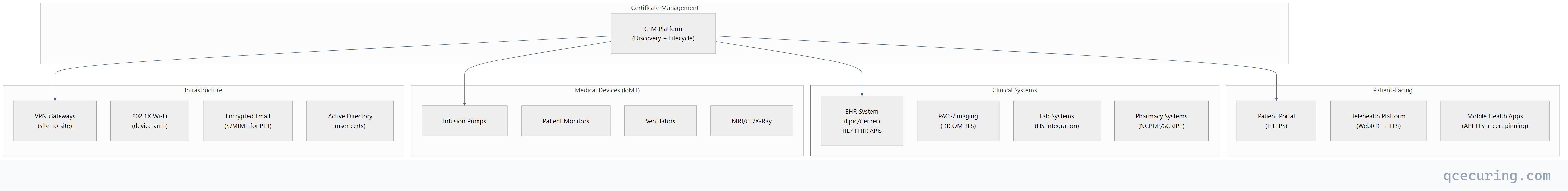
A hospital’s certificate infrastructure is uniquely complex. You have EHR systems (Epic, Cerner, MEDITECH) that need TLS for HL7 FHIR APIs. Medical devices — infusion pumps, imaging systems, patient monitors — that authenticate via certificates but can’t be easily updated. Patient portals handling PHI over HTTPS. Telehealth platforms with mTLS between providers. And all of it falls under HIPAA’s encryption requirements with audit trails that must survive a compliance investigation.
When a certificate expires on a patient portal, it’s not just a website outage — it’s a potential HIPAA violation and a disruption to patient care. When a medical device’s certificate expires, it may disconnect from the network entirely, with no remote renewal mechanism.
The Healthcare Certificate Landscape
Certificate Count by Hospital Size
| Hospital Size | Estimated Certificates | Key Challenge |
|---|---|---|
| Small (< 100 beds) | 200-500 | Manual tracking, no dedicated PKI staff |
| Medium (100-500 beds) | 500-2,000 | Mixed vendors, device sprawl |
| Large (500+ beds) | 2,000-10,000 | Multi-site, IoMT at scale, compliance |
| Health System (multi-hospital) | 10,000-50,000+ | Federated management, M&A integration |
HIPAA Encryption Requirements
HIPAA’s Security Rule (§164.312) classifies encryption as an “addressable” implementation specification — meaning you must implement it or document why an equivalent alternative is used. In practice, every healthcare organization encrypts PHI in transit.
What HIPAA Requires for Certificates
| Requirement | HIPAA Reference | Certificate Implication |
|---|---|---|
| Encryption of PHI in transit | §164.312(e)(1) | TLS certificates on all systems handling PHI |
| Access controls | §164.312(a)(1) | Client certificates for system-to-system auth |
| Audit controls | §164.312(b) | Certificate operations must be logged |
| Integrity controls | §164.312(c)(1) | Code signing for clinical software updates |
| Authentication | §164.312(d) | Certificate-based device identity |
Minimum TLS Configuration for HIPAA
# HIPAA-compliant TLS configuration (references NIST SP 800-52)
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers 'ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256';
ssl_prefer_server_ciphers on;
# Certificate must use:
# - RSA 2048+ or ECDSA P-256+
# - SHA-256+ signature algorithm
# - Valid chain to trusted CA
# - Matching SAN for the service hostnameMedical Device Certificate Challenges
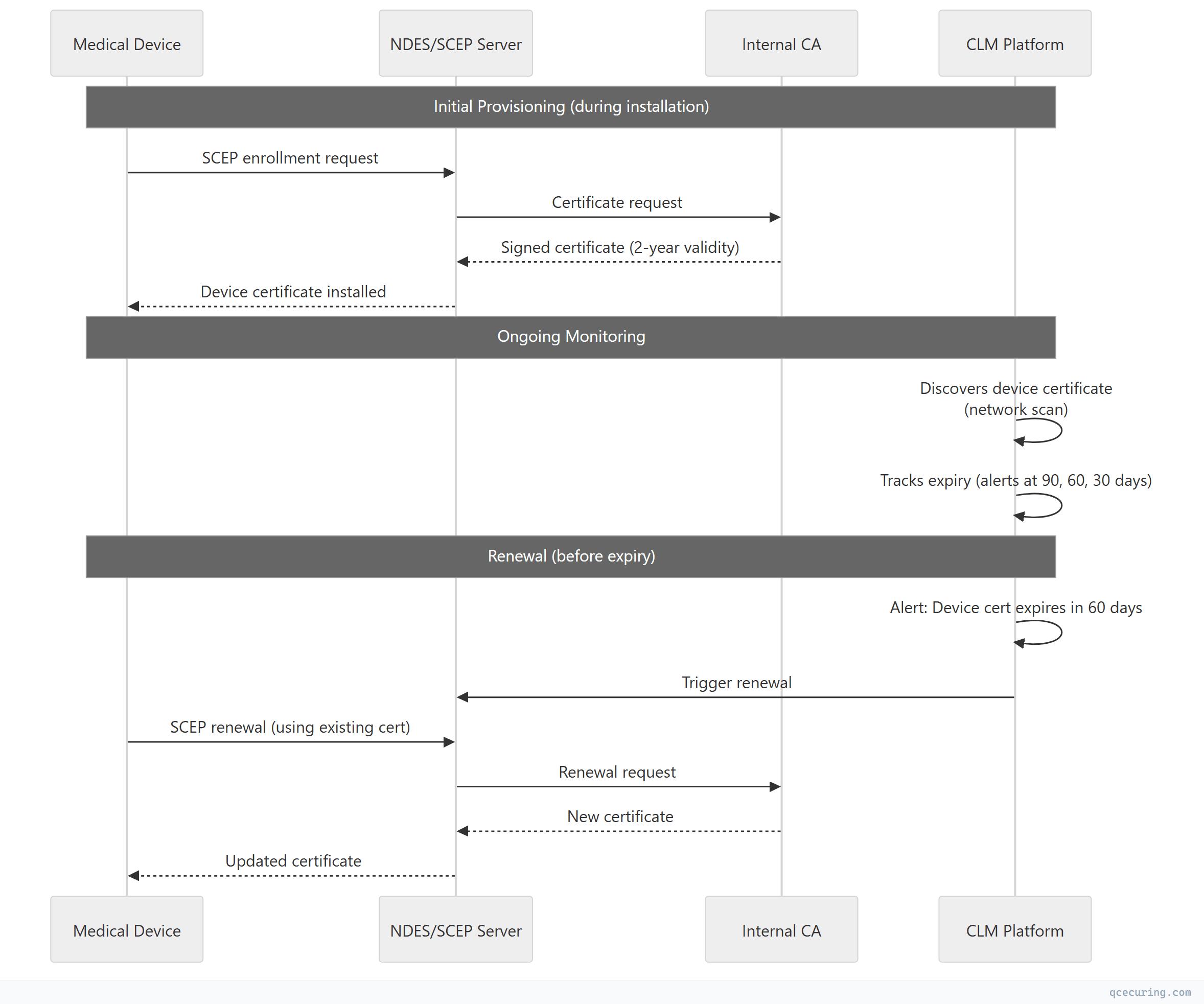
Medical devices (IoMT — Internet of Medical Things) present unique certificate management problems:
| Challenge | Why It’s Hard | Solution |
|---|---|---|
| Long device lifespan | 10-15 year devices outlive certificate validity | Automated renewal via SCEP/EST, or long-lived internal CA certs |
| No remote access | Devices on isolated VLANs, no internet | On-premises SCEP (NDES) or manual renewal during maintenance |
| FDA-regulated firmware | Can’t update crypto libraries easily | Plan certificate renewal separate from firmware updates |
| Resource-constrained | Limited CPU/memory for TLS | Use ECDSA (smaller keys, faster handshakes) |
| Vendor-managed | Hospital doesn’t control the device OS | Negotiate certificate management in procurement contracts |
| Network segmentation | Devices on isolated clinical networks | Deploy SCEP/EST endpoints within clinical VLANs |
Device Certificate Lifecycle
EHR System Integration
Epic Certificate Requirements
Epic systems use certificates for:
- MyChart patient portal (public TLS)
- Interconnect web services (mTLS between Epic instances)
- Care Everywhere health information exchange (mTLS)
- FHIR APIs (OAuth 2.0 + TLS)
- Hyperspace client connections (internal TLS)
Common Epic certificate issues:
- Interconnect certificates expire and break Care Everywhere connections
- MyChart certificate renewal requires coordination with Epic hosting
- FHIR API certificates need SANs for multiple endpoint URLs
HL7 FHIR API Security
# FHIR server TLS requirements
tls:
version: "1.2+"
client_auth: "required" # mTLS for system-to-system
certificate:
key_type: "ECDSA P-256"
validity: "1 year"
san:
- "fhir.hospital.org"
- "api.hospital.org"
eku:
- "serverAuth"
- "clientAuth" # For bidirectional FHIR exchangeSelecting a CLM Platform for Healthcare
Must-Have Features
| Feature | Why Healthcare Needs It |
|---|---|
| Certificate discovery | Find every cert across clinical and IT networks |
| Medical device support | SCEP/EST enrollment for IoMT devices |
| HIPAA audit trail | Immutable log of all certificate operations |
| Multi-CA support | Internal CA + public CA + device vendor CAs |
| Automated renewal | Prevent outages on 24/7 clinical systems |
| Network segmentation awareness | Discover certs across isolated clinical VLANs |
| Role-based access | Separate clinical engineering from IT security |
| Compliance reporting | HIPAA, HITRUST, SOC 2 evidence generation |
| Integration with ITSM | ServiceNow/Jira tickets for manual renewals |
| Downtime-free renewal | Rolling updates for HA clinical systems |
Evaluation Criteria
| Criterion | Weight | Questions to Ask |
|---|---|---|
| Discovery depth | High | Can it scan clinical VLANs? Does it find certs on medical devices? |
| Automation | High | Does it support SCEP/EST for devices? ACME for web servers? |
| Compliance | High | Does it generate HIPAA-ready audit reports? |
| Integration | Medium | Does it integrate with Epic/Cerner APIs? AD CS? |
| Scalability | Medium | Can it handle 10,000+ certificates across multiple sites? |
| Deployment | Medium | On-premises option? (some hospitals can’t use cloud) |
| Support | Medium | Healthcare-specific expertise? BAA available? |
Implementation Roadmap
Phase 1: Discovery (Weeks 1-4)
# Network-based certificate discovery across all VLANs
# Scan clinical network (10.10.0.0/16)
# Scan administrative network (10.20.0.0/16)
# Scan DMZ (192.168.1.0/24)
# Scan medical device VLAN (10.30.0.0/16)
# Expected findings:
# - Certificates you knew about (patient portal, EHR)
# - Certificates you forgot about (old test servers, vendor appliances)
# - Expired certificates still in use (medical devices, printers)
# - Self-signed certificates that should be CA-issuedPhase 2: Risk Assessment (Weeks 5-6)
| Priority | Criteria | Action |
|---|---|---|
| Critical | PHI-handling systems with certs expiring < 30 days | Immediate renewal |
| High | Patient-facing systems, EHR integrations | Automate renewal |
| Medium | Internal systems, non-PHI | Schedule renewal |
| Low | Development, test environments | Document and plan |
Phase 3: Automation (Weeks 7-12)
- Deploy ACME/Certbot for web servers (patient portal, APIs)
- Configure SCEP/NDES for medical devices
- Set up auto-enrollment via AD CS for Windows systems
- Integrate CLM platform with monitoring (alerts to on-call)
- Create runbooks for devices that can’t auto-renew
Phase 4: Compliance (Ongoing)
- Generate monthly certificate inventory reports
- Track crypto period compliance (NIST SP 800-57)
- Document all certificate operations for HIPAA audit trail
- Conduct quarterly reviews of certificate hygiene
Compliance and Audit
HIPAA Audit Evidence
| Auditor Question | Evidence from CLM |
|---|---|
| ”How do you encrypt PHI in transit?” | Certificate inventory showing TLS on all PHI systems |
| ”How do you manage encryption keys?” | Key lifecycle reports, rotation history |
| ”Who has access to certificates?” | RBAC logs, approval workflows |
| ”How do you prevent certificate expiry?” | Automated renewal reports, alert history |
| ”How do you handle compromised certificates?” | Revocation procedures, incident response logs |
HITRUST CSF Mapping
| HITRUST Control | Certificate Requirement |
|---|---|
| 09.s (Encryption) | TLS certificates on all PHI systems |
| 09.x (Key Management) | Certificate lifecycle management |
| 01.j (Access Control) | Certificate-based authentication |
| 09.ab (Monitoring) | Certificate expiry monitoring |
| 12.c (Incident Response) | Certificate revocation procedures |
FAQ
Q: Does HIPAA require specific certificate authorities?
No. HIPAA doesn’t mandate a specific CA. You can use public CAs (DigiCert, Let’s Encrypt), private CAs (AD CS, Vault PKI), or a combination. What matters is that certificates are properly managed — valid, not expired, using approved algorithms, and with documented lifecycle procedures.
Q: How do we handle medical devices that can’t auto-renew certificates?
Create a maintenance calendar. Track device certificate expiry dates in your CLM platform. Schedule certificate renewal during planned maintenance windows (many devices require physical access or vendor involvement). For critical devices, maintain spare certificates pre-generated and ready to install.
Q: Do we need a BAA (Business Associate Agreement) with our CLM vendor?
If the CLM platform processes, stores, or transmits PHI (including certificate metadata that could identify patients or systems handling PHI), yes — you need a BAA. Most enterprise CLM vendors offer BAAs. Cloud-hosted CLM platforms that only see certificate metadata (not PHI itself) may not require one, but consult your compliance team.
Q: Should we use public or private CAs for internal hospital systems?
Private CA (AD CS or similar) for internal systems — EHR integrations, device authentication, internal APIs. Public CA for patient-facing systems — patient portal, telehealth, mobile apps. This gives you control over internal certificate policies while maintaining browser trust for patient-facing services.
Q: How do we handle certificate management during hospital mergers/acquisitions?
Discovery first — scan the acquired organization’s network to inventory all certificates. Then: (1) identify overlapping CAs, (2) plan trust store consolidation, (3) migrate to unified certificate policies, (4) re-issue certificates under the parent organization’s CA where needed. This typically takes 6-12 months.
Q: What certificate validity period should we use for medical devices?
Balance security with operational reality. 2-year certificates are common for devices that support SCEP renewal. For devices that require manual renewal (physical access), 3-5 years may be necessary to align with maintenance cycles. Never exceed the device’s expected remaining service life.
Related Reading:
