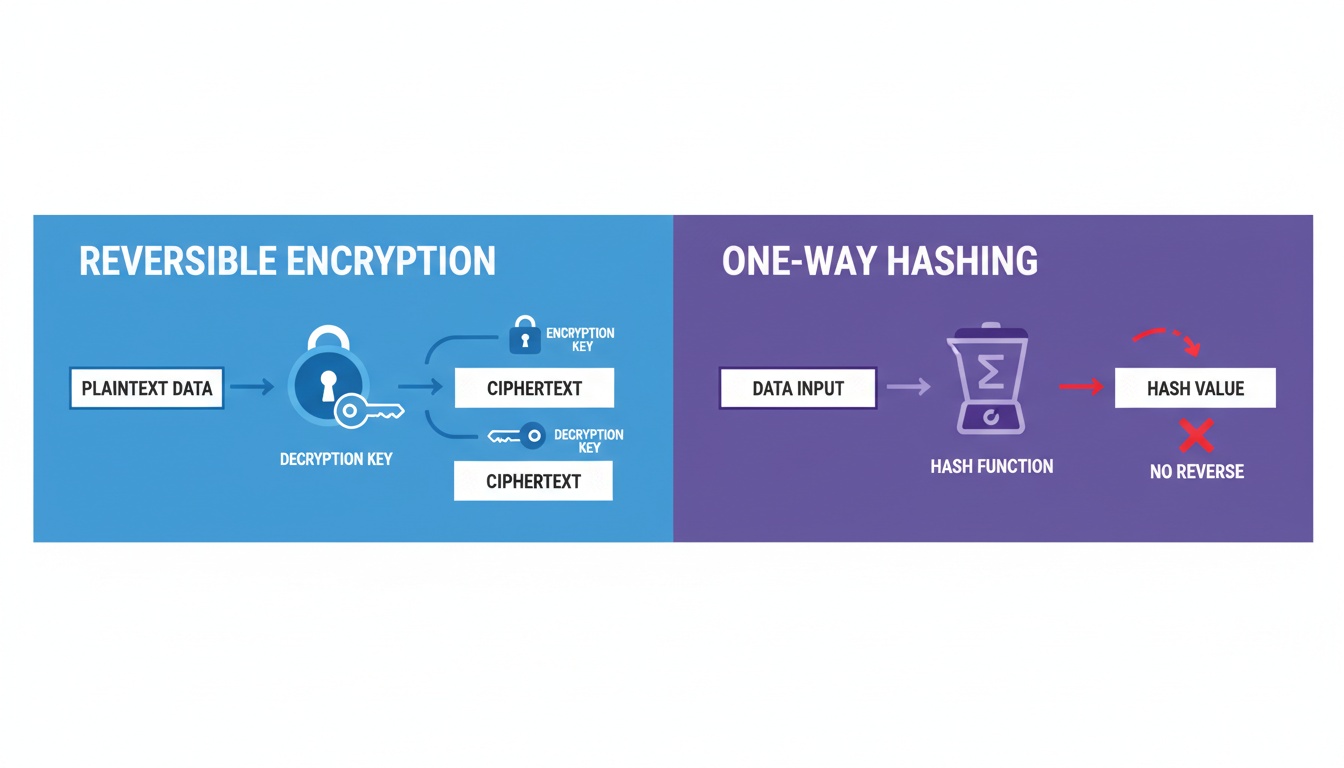
Encryption is the process of converting readable information (plaintext) into an unreadable format (ciphertext) using a cryptographic key. The main goal of encryption is confidentiality: even if someone intercepts the data, they cannot understand it without the correct key to decrypt it. When people compare “encrypted vs hashed” data, encryption is the part that keeps information secret, not just verified.
A crucial property of encryption is that it is reversible. As long as the right key and algorithm are available, ciphertext can be transformed back into the original plaintext. This makes encryption ideal for scenarios where data must remain confidential during storage or transmission but still needs to be recovered later by authorized parties. This is why encryption is used heavily in SSL/TLS, VPNs, and disk encryption rather than for password storage.
Encryption is two-way: data is encrypted with a key and decrypted with a corresponding key.
Key Properties of Encryption
| Property | Description |
|---|---|
| Purpose | Protect data confidentiality |
| Direction | Two-way (encrypt and decrypt) |
| Output | Reversible ciphertext |
| Key Type | Symmetric or asymmetric keys |
| Examples | AES, RSA, DES, ChaCha20 |
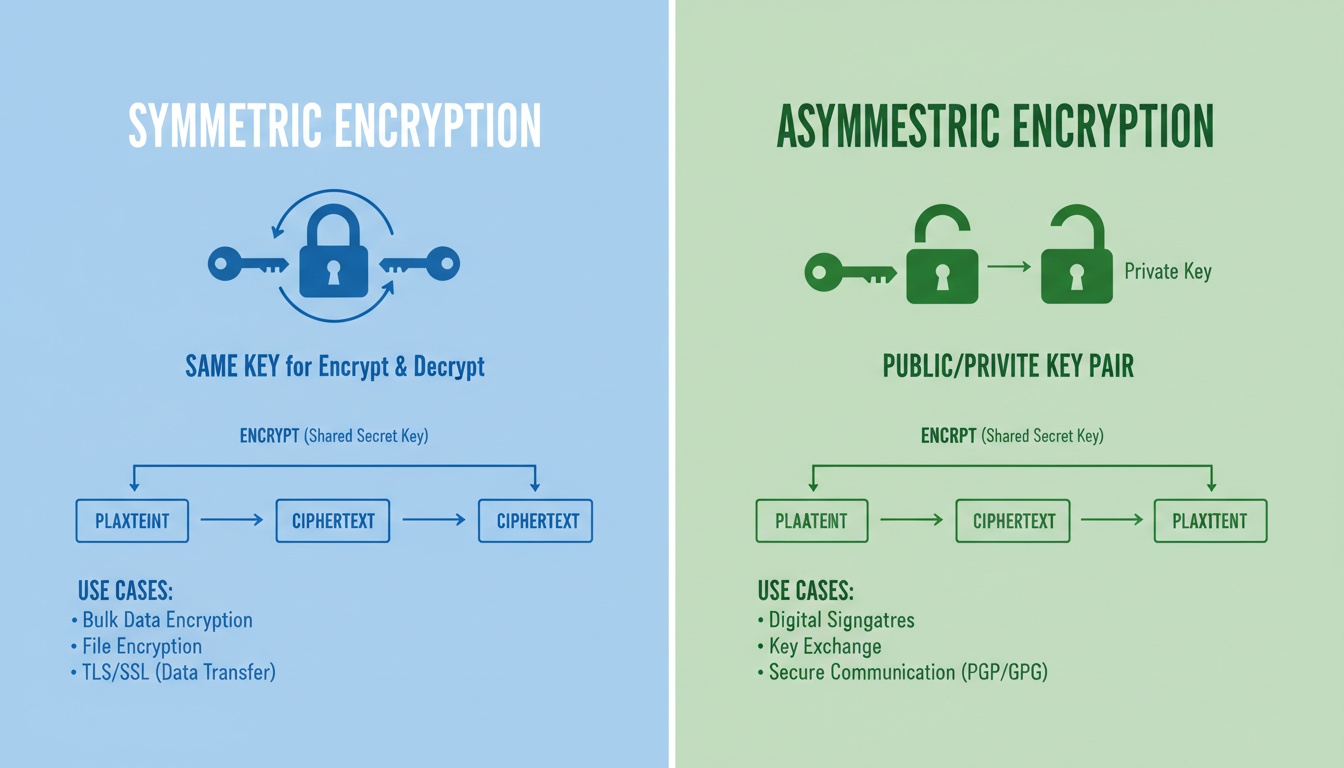
Encryption always relies on keys. In symmetric encryption, the same key is used to encrypt and decrypt. In asymmetric encryption, one key (public) is used to encrypt and a different key (private) is used to decrypt. In many systems, you encrypt and hash different pieces of data: for example, you encrypt tokens but hash passwords.
Types of Encryption
When people search for types of encryption, they are usually referring to how algorithms use keys and how they process data. Different types are used in different layers of systems and protocols.
| Type | Description | Example Algorithms |
|---|---|---|
| Symmetric Encryption | Same secret key used for both encryption and decryption | AES, DES, 3DES |
| Asymmetric Encryption | Uses a public/private key pair | RSA, ECC |
| Stream Encryption | Encrypts data one byte or bit at a time | ChaCha20, RC4 |
| Block Encryption | Encrypts data in fixed-size blocks | AES, Blowfish |
Symmetric ciphers like AES are often used for bulk data encryption because they are efficient. Asymmetric ciphers like RSA are used for key exchange and digital signatures, where properties like non-repudiation and public verification are important. Understanding these encryption types helps when deciding how to encrypt and hash data in the same architecture.
What is Hashing?
Hashing is a one-way process that takes an input (such as a password, file, or message) and produces a fixed-length string called a hash or message digest. The same input will always produce the same hash value, but you cannot feasibly reverse the hash to obtain the original input. The primary goals of hashing are integrity checking and authentication, not secrecy.
Because hashing is designed to be irreversible, it is not used to hide data that needs to be recovered later. Instead, it is used to verify that data has not been changed or to store sensitive values (like passwords) in a way that makes direct recovery extremely difficult for attackers. This is why “hashing vs encryption” is such an important distinction: hashing protects authenticity, while encryption protects confidentiality.
Hashing is one-way: it transforms data into a fixed-length value that cannot be practically reversed.
Key Properties of Hashing
| Property | Description |
|---|---|
| Purpose | Verify data integrity and authenticity |
| Direction | One-way only (no decryption step) |
| Output | Fixed-length hash value |
| Key Usage | No key required for basic hashing |
| Examples | SHA-256, MD5, SHA-512, Bcrypt, Argon2 |
A strong cryptographic hash algorithm in cryptography is designed to be collision-resistant (hard to find two different inputs that produce the same hash) and preimage-resistant (hard to find an input that matches a given hash). When people ask “what is a hash in cryptography?” or “what is hashing in cryptography?”, this is the core idea: a secure, one-way fingerprint of data.
Hashing in Cybersecurity
Hashing in cybersecurity is everywhere. It shows up in password storage, digital signatures, blockchain, and file verification. When you see terms like data hashing, secure hashing, or security hash, they are all referring to this same family of techniques.
Common uses of hashing include:
- Password storage in authentication systems
- Blockchain and distributed ledger data linking
- Digital signatures and certificates
- Data integrity checks for files and backups
- Software download verification using checksum vs hash values
In password storage, for example, the system stores only a hashed value of the password (often with a salt) instead of the password itself. When a user logs in, the system hashes the entered password and compares it to the stored hash to see if they match. This is why “hashing values” and “hashing in cyber security” are so important for identity and access management.
Encryption vs Hashing (Side-by-Side Comparison)
Although encryption and hashing both transform data, they do so for different reasons and with different properties. Mixing them up leads directly to mistakes like using encryption where hashing is needed, or treating a hash as if you can “decrypt” it. This section summarizes the difference between encryption and hashing and the difference between hash and encryption in one place.
| Feature | Encryption | Hashing |
|---|---|---|
| Purpose | Confidentiality (keep data secret) | Integrity and verification |
| Reversibility | Reversible with the correct key | Irreversible in practice |
| Keys Used | Yes (symmetric or asymmetric keys) | No key for basic hashing |
| Output Length | Variable, related to input size | Fixed length regardless of input size |
| Algorithms | AES, RSA, ChaCha20, DES | SHA-256, SHA-512, MD5, Bcrypt, Argon2 |
| Typical Use | Protecting data at rest/in transit | Passwords, checksums, integrity checks |
In short: encrypt vs hash comes down to what you need. Encryption aims to hide data but allow recovery, while hashing aims to detect changes and avoid recovery altogether. This is the core diff between hashing and encryption that security professionals care about.
Is Hashing Encryption?
No. Hashing is not encryption, even though both use mathematical transformations and produce “scrambled” output. The most important distinction in hashing vs encryption is reversibility: encryption must be reversible (with the correct key), whereas hashing is deliberately designed to be one-way.
Some people casually refer to hashing as “one-way encryption” or “hash encryption,” but from a cryptographic perspective that is inaccurate. Saying something is encrypted implies that it can be decrypted later, and that simply does not apply to secure hash functions.
| Feature | Hashing | Encryption |
|---|---|---|
| One-way or two-way | One-way hashing | Two-way encryption |
| Can be decrypted? | No, not in practice | Yes, with the correct key |
| Primary Purpose | Validation and integrity | Secrecy and confidentiality |
Understanding this difference between hashing and encryption helps prevent design errors such as trying to “decrypt” a hash or using hashing where actual confidentiality is required.
Can Hashes Be Decrypted?
From a design standpoint, hashes are not meant to be decrypted. Cryptographic hashing algorithms are intentionally built so that given a hash output, finding the original input is computationally infeasible. However, attackers sometimes try to “reverse” hashes using indirect methods that search for inputs which produce the same hash value.
Common techniques include:
- Rainbow tables: Precomputed databases of hash → input pairs for common passwords.
- Brute-force attacks: Trying huge numbers of candidate inputs until a matching hash is found.
- Dictionary attacks: Using large wordlists and variations (like “Password1!”) to find matches.
These methods do not actually perform decryption hash or true hashing decryption. Instead, they guess inputs until they find one that produces the same hash. If the underlying password is weak or unsalted, this guessing can be very effective, which is why secure hashing and salting are so important.
Why Decrypting a Hash Is Not Possible in Principle
A properly designed cryptographic hash function is:
- A one-way mathematical function with no inverse function exposed.
- Not based on a secret key that can be reversed.
- Many-to-one: multiple different inputs may produce the same hash (collisions), so there is no unique “original message” to recover.
Because of these properties, the only practical “way back” to a matching input is guessing and checking, which becomes infeasible if strong passwords, good hash algorithms, and slow, secure hashing strategies are used.
Salting and Hashing – Extra Security
To make hash-based storage more resistant to attacks like rainbow tables and large-scale guessing, security professionals add a random value called a salt before hashing. Each user or record gets a unique salt, and the salt is stored alongside the hash. This is a standard part of modern encryption and hashing strategies for credentials.
Example:
Password: “123456” Salt: “@XyQ!” Hashed value: SHA256(“123456@XyQ!”)
text
With salting:
- Two users with the same password will have different stored hashes.
- Precomputed rainbow tables become ineffective because they do not include the unique salts.
- Attackers must brute-force each hash individually, which greatly increases the work required.
Modern password hashing schemes like Bcrypt, Argon2, PBKDF2, and scrypt also add key stretching (making hashing deliberately slow) so that large-scale guessing attacks become much more expensive. When people compare salting vs hashing or tokenization vs hashing, salting is all about strengthening the underlying hash.
AES vs SHA: Which Is Better?
AES vs SHA (or SHA vs AES) is a very common search, but it is slightly misleading. AES is a symmetric encryption algorithm, while SHA (such as SHA-256) is a family of hashing algorithms. Asking “AES vs SHA which is better?” only makes sense once you understand that encryption and hashing solve different problems.
| Feature | AES (Encryption) | SHA (Hashing) |
|---|---|---|
| Type | Symmetric encryption algorithm | Cryptographic hash algorithm |
| Purpose | Data confidentiality | Data integrity and verification |
| Reversible | Yes, with the correct key | No, not reversible in practice |
| Common Use | File, database, and network encryption | Password storage, checksums, signatures |
AES is used when you need to hide data but later read it again (for example, encrypting a disk or securing HTTPS traffic). SHA-256 or similar secure hashing algorithms are used when you need to verify that data has not changed or to securely store a representation of sensitive values like passwords. So AES vs SHA is not about “better” overall, but about choosing the right tool for confidentiality (AES) or integrity (SHA).
Use Cases: Encryption vs Hashing
Choosing between encryption hashing techniques depends entirely on what you want to achieve. In many systems, they are used together, each handling a different part of the security requirement. This is where the practical meaning of hashing and the meaning of encryption come together.
| Scenario | Recommended Technique |
|---|---|
| Password protection | Hashing with salt (Bcrypt, Argon2, PBKDF2) |
| File or disk security | Encryption (e.g., AES-based full disk encryption) |
| Email, VPN, HTTPS (SSL/TLS) | Encryption for data in transit |
| Blockchain / ledger linking | Hashing (block hashes, transaction IDs) |
| Software file download verification | Hashing (publish expected hash for comparison) |
| Tokenization vs hashing | Tokenization stores replaceable values; hashing stores irreversible values |
| Digital signatures | Hashing plus encryption / public-key cryptography |
A good rule of thumb:
- Use encryption when you need to read the data again later.
- Use hashing when you only need to verify that data is correct or unchanged, not to recover the original value.
This is the practical answer to “what does hashing do?”, “what does hashing mean?”, and “what is hashing in cybersecurity?” that security professionals rely on every day.
Frequently Asked Questions (FAQs)
What does hashing do?
Hashing converts data of any length into a fixed-length, seemingly random value that can be used to verify integrity or identity without revealing the original data. It is the backbone of secure hash storage and many hash types used in modern systems.
What is hashing in cybersecurity?
In cybersecurity, hashing is used to ensure that messages, files, and credentials have not been altered. It underpins password storage, digital signatures, certificate validation, and integrity checks in many protocols, and is a key part of computer science hashing and cryptography hashing topics.
What is a hash in cryptography?
A hash is the output produced by a cryptographic hashing algorithm. It acts like a fingerprint for the input: small changes to the input produce completely different hashes. When you see “what is a hash algorithm” or “hashes in cryptography,” this is what they refer to.
What is one-way encryption?
People sometimes use the phrase “one-way encryption” or “1 way encryption” to describe hashing, but strictly speaking hashing is not encryption. True encryption is always reversible with the correct key, whereas hashing is designed to be a one-way hash or one-way hashing function only.
Is hashing safe for passwords?
Yes, hashing is the standard method for storing passwords safely when combined with unique salts and slow, modern hashing algorithms like Argon2, Bcrypt, PBKDF2, or scrypt. These techniques make offline password cracking significantly harder and are considered best practice for secure hashing in cyber security.
Can encryption replace hashing?
No. Encryption protects data confidentiality, while hashing protects data integrity and authenticity. Using only encryption for things like password storage leaves you exposed if keys are compromised, whereas hashing is designed to avoid direct recovery of the original value. The difference between hash and encryption here is critical.
Conclusion
Encryption and hashing are both foundational tools in cryptography, but they solve different problems and should not be used interchangeably. Encryption is a reversible, key-based process that protects the confidentiality of data, while hashing is a one-way transformation that provides integrity and verification without revealing the original information.
Designing secure systems means understanding the difference between encryption and hashing, when to encrypt and hash, and how to combine both alongside practices like salting and key management. Once you clearly separate “keeping data secret” (encryption) from “proving data has not changed” (hashing), it becomes much easier to choose the right mechanism for each part of your application or infrastructure.
Need help implementing secure hashing and encryption?
Contact our cryptography experts