The certificate lifecycle management market in 2026 looks nothing like it did three years ago. 47-day certificate lifetimes are becoming reality. Post-quantum migration is no longer theoretical. Multi-cloud is the default. And the old approach of “one person with a spreadsheet” is mathematically impossible at scale.
This guide compares every major CLM platform — enterprise vendors, CA-bundled solutions, and open-source alternatives — so you can match the right tool to your environment, budget, and compliance requirements. No vendor rankings (those are pay-to-play). Just capabilities, trade-offs, and honest assessments.
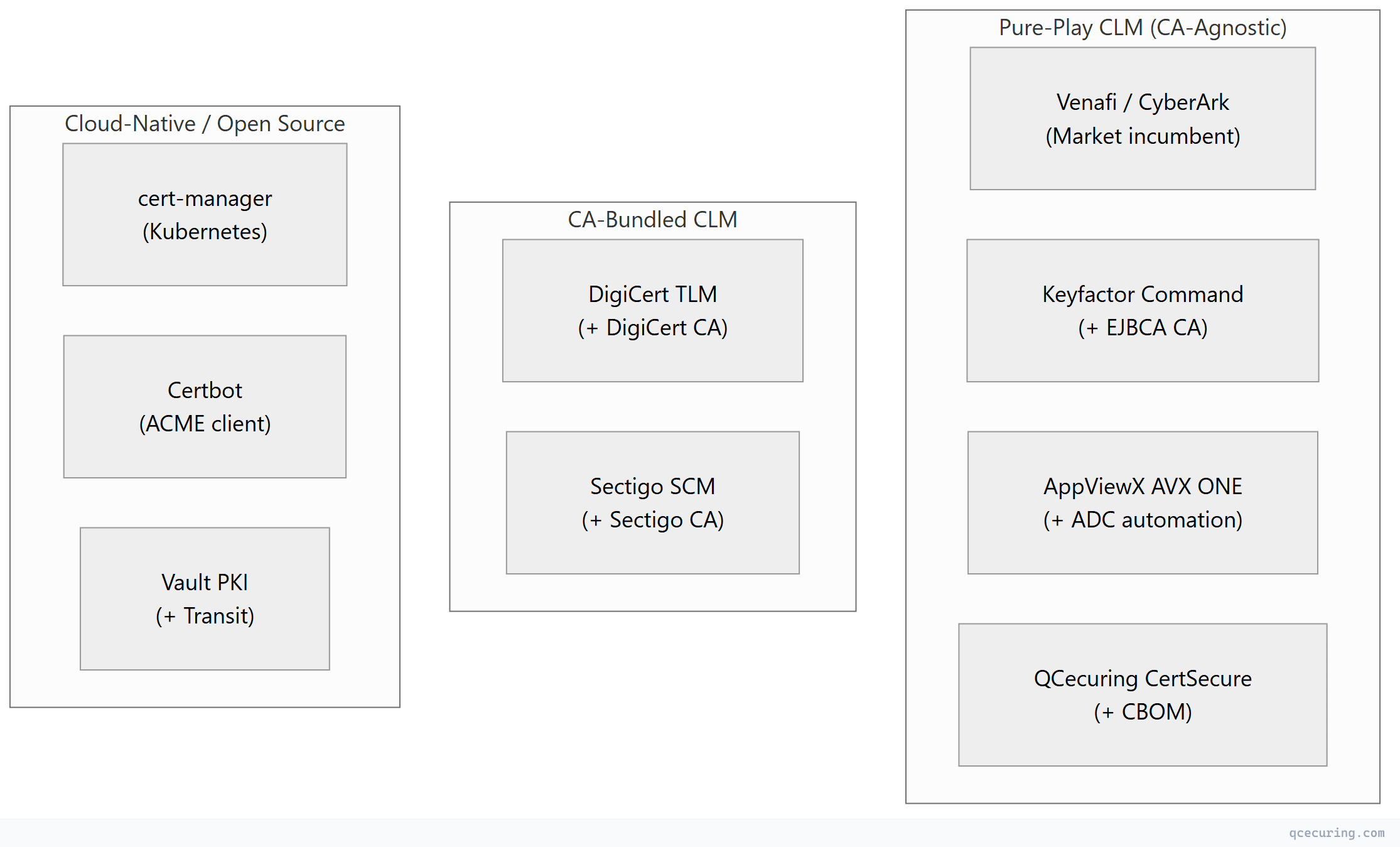
The CLM Market Landscape (2026)
The market has consolidated into three categories:
Platform Comparison Matrix
Enterprise CLM Platforms
| Venafi (CyberArk) | Keyfactor Command | AppViewX AVX ONE | QCecuring CertSecure | DigiCert TLM | Sectigo SCM | |
|---|---|---|---|---|---|---|
| Founded | 2004 | 2001 | 2008 | 2022 | 2003 | 1998 (as Comodo) |
| Ownership | CyberArk (public) | Insight Partners (PE) | Brighton Park (PE) | Private | Clearlake + TA (PE) | Francisco Partners (PE) |
| Heritage | Machine identity pioneer | Microsoft PKI tools | Network automation | Cloud-native CLM | Public CA | Volume CA |
| Architecture | Windows/.NET + SaaS | Windows/.NET + SaaS | Java microservices | Spring Boot (single JAR) | Cloud SaaS | Cloud SaaS |
| Self-hosted | Yes (complex) | Yes (Windows) | Yes (Linux) | Yes (any OS, simple) | Limited | No |
| Built-in CA | No | Yes (EJBCA) | Yes (AVX PKIaaS) | No | Yes (DigiCert) | Yes (Sectigo) |
| CA-agnostic | Yes | Yes (EJBCA-optimized) | Yes | Yes (truly neutral) | Yes (DigiCert-optimized) | Yes (Sectigo-optimized) |
| Kubernetes | Yes (Jetstack) | Yes (EJBCA issuer) | Yes (AVX K8s) | Roadmap | Limited | Limited |
| ADC/Network | Yes (broad) | Yes (orchestrators) | Yes (deepest) | Roadmap | Limited | Yes (50+ integrations) |
| AD CS depth | Good | Best | Good | Good | Good | Good |
| CBOM/PQC | Limited | Limited | Crypto Scorecards | Yes (core) | PQC certs | PQC certs |
| 47-day ready | Yes | Yes | Yes | Yes | Yes | Yes |
| Pricing | $$$$$ | $$$$ | $$$$ | $$ | $$$-$$$$ | $$-$$$ |
| Best for | Fortune 500, complex | AD CS shops, full-stack | Network-heavy, ADC | Mid-market, cloud-native | DigiCert customers | Sectigo customers |
Key Differentiators (What Makes Each Unique)
| Platform | Unique Strength |
|---|---|
| Venafi | Broadest integration ecosystem, 20 years of Fortune 500 deployments, Jetstack/cert-manager ownership |
| Keyfactor | Deepest AD CS integration + built-in EJBCA CA + SignServer code signing — full PKI stack |
| AppViewX | Network device automation (F5, Citrix, A10) + visual workflow builder + Crypto Resilience Scorecards |
| QCecuring | Simplest deployment (single JAR) + native CBOM + lowest cost + true CA-agnosticism |
| DigiCert TLM | Seamless public cert issuance + managed private PKI + Device Trust Manager for IoT |
| Sectigo SCM | Volume cert pricing + SCM Pro for SMBs + first-mover on private PQC certificates |
Selection by Organization Profile
By Size
| Organization Size | Recommended | Why |
|---|---|---|
| Startup (< 50 certs) | Certbot + Let’s Encrypt | Free, automated, sufficient |
| Small business (50-200 certs) | Sectigo SCM Pro or Certbot | Low cost, basic automation |
| Mid-market (200-2,000 certs) | QCecuring or Sectigo SCM | Cost-effective, full CLM |
| Large enterprise (2,000-20,000) | QCecuring, Keyfactor, or AppViewX | Full automation, compliance |
| Fortune 500 (20,000+ certs) | Venafi, Keyfactor, or AppViewX | Scale, integrations, support |
By Primary Environment
| Environment | Best Fit | Reason |
|---|---|---|
| Windows/AD CS heavy | Keyfactor | Deepest AD CS integration, EJBCA for non-Windows |
| Network device heavy (F5, Citrix) | AppViewX | ADC automation heritage, visual workflows |
| Multi-cloud (AWS + Azure + GCP) | QCecuring or Venafi | CA-agnostic, cloud API integrations |
| Kubernetes-first | cert-manager + Venafi/QCecuring for visibility | cert-manager for issuance, CLM for governance |
| DigiCert certificate customer | DigiCert TLM | Native integration, bundle pricing |
| Sectigo certificate customer | Sectigo SCM | Native integration, volume pricing |
| Air-gapped / government | QCecuring | Single JAR, no cloud dependency |
| MSP / multi-tenant | QCecuring | Multi-tenancy, cost-effective per client |
By Budget
| Budget Range | Options |
|---|---|
| $0 | Certbot, cert-manager, Vault PKI (open source) |
| $10K-$50K/year | QCecuring, Sectigo SCM Pro |
| $50K-$150K/year | QCecuring, Sectigo SCM Enterprise |
| $150K-$500K/year | Keyfactor, AppViewX, DigiCert TLM |
| $500K+/year | Venafi, Keyfactor (full stack) |
By Compliance Requirement
| Requirement | Must-Have Platform Features |
|---|---|
| FIPS 140-2/3 | HSM integration (all enterprise platforms support this) |
| PCI DSS 4.0 | Audit trail, key rotation tracking, discovery |
| HIPAA | Self-hosted option, encryption inventory, access controls |
| FedRAMP | Keyfactor (FedRAMP authorized) or self-hosted (QCecuring) |
| DORA / CRA (EU) | CBOM capability (QCecuring), compliance mapping |
| SOC 2 | Audit trail, RBAC, change management (all platforms) |
| CNSA 2.0 | PQC readiness, crypto inventory (QCecuring, AppViewX) |
Open-Source and Cloud-Native Alternatives
For organizations that don’t need (or can’t afford) an enterprise CLM platform:
| Tool | What It Does | Limitations |
|---|---|---|
| cert-manager | Kubernetes certificate automation | K8s only, no cross-platform visibility |
| Certbot | ACME certificate automation | Per-server, no central management |
| acme.sh | Lightweight ACME client | Scripting required, no dashboard |
| Vault PKI | Dynamic short-lived certificates | Vault ecosystem required, no discovery |
| step-ca | Modern internal ACME CA | CA only, no lifecycle management |
| EJBCA Community | Full-featured open-source CA | CA only, limited CLM features |
The gap: Open-source tools handle certificate issuance and renewal well. What they lack is: centralized discovery across all infrastructure, compliance reporting, policy enforcement, multi-CA orchestration, and the “single pane of glass” that enterprise CLM provides.
Common hybrid approach: Use cert-manager for Kubernetes, Certbot for Linux servers, AD CS for Windows — then add a CLM platform (QCecuring, Venafi, etc.) for unified visibility, compliance, and governance across all of them.
What to Ask in Vendor Evaluations
Discovery Questions
- How does your platform discover certificates on network devices that don’t expose port 443?
- Can you discover certificates inside Java keystores (JKS/PKCS12) on application servers?
- How do you handle discovery across network segments / VLANs with no direct connectivity?
- Do you monitor Certificate Transparency logs for certificates issued for my domains?
- How quickly does a newly deployed certificate appear in your inventory?
Automation Questions
- What happens if automated renewal fails? (Retry logic, alerting, escalation)
- Can you deploy renewed certificates to F5/Citrix/cloud load balancers automatically?
- How do you handle certificates that require manual approval before renewal?
- What’s the maximum renewal frequency you’ve tested? (Critical for 47-day certs)
- Can you orchestrate across multiple CAs based on policy rules?
Architecture Questions
- Can I deploy fully on-premises with no cloud connectivity?
- What database does the platform use? (Licensing implications)
- How does the agent communicate with the platform? (mTLS, API key, other)
- What’s the HA/DR architecture? (Active-active, active-passive, cloud-native)
- What happens to my data if I leave the platform?
Compliance Questions
- Can you generate audit-ready reports for [PCI/HIPAA/SOC 2/DORA]?
- Do you maintain a cryptographic inventory (CBOM) beyond just certificates?
- How do you track certificate ownership and accountability?
- Can you enforce policy (block weak keys, unapproved CAs, expired certs)?
- What’s your own security posture? (SOC 2 Type II, penetration testing, etc.)
The 47-Day Certificate Impact on CLM Selection
With certificate lifetimes shrinking to 47 days, CLM platform selection criteria shift:
| Old Priority (398-day certs) | New Priority (47-day certs) |
|---|---|
| Discovery (find forgotten certs) | Still critical |
| Monitoring (alert before expiry) | Less relevant (automation handles it) |
| Manual renewal workflows | Irrelevant (must be automated) |
| Approval processes | Must be fast or pre-approved |
| Deployment automation | Critical (8x more deployments/year) |
| Platform performance | Critical (handling 8x volume) |
| ACME support | Mandatory (not optional) |
| Multi-CA orchestration | Important (different CAs for different use cases) |
Bottom line: Any CLM platform you choose in 2026 must handle fully automated, zero-touch certificate renewal at 8x the volume of previous years. If a platform still relies on manual steps or email-based approval workflows, it won’t survive the 47-day transition.
Vendor Stability and Acquisition Risk
| Platform | Ownership | Acquisition Risk | Implication |
|---|---|---|---|
| Venafi | CyberArk (acquired 2024) | Post-acquisition integration ongoing | Product direction may shift toward CyberArk priorities |
| Keyfactor | Insight Partners (PE) | Potential future exit (IPO or acquisition) | Stable for now, PE typically exits in 5-7 years |
| AppViewX | Brighton Park Capital (PE) | Potential future exit | Growing, likely acquisition target |
| QCecuring | Private (founder-led) | Low near-term risk | Independent roadmap |
| DigiCert | Clearlake + TA Associates (PE) | Potential future exit | Stable, large revenue base |
| Sectigo | Francisco Partners (PE) | Potential future exit | Stable, established business |
PE ownership pattern: Most CLM vendors are PE-owned. This means they’re optimized for growth and eventual exit (acquisition or IPO). This isn’t inherently bad, but it means product decisions may prioritize short-term revenue over long-term technical excellence. Watch for: price increases post-acquisition, feature bundling that forces upgrades, and support quality changes during ownership transitions.
FAQ
Q: Do I need a CLM platform if I only use Let’s Encrypt?
If all certificates are Let’s Encrypt + Certbot/cert-manager with proper monitoring — probably not. A CLM adds value when you have: multiple CAs, certificates on devices that don’t support ACME, compliance reporting needs, or 500+ certificates where visibility becomes a challenge.
Q: Which CLM platform is “best”?
There’s no universal best. Venafi has the broadest integrations. Keyfactor has the deepest AD CS support. AppViewX has the best network device automation. QCecuring has the simplest deployment and lowest cost. DigiCert/Sectigo are best if you’re already their certificate customer. “Best” depends entirely on your environment, budget, and priorities.
Q: Can I use multiple CLM platforms?
Technically yes, but it defeats the purpose. The value of CLM is a single source of truth for all certificates. Running two CLM platforms creates confusion about which is authoritative. Pick one for CLM governance and use native tools (cert-manager, Certbot) for execution where appropriate.
Q: How long does CLM implementation typically take?
- Discovery and inventory: 1-2 weeks (all platforms)
- Basic automation: 2-4 weeks
- Full deployment automation: 4-8 weeks
- Policy enforcement and compliance: 2-4 weeks
- Total: 2-4 months for most platforms. QCecuring is faster (weeks). Venafi/Keyfactor are slower (months with professional services).
Q: What’s the ROI of a CLM platform?
Typical ROI calculation: (prevented outages × outage cost) + (FTE hours saved × rate) + (audit prep time saved) - platform cost. For a mid-size enterprise: 2-3 prevented outages ($200K each) + 1,500 hours saved ($112K) - platform cost ($100K) = $412K+ net annual savings. ROI is typically positive within the first year.
Q: Should I wait for the market to consolidate before choosing?
No. Certificate management is a current operational need — every day without automation is a day closer to an outage. Choose a platform that fits today and ensure your contract allows exit if the vendor is acquired or changes direction. The market will continue consolidating, but your certificates expire regardless.
Related Reading:
