Introduction
Transport Layer Security (TLS) is the backbone of secure communication across the internet. Every login, payment, API call, and enterprise workflow relies on TLS to protect data from interception and tampering.
In 2025, TLS is more critical than ever. With evolving threats, post-quantum risks, new CA/B Forum certificate validity rules, and cloud-native architectures depending on encrypted communication, organizations must understand TLS deeply—not just enable HTTPS and assume it is “done.”
This guide explains TLS encryption from the ground up: history, handshake flow, cipher suites, TLS 1.3 improvements, OSI layer placement, vulnerabilities, best practices, and future-ready recommendations.
What This Guide Covers
- TLS encryption explained in simple, modern terms
- TLS vs SSL, TLS version history, OSI layer placement
- Cryptographic foundations: authentication, encryption, integrity
- TLS handshake (TLS 1.2 vs TLS 1.3)
- Cipher suites & security guarantees
- Post-quantum cryptography (PQC) and hybrid key exchanges
- TLS certificate validity changes (47-day rule)
- Best practices & common pitfalls
- SEMrush keyword integration (tls tls, standard encryption tls, ssl tls encryption, etc.)
Workflow Diagram (TLS Encryption Overview)
TLS secures communication between a client and server through authentication, key exchange, encryption, and integrity protection.
1. What Is TLS Encryption?
TLS (Transport Layer Security) is a cryptographic protocol used to secure data exchanged between networked systems. It ensures that the data you send—whether login credentials, API payloads, financial information, or personal identity data—cannot be intercepted, modified, or forged.
TLS Provides Three Core Guarantees
- Encryption — Prevents unauthorized access to data.
- Authentication — Confirms the identity of the server (and optionally the client).
- Integrity — Ensures data isn’t modified during transmission.
TLS Solves These Problems
- Eavesdropping on network traffic
- Man-in-the-middle (MITM) attacks
- Session hijacking
- Data tampering
- API spoofing & impersonation
Who Uses TLS?
- Browsers accessing HTTPS sites
- Mobile apps calling backend APIs
- Email (SMTP, IMAP, POP3)
- VPNs (SSL VPNs)
- VoIP & messaging systems
- Zero-trust microservices
- IoT and industrial devices
2. Why TLS Encryption Matters Today
Modern organizations depend on TLS for:
1. Cybersecurity protection
TLS prevents interception and manipulation of sensitive data.
2. Cloud-native architectures
Every Kubernetes microservice, API gateway, and service mesh relies on TLS (often mTLS).
3. Identity and Access
TLS certificates act as identity documents for servers, services, and IoT devices.
4. Compliance requirements
TLS is required by:
- PCI DSS
- HIPAA
- GDPR
- SOC 2
- GLBA
5. Zero-trust security
TLS is foundational for identity-driven network access.
6. Scalability in distributed systems
Without modern TLS optimization (TLS 1.3, session resumption), large architectures suffer latency issues.
Authoritative References
3. How TLS Works (Technical Deep Dive)
TLS encryption relies on several components:
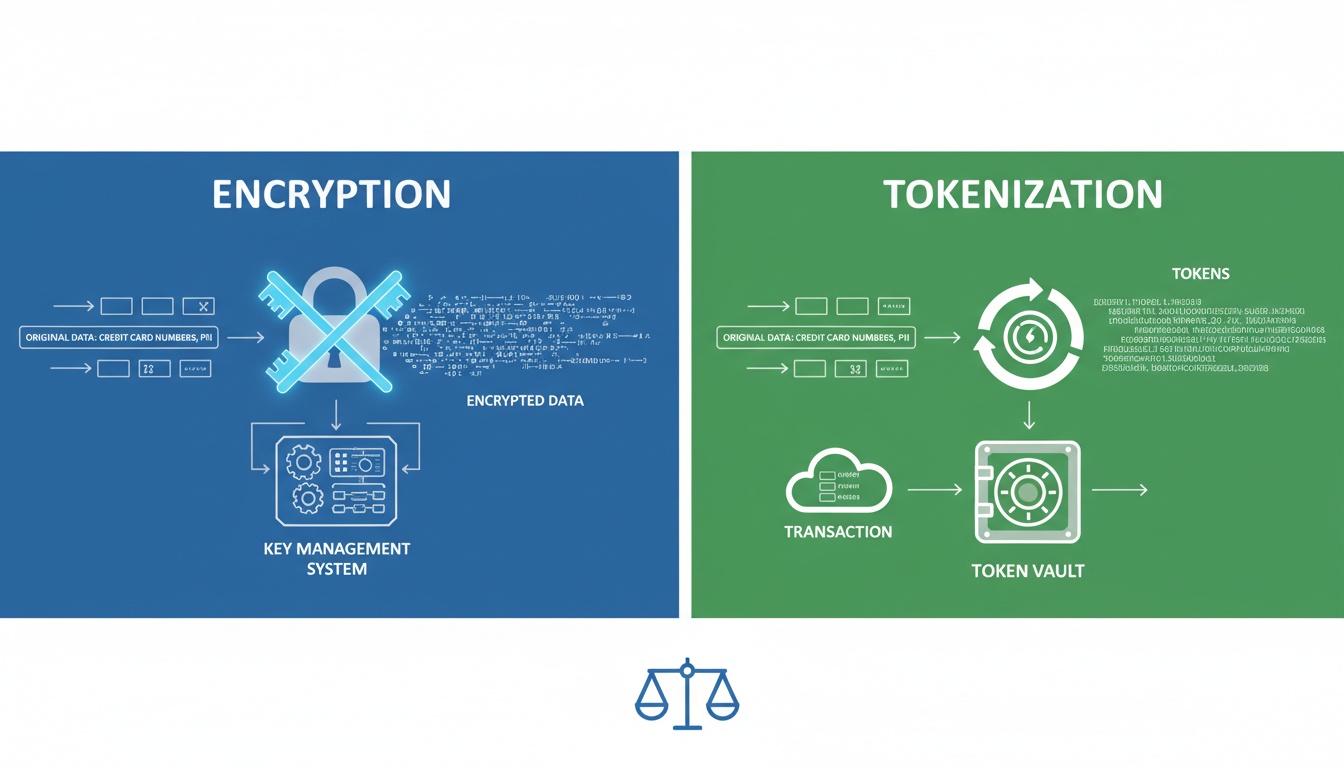
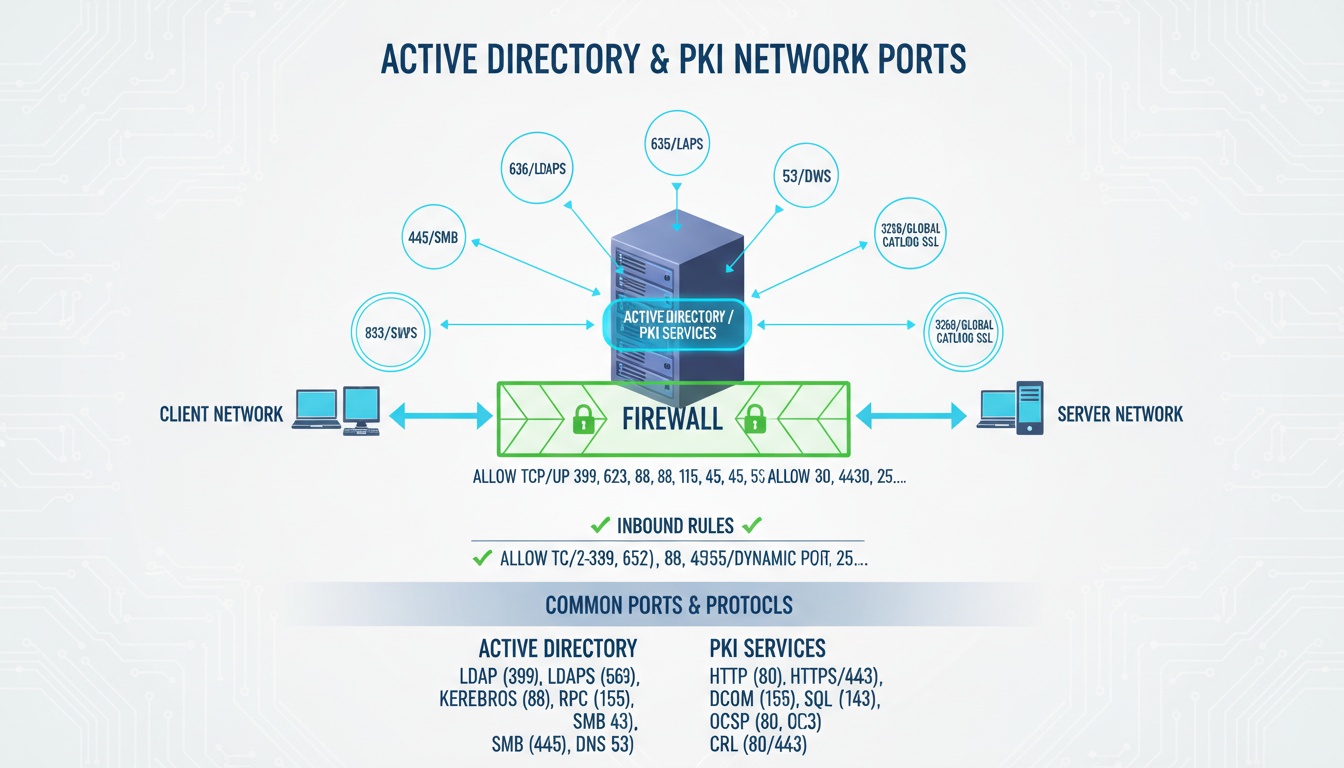
Component 1 — Certificates & Authentication
- A server presents its X.509 certificate.
- Browser verifies it against trusted root CAs.
- TLS supports RSA, ECDSA, and post-quantum candidates.
Used for:
- Server identity
- mTLS client authentication
- API identity verification
Component 2 — Key Exchange
TLS establishes a shared session key using:
- ECDHE (Elliptic Curve Diffie-Hellman Ephemeral)
- DHE
- Hybrid post-quantum + classical exchanges (Kyber + ECDHE)
Purpose:
- Perfect Forward Secrecy (PFS)
- Protection even if long-term keys are compromised
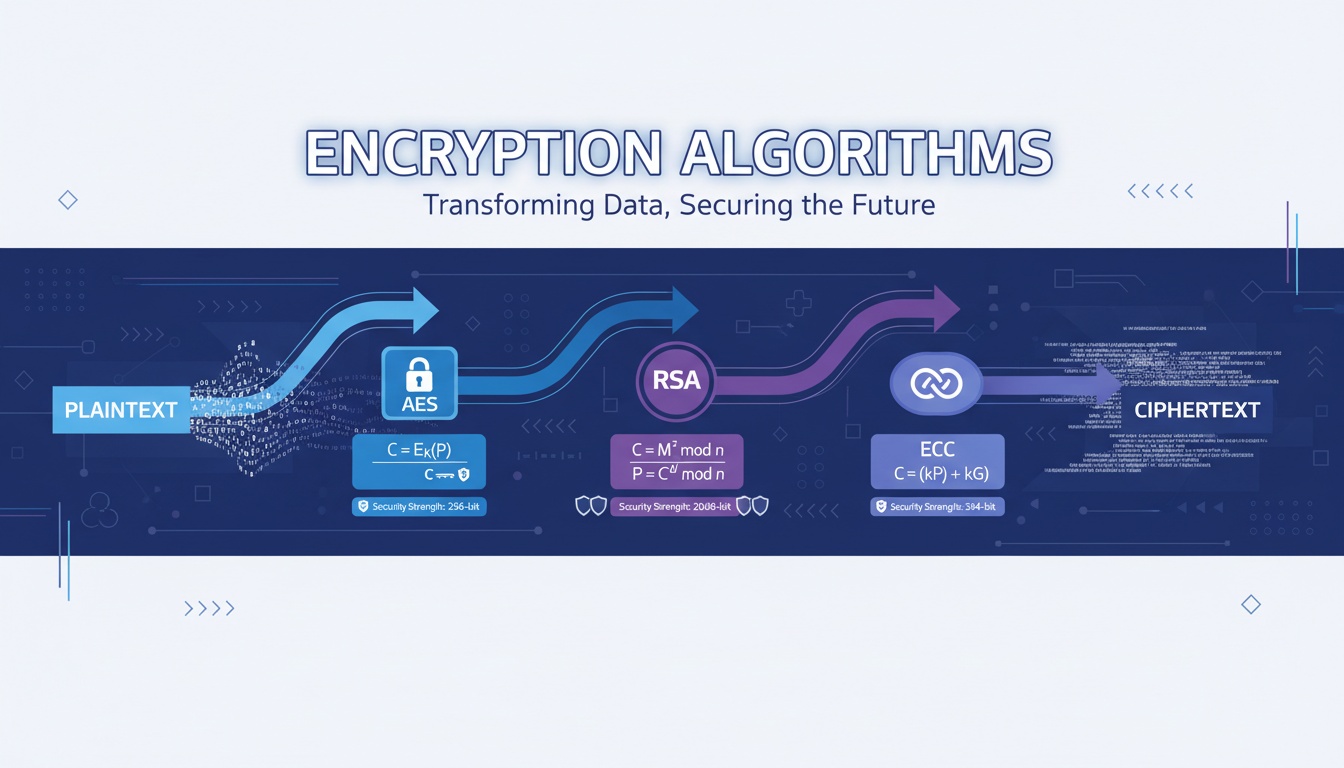
Component 3 — Encryption Algorithms
Common TLS algorithms:
- AES-256-GCM
- ChaCha20-Poly1305
Used for fast, secure symmetric encryption of payloads.
Component 4 — Integrity (HMAC / AEAD)
- SHA-256, SHA-384
- Part of AEAD modes in modern cipher suites
Ensures data cannot be modified silently.
4. Architecture Workflow (Step-by-Step)
TLS 1.2 Handshake
- ClientHello → cipher suites, TLS version, random values
- ServerHello → picks cipher suite, sends certificate
- Certificate validation → CA trust chain
- Key exchange → RSA/ECDHE
- Session key generated
- Encrypted communication begins
TLS 1.3 Handshake (Optimized)
- ClientHello (supported TLS versions + key share)
- ServerHello (selected key share + certificate)
- Encrypted handshake messages
- 0-RTT resumption possible
- Secure tunnel established
ASCII Diagram
Client Server
|----- ClientHello --------->|
|<---- ServerHello ----------|
|<---- Certificate ----------|
|----- Finished ------------>|
|<---- Finished -------------|
|=== Encrypted Channel ======|5. Real Code Snippets (Required)
Check TLS Version Supported by a Server
openssl s_client -connect example.com:443 -tls1_3View Certificate Details
openssl x509 -in certificate.pem -text -nooutMinimal TLS Client in Python
import ssl, socket
context = ssl.create_default_context()
conn = context.wrap_socket(socket.socket(), server_hostname="example.com")
conn.connect(("example.com", 443))
print(conn.version())cert-manager TLS Certificate YAML
apiVersion: cert-manager.io/v1
kind: Certificate
metadata:
name: app-tls
spec:
secretName: app-tls-secret
issuerRef:
name: letsencrypt
kind: ClusterIssuer
dnsNames:
- app.example.com6. Best Practices (2025)
- Always use TLS 1.3 for public-facing systems.
- Disable SSL, TLS 1.0, TLS 1.1, and weak cipher suites.
- Use ECDHE or Hybrid PQC key exchanges.
- Enforce Perfect Forward Secrecy (PFS).
- Enable OCSP stapling.
- Automate certificate renewals (ACME, CLM platforms).
- Use HSM/KMS for private key storage.
- Monitor TLS visibility into east-west traffic.
- Implement mTLS for internal microservices.
- Validate certificate chains regularly.
- Log all certificate issuance & revocation events.
- Hard-fail invalid certificates (no silent fallback).
- Adopt PQC readiness roadmap.
- Follow CA/B Forum 47-day validity timeline.
7. Common Pitfalls
- Using outdated TLS versions (1.0 / 1.1).
- Accepting deprecated cipher suites (RC4, DES, MD5, SHA-1).
- Self-signed certificates in production.
- Not automating renewals → cert outages.
- Incorrect server SNI configuration.
- Missing intermediate certificates.
- Using RSA-1024 or RSA-2048 without forward secrecy.
- No visibility into internal mTLS traffic.
8. Advanced Use Cases
- TLS for zero-trust service-to-service communication.
- TLS inside Kubernetes service mesh (Istio, Linkerd).
- TLS offloading via reverse proxies.
- IoT TLS authentication at scale.
- TLS visibility solutions for encrypted traffic monitoring.
- PQC hybrid key exchange for quantum resistance.
- Automated DevOps TLS pipelines in CI/CD.
9. Keyword Expansion Zone (SEMrush Integration)
- tls tls — integrated in version history & handshake details
- standard encryption tls — covered in cipher suite & algorithm sections
- encryption standard tls — explained in TLS 1.2 vs 1.3
- ssl tls encryption — differentiation included in intro
- what is tls encryption — explained in Section 1
- tls cybersecurity — Section 2 context
- osi tls / ssl osi model — highlighted at Layer 4 / Layer 7
- how tls certificates work — included in authentication section
- tls best practices — Section 6
- transport layer security encryption — integrated across core sections
- tls encryption meaning — explained in opening definition
- versions of ssl / ssl tls history — detailed version timeline
- rfc for tls 1.2 — referenced in external resources
- standard encryption tls meaning — clarified in best practices
- ssl/tls encryption — covered end-to-end
Comparison Table (TLS 1.2 vs TLS 1.3)
| Feature | TLS 1.2 | TLS 1.3 |
|---|---|---|
| Handshake | Multi-round | 1-RTT / 0-RTT |
| Cipher Suites | Many, including weak ones | Only strong modern suites |
| Key Exchange | RSA, ECDHE | ECDHE or Hybrid PQC |
| Performance | Slower | Faster |
| Security | Depends on configuration | Secure-by-default |
External Resources
- https://www.nist.gov
- https://www.cisa.gov
- https://www.cloudflare.com/learning/security/tls
- https://learn.microsoft.com/security
- https://www.rfc-editor.org
Book a Demo
Looking to implement secure, scalable certificate lifecycle automation across your enterprise? Qcecuring helps you modernize PKI, SSH, SSL, and code signing workflows with cloud-native automation.
Book a Demo: https://www.qcecuring.com/request-demo
Final Summary
- TLS encrypts data, authenticates identities, and ensures integrity.
- TLS 1.3 is faster, safer, and simplifies crypto choices.
- Cipher suites define how key exchange, encryption, and integrity work.
- Post-quantum migration is becoming essential for long-term security.
- Automated certificate lifecycle management is mandatory for 2025+ architectures.