Difference Between Symmetric and Asymmetric Encryption
Encryption is the foundation of modern cybersecurity. Whether you’re protecting files, databases, APIs, mobile apps, or cloud workloads—two core techniques make this possible:
** Symmetric Encryption**
** Asymmetric Encryption**
Both serve the same purpose (data protection), but they work very differently.
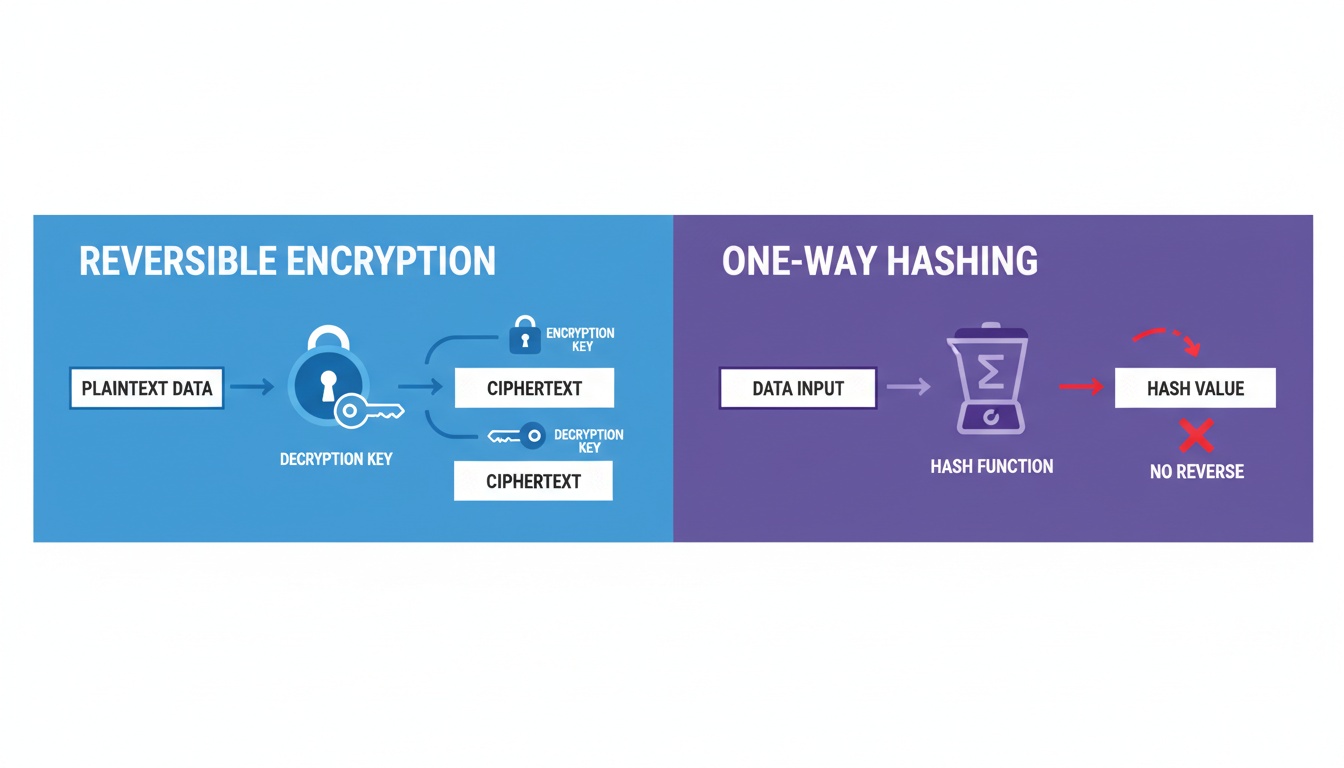
1. What Is Encryption?
Encryption converts readable data (plaintext) into unreadable data (ciphertext) using cryptographic algorithms.
It ensures:
- Confidentiality – only authorized users can read the data
- Integrity – data cannot be altered silently
- Authentication – verifying identity of sender/receiver
- Non-repudiation (via digital signatures)
There are two main types of encryption:
- Symmetric Encryption — one key
- Asymmetric Encryption — two keys
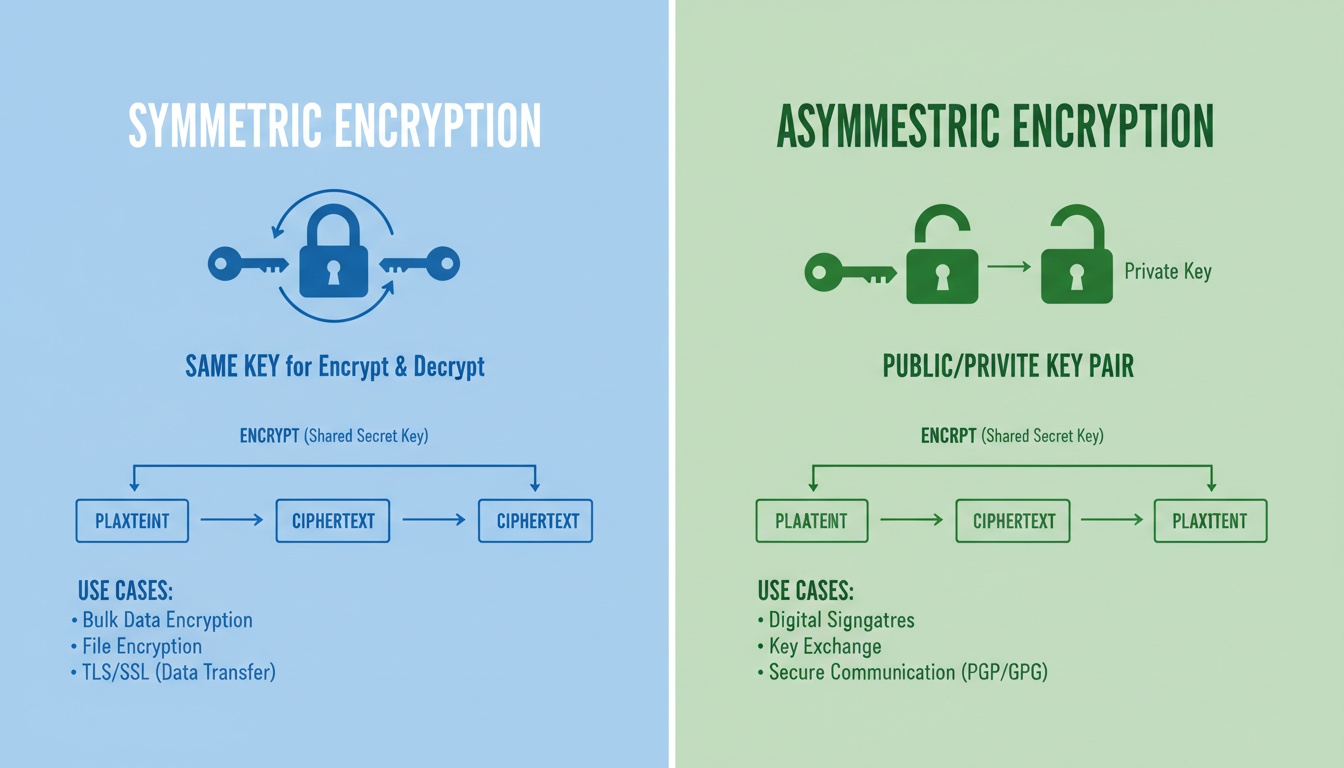
2. What Is Symmetric Key Encryption?
Symmetric encryption uses a single secret key for both encrypting and decrypting data.
It is extremely fast, efficient, and ideal for handling large volumes of data.
Key Characteristics
- Uses one secret key
- High performance (very fast)
- Low resource usage
- Needs a secure way to distribute the key
- Ideal for encrypting large amounts of data
Common Symmetric Encryption Algorithms
- AES (AES-128, AES-192, AES-256)
- DES / 3DES
- Blowfish / Twofish
- ChaCha20
- RC4 (deprecated)
Common Use Cases
- File encryption
- Disk encryption (BitLocker, FileVault, LUKS)
- VPNs
- Database encryption
- Mobile & IoT devices
- TLS session encryption
Is AES symmetric or asymmetric?
AES is a symmetric encryption algorithm.
Mathematical Representation
Ciphertext = E(K, P)
Plaintext = D(K, Ciphertext)Where:
- K = one shared key
- P = plaintext
- E/D = encryption/decryption
3. What Is Asymmetric Key Encryption?
Asymmetric encryption uses two mathematically linked keys:
- Public Key (Ke) – used to encrypt
- Private Key (Kd) – used to decrypt
The private key stays secret, while the public key can be shared with anyone.
Key Characteristics
- Uses a public + private key pair
- More secure, but slower
- Eliminates need for sharing secret keys
- Enables digital signatures and identity verification
- Ideal for secure communication and key exchange
Common Asymmetric Algorithms
- RSA
- ECC (Elliptic Curve Cryptography)
- DSA / ECDSA
- ElGamal
- Diffie–Hellman (key exchange)
Common Use Cases
- HTTPS/SSL/TLS
- SSH authentication
- Secure email (PGP/GPG)
- Digital signatures
- Blockchain wallets
- Certificate Authorities (PKI)
Is RSA symmetric or asymmetric?
RSA is an asymmetric encryption algorithm.
Mathematical Representation
Ciphertext = E(Ke, P)
Plaintext = D(Kd, Ciphertext)Where:
- Ke = public (encryption) key
- Kd = private (decryption) key
- P = plaintext
4. Symmetric vs Asymmetric Encryption — Easy Comparison Table
| Factor | Symmetric Encryption | Asymmetric Encryption |
|---|---|---|
| Keys Used | One secret key | Public + private key |
| Speed | Very fast | Slower |
| Security | Secure but key sharing is risky | Higher (no shared private key) |
| Ciphertext Size | Same or near plaintext size | Larger than plaintext |
| Key Length | 128–256 bits | 2048+ bits (RSA), 256-bit (ECC) |
| Resource Usage | Low | High |
| Used For | Large data encryption | Authentication, signatures, key exchange |
| Provides | Confidentiality | Confidentiality + authenticity + non-repudiation |
| Algorithms | AES, DES, RC4 | RSA, ECC, DH |
| Data Handling | Efficient for large data | Less efficient, small data chunks |
| Security Model | Shared key risk | Strong trust model (public/private) |
5. How Symmetric Encryption Works (Step-by-Step)
- A secret key is generated.
- Sender encrypts data using the secret key.
- Receiver decrypts data using the same secret key.
- Key must be kept secret and securely exchanged.
Biggest challenge → securely sharing the key.
6. How Asymmetric Encryption Works (Step-by-Step)
- Receiver shares public key openly.
- Sender encrypts message using the public key.
- Receiver decrypts using private key.
- Private key never leaves the device → high security.
Digital Signature Flow
- Sender signs data using their private key.
- Receiver verifies signature with the public key.
This ensures:
- Authenticity
- Integrity
- Non-repudiation
7. Hybrid Encryption (Used in TLS/HTTPS)
Most modern systems combine both methods:
- Asymmetric encryption is used to securely exchange a symmetric key.
- Symmetric encryption handles the actual data (fast & efficient).
This hybrid model powers:
- HTTPS/TLS
- Messaging apps
- Secure file-sharing platforms
- Enterprise identity systems
8. When to Use Symmetric vs Asymmetric Encryption
Choose Symmetric Encryption When:
- Speed is a priority
- Encrypting large amounts of data
- Devices have limited resources
- Example: storage encryption, VPN tunnels, databases
Choose Asymmetric Encryption When:
- Secure key exchange is required
- Digital signatures are needed
- Authentication is important
- Example: certificates, PKI, HTTPS, SSH
Best Modern Approach (2025)
Use asymmetric to exchange keys → symmetric to encrypt data.
9. Real-World Examples
Examples of Symmetric Encryption
- AES-256 for VPN tunnels
- File encryption tools
- Disk-level encryption systems
- Cloud storage encryption
- Messaging apps (session keys)
Examples of Asymmetric Encryption
- RSA certificates in HTTPS
- SSH public keys
- Blockchain private keys
- Code signing certificates
- Secure email encryption (PGP)
10. Frequently Asked Questions
Is AES symmetric or asymmetric?
AES is symmetric.
Is RSA symmetric or asymmetric?
RSA is asymmetric.
Why is asymmetric encryption slower?
It uses complex mathematical operations involving very large numbers.
Which encryption is more secure?
- Symmetric → extremely secure for data
- Asymmetric → secure for identity & key management
Do modern systems use both?
Yes — almost all secure systems use a hybrid model.
11. Summary
- Symmetric encryption uses one key, is fast, and ideal for large data.
- Asymmetric encryption uses two keys, adds identity & trust, and secures communication.
- Hybrid encryption combines both and is used in HTTPS/TLS.
- Choosing the right method depends on your performance and security needs.
12. Book a Demo (CTA)
Want to secure your organization with modern encryption, PKI automation, and zero-downtime certificate lifecycle management?
QCeCuring helps teams deploy enterprise-grade cryptography and automate TLS certificates across all environments.
Book a Demo: https://www.qcecuring.com/request-demo