Opening Section
AES (Advanced Encryption Standard) is the most widely deployed symmetric encryption algorithm in the world. It protects data inside web traffic, mobile applications, Wi-Fi networks, cloud workloads, and government systems. Its speed, security guarantees, and hardware acceleration support make it the global standard for protecting sensitive information.
This guide provides a clear, modern, fully original explanation of what AES is, how the algorithm works internally, why enterprises depend on it, and how it fits into cloud-native architectures, zero-trust environments, and modern cybersecurity strategies.
What This Guide Covers
- Simple, accurate definition of AES
- AES vs. Rijndael explained
- Internal AES operations — SubBytes, ShiftRows, MixColumns, AddRoundKey
- Key lengths, block sizes, and round structure
- AES modes of operation (CBC, GCM, CFB, OFB)
- Architecture workflow for AES encryption
- Real code examples (Python, OpenSSL)
- Best practices and common pitfalls
- Enterprise use cases across cloud, IoT, and networking
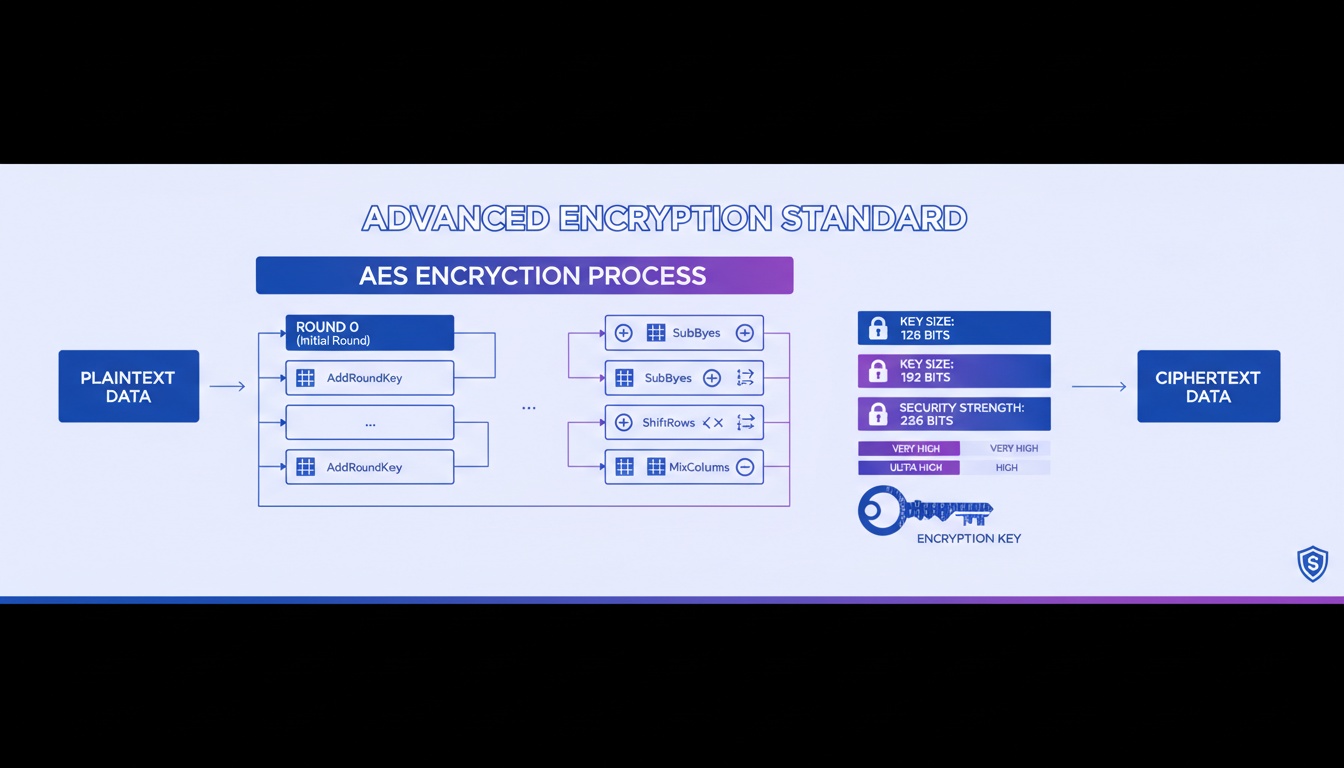
Workflow Diagram (AI-Generated)
Alt-text: Workflow diagram for AES encryption
1. What Is AES Encryption?
AES is a symmetric block cipher standardized by NIST that encrypts data in fixed 128-bit blocks. It supports key sizes of 128, 192, or 256 bits, and is designed to be secure, efficient, and hardware-accelerated.
AES solves the core problem of protecting digital information at rest and in transit. It is implemented globally in:
- TLS and HTTPS
- VPN protocols
- Wi-Fi (WPA2, WPA3)
- Mobile devices
- Cloud storage systems
- Operating system file encryption
- Government and military communication
Organizations rely on AES when they require confidentiality, performance, and compliance with modern security standards.
2. Why AES Matters Today
AES plays a foundational role in modern security due to its combination of performance, strength, and universal platform support.
Key reasons:
- Essential for cloud-native applications and microservices
- Required for zero-trust network architectures
- Standard component of identity and access systems
- Used in compliance frameworks (NIST, ISO, HIPAA, PCI-DSS)
- Supported by CPUs via AES-NI for high-speed encryption
- Provides secure, low-latency encryption for distributed workloads
Authoritative References
- https://www.nist.gov
- https://www.cisa.gov
- https://www.cloudflare.com/learning/cryptography/aes-encryption/
3. How AES Works (Technical Deep Dive)
AES operates on a 4×4 byte matrix called the state. It transforms plaintext into ciphertext using a series of mathematical operations.
Core Components
SubBytes
A nonlinear substitution step using an S-box lookup table.
ShiftRows
Each row of the state is cyclically shifted left to increase diffusion.
MixColumns
Each column is mixed using linear transformations over a Galois Field.
(Not applied in the final round.)
AddRoundKey
State is XORed with a round key derived from the main AES key.
Round Structure
- AES-128 → 10 rounds
- AES-192 → 12 rounds
- AES-256 → 14 rounds
Encryption Process
- Initial AddRoundKey
- Repeated rounds: SubBytes → ShiftRows → MixColumns → AddRoundKey
- Final round omits MixColumns
- Ciphertext generated
4. Architecture Workflow (Step-by-Step)
- Plaintext split into 128-bit blocks
- Key schedule expands the secret key into round keys
- Initial AddRoundKey applied
- Each round transforms the state using AES operations
- Final round produces ciphertext
- Decryption performs the operations in reverse order
5. Real Code Snippets
Inspect AES Key Parameters (Python)
from cryptography.hazmat.primitives.ciphers import algorithms
cipher = algorithms.AES(b"0" * 32)
print(cipher.key_size)
print(cipher.block_size)AES-GCM Encryption (Python)
from cryptography.hazmat.primitives.ciphers.aead import AESGCM
import os
key = AESGCM.generate_key(bit_length=256)
aesgcm = AESGCM(key)
nonce = os.urandom(12)
ciphertext = aesgcm.encrypt(nonce, b"example data", None)OpenSSL — List AES Cipher Commands
openssl list -cipher-commands | grep aes6. Best Practices
- Prefer AES-256 for long-term data protection
- Use authenticated modes: AES-GCM or AES-CCM
- Avoid ECB mode completely
- Never reuse IVs in GCM
- Store keys in HSM or cloud KMS
- Rotate encryption keys periodically
- Enforce TLS 1.3 for network encryption
- Use secure random number generators
- Enable AES-NI hardware acceleration
- Avoid implementing AES manually
- Validate ciphertext authentication tags
- Integrate encryption into CI/CD pipelines
7. Common Pitfalls
- Using AES-ECB
- Reusing nonces or IVs
- Storing keys in plaintext
- Hardcoded keys in source code
- Weak key generation methods
- Incorrect padding schemes
- Not validating authentication tags
- Skipped key rotation policies
8. Advanced Use Cases
- Enterprise cloud KMS integrations
- Service mesh mTLS encryption workflows
- IoT device provisioning and firmware protection
- Large-scale data lake encryption
- CI/CD pipeline secret management
- Identity and access workflows
- On-device encryption for mobile systems
9. Keyword Expansion Zone
- aes algorithm internal working
- how does aes encryption work step by step
- aes 128 vs aes 256 for enterprises
- rijndael cipher explanation
- gcm vs cbc encryption modes
- symmetric encryption for cloud workloads
Comparison Table
| Feature | DES / 3DES | AES |
|---|---|---|
| Block Size | 64-bit | 128-bit |
| Security | Weak | Strong |
| Performance | Slow | Hardware-accelerated |
| Adoption | Legacy only | Global standard |
External Resources
- https://www.nist.gov
- https://cisa.gov
- https://www.cloudflare.com/learning
- https://learn.microsoft.com/security
- https://www.rfc-editor.org/rfc/rfc8446
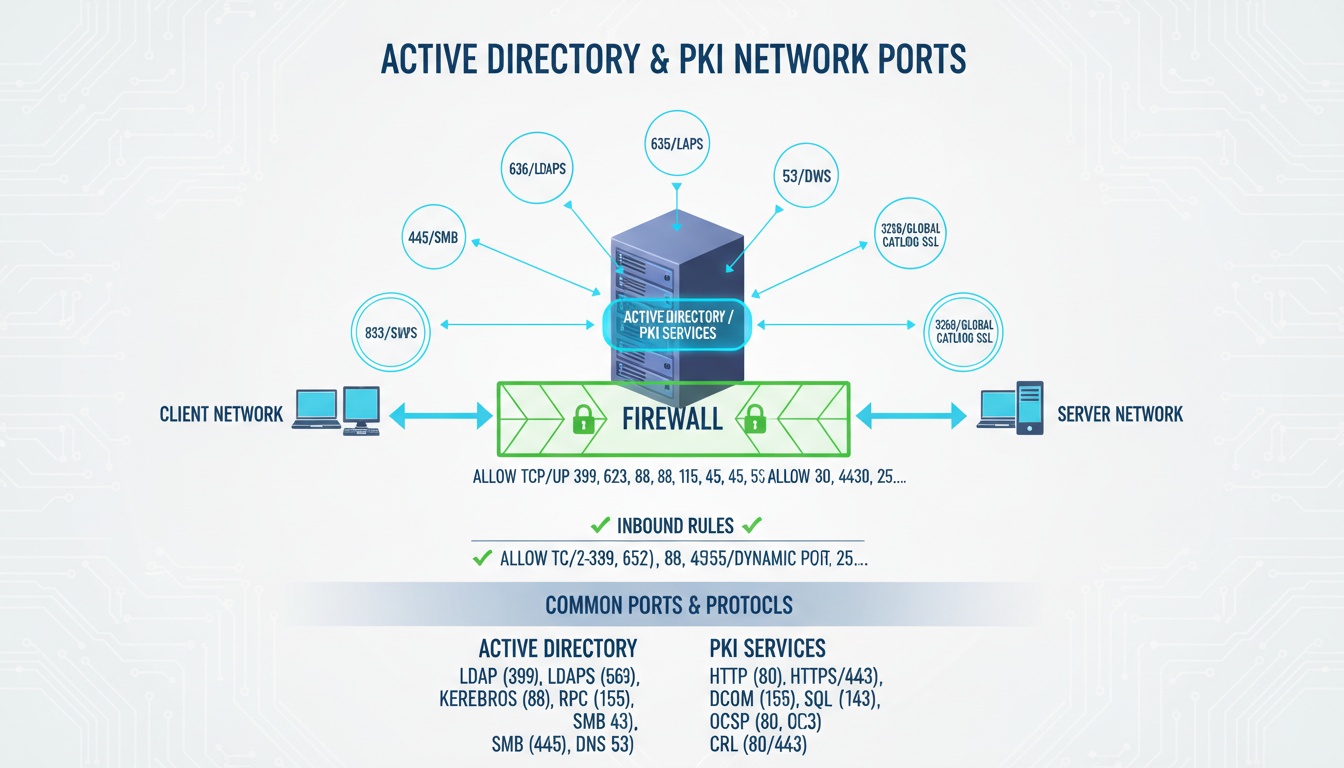
Looking to implement secure, scalable certificate lifecycle automation across your enterprise?
Qcecuring helps you modernize PKI, SSH, SSL, and code signing workflows with cloud-native automation.Book a Demo: https://www.qcecuring.com/request-demo
Final Summary
- AES is a symmetric block cipher designed for speed and security.
- It uses repeated rounds of substitution, shifting, mixing, and key addition.
- AES-GCM is the recommended modern encryption mode.
- AES protects cloud, network, enterprise, and IoT systems globally.
- Proper implementation and key management determine real-world security.