The post-quantum migration starts with a question nobody can answer easily: “What cryptography do we actually use, and where?” SandboxAQ’s AQtive Guard and QCecuring’s CBOM Platform both answer this question — but from very different starting points, with different architectures, and targeting different buyer profiles.
SandboxAQ is an AI company spun out of Google/Alphabet with $500M+ in funding and a mandate to apply AI to quantitative problems — including cryptographic security. AQtive Guard uses AI-driven analysis to discover cryptographic assets and assess quantum risk. QCecuring approaches the same problem from a standards-based CLM perspective — CBOM as an extension of certificate and key lifecycle management.
Company Backgrounds
SandboxAQ
SandboxAQ was spun out of Alphabet (Google’s parent company) in March 2022 as an independent company focused on “AQ” — the intersection of AI and Quantum technologies. Led by CEO Jack Hidary (former Google X), the company raised over $500 million in funding from investors including Breyer Capital, T. Rowe Price, Salesforce Ventures, and others.
Key facts:
- Founded: 2022 (spun out of Alphabet/Google)
- Headquarters: Palo Alto, California
- Funding: $500M+ (one of the largest cybersecurity raises ever)
- CEO: Jack Hidary (former Google X)
- Products: AQtive Guard (cryptographic discovery + AI-SPM + NHI management)
- Approach: AI-driven cryptographic vulnerability detection and remediation
- Customers: US Department of War (DoW) CIO, large enterprises
- Partnerships: CrowdStrike (endpoint integration), major defense contracts
- Recent: Launched AI-SPM (Shadow AI detection), OpenCryptography.com (public resource)
- Positioning: “AI at the heart of cryptography and Non-Human Identity vulnerability detection”
SandboxAQ’s evolution: Originally focused purely on cryptographic discovery and PQC migration, AQtive Guard has expanded to cover Non-Human Identity (NHI) management and AI Security Posture Management (AI-SPM). The platform now positions itself as a broader security tool, not just a CBOM generator.
QCecuring
QCecuring’s CBOM Platform is part of their broader cryptographic security suite — integrated with CertSecure (CLM), SSH KLM, and code signing. The CBOM capability provides cryptographic asset discovery and inventory aligned with CycloneDX CBOM standards.
Key facts:
- CBOM integrated with CLM platform (not a standalone product)
- Standards-based: CycloneDX CBOM format
- Approach: Discovery + inventory + compliance mapping + migration planning
- Deployment: Self-hosted or cloud, single JAR
- Focus: Practical PQC migration planning tied to certificate/key lifecycle
Approach Comparison
| Aspect | SandboxAQ AQtive Guard | QCecuring CBOM |
|---|---|---|
| Primary approach | AI-driven vulnerability detection | Standards-based inventory + lifecycle |
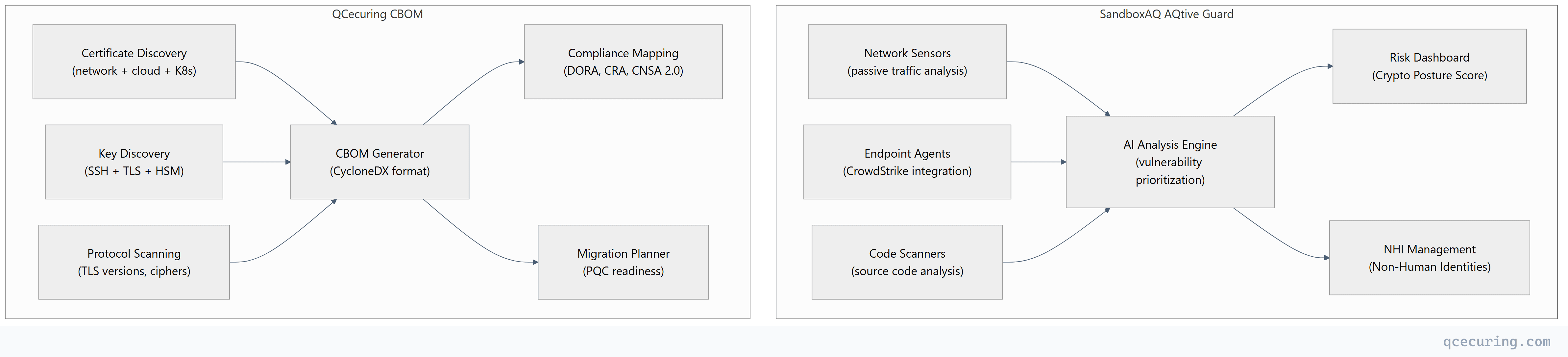
| Discovery method | Network sensors + endpoint agents + code scanning | Certificate/key discovery + protocol scanning |
| Output format | Proprietary risk dashboard | CycloneDX CBOM (open standard) |
| AI/ML usage | Core (prioritization, triage, remediation guidance) | Limited (rule-based analysis) |
| Scope | Crypto + NHI + AI security | Crypto (certificates, keys, algorithms) |
| Integration with CLM | No (standalone) | Yes (native — same platform as CertSecure) |
| Remediation | Guidance + prioritization | Automated via CLM (rotate keys, renew certs) |
| Deployment | SaaS + sensors | Self-hosted or SaaS |
| Target buyer | CISO / security team | PKI team / crypto team / compliance |
Feature Comparison
Cryptographic Discovery
| Capability | SandboxAQ | QCecuring |
|---|---|---|
| Network traffic analysis (passive) | Yes (network analyzer sensor) | Limited |
| TLS handshake inspection | Yes | Yes |
| Certificate discovery | Yes | Yes (deeper — 7 methods) |
| SSH key discovery | Limited | Yes (SSH KLM product) |
| Source code crypto scanning | Yes | No |
| Binary/firmware analysis | Yes | No |
| Cloud API scanning | Yes | Yes |
| Kubernetes scanning | Yes | Roadmap |
| HSM key inventory | Limited | Yes |
| CrowdStrike endpoint integration | Yes (native) | No |
SandboxAQ’s discovery is broader — it analyzes network traffic passively, scans source code for crypto library usage, and integrates with endpoint agents. QCecuring’s discovery is deeper for certificates and keys specifically but doesn’t do source code or binary analysis.
Risk Assessment & Prioritization
| Capability | SandboxAQ | QCecuring |
|---|---|---|
| AI-driven risk scoring | Yes (core differentiator) | No (rule-based) |
| Quantum vulnerability classification | Yes | Yes |
| Crypto posture score | Yes (dashboard metric) | Yes (compliance score) |
| Remediation prioritization | Yes (AI-ranked) | Yes (policy-based) |
| Owner assignment | Yes | Yes |
| Remediation tracking | Yes | Yes (via CLM workflows) |
| Compliance mapping (DORA, CRA, CNSA) | Yes | Yes (deeper — built-in) |
CBOM Generation
| Capability | SandboxAQ | QCecuring |
|---|---|---|
| CycloneDX CBOM output | Limited (proprietary format primary) | Yes (native CycloneDX) |
| SPDX support | No | Roadmap |
| Machine-readable inventory | Yes (API) | Yes (API + CycloneDX export) |
| Integration with SBOM tools | Yes | Yes |
| Regulatory evidence generation | Yes | Yes (DORA, CRA, CNSA 2.0 mapped) |
Remediation & Lifecycle
| Capability | SandboxAQ | QCecuring |
|---|---|---|
| Automated certificate renewal | No (discovery only) | Yes (via CertSecure CLM) |
| Automated key rotation | No | Yes (via SSH KLM) |
| Algorithm migration workflows | Guidance only | Yes (integrated with CLM) |
| Certificate re-issuance with new algorithms | No | Yes (via CA integrations) |
| Continuous monitoring | Yes | Yes |
This is QCecuring’s key advantage: AQtive Guard discovers and prioritizes, but it can’t fix anything. QCecuring discovers AND remediates — because the CBOM is integrated with the CLM platform that actually manages certificates and keys. When QCecuring identifies a weak algorithm, it can automatically renew the certificate with a stronger one.
Where SandboxAQ Wins
1. AI-Driven Analysis
SandboxAQ’s AI engine doesn’t just list cryptographic assets — it prioritizes them by actual risk, considering factors like: data sensitivity, exposure level, algorithm weakness, and migration complexity. This is more sophisticated than rule-based scoring.
2. Source Code and Binary Analysis
AQtive Guard can scan source code repositories and compiled binaries for cryptographic library usage — finding hardcoded algorithms, deprecated crypto calls, and vulnerable dependencies. QCecuring only discovers crypto at the network/infrastructure level, not in application code.
3. Non-Human Identity (NHI) Management
AQtive Guard has expanded beyond pure cryptography to cover all non-human identities — service accounts, API keys, tokens, and machine credentials. This broader scope appeals to security teams managing the full NHI attack surface.
4. CrowdStrike Integration
One-click integration with CrowdStrike endpoints means AQtive Guard can discover cryptographic assets on every endpoint in your fleet without deploying additional agents. For organizations already running CrowdStrike, this is frictionless deployment.
5. Government/Defense Credentials
SandboxAQ’s partnership with the US Department of War CIO and their Alphabet pedigree gives them credibility in government and defense markets. For organizations requiring vendor security clearances or government references, SandboxAQ has an edge.
6. OpenCryptography.com (Public Resource)
SandboxAQ launched OpenCryptography.com — a free public resource for assessing cryptographic risk in open-source software. This demonstrates thought leadership and provides value even to non-customers.
Where QCecuring Wins
1. Integrated Remediation (Discovery + Fix)
QCecuring’s CBOM is part of the same platform that manages certificates and keys. When it finds a weak algorithm, it can trigger automated renewal with a stronger algorithm. AQtive Guard tells you what’s wrong; QCecuring fixes it.
2. Standards-Based CBOM (CycloneDX)
QCecuring generates CycloneDX-format CBOMs — an open standard that integrates with existing SBOM tooling, vulnerability management platforms, and compliance workflows. AQtive Guard’s output is primarily proprietary dashboards.
3. Self-Hosted / Air-Gapped Deployment
QCecuring deploys as a single JAR on your infrastructure — no data leaves your network. AQtive Guard is primarily SaaS with on-premises sensors. For classified environments or strict data sovereignty, QCecuring’s model is simpler.
4. Cost
SandboxAQ targets large enterprises and government with pricing to match their $500M+ funding and Alphabet pedigree. QCecuring provides CBOM capabilities as part of their broader platform at a fraction of the cost — accessible to mid-market organizations, not just Fortune 500.
5. Certificate and Key Lifecycle (Not Just Discovery)
QCecuring’s CBOM is one view within a platform that also handles: certificate issuance, renewal, deployment, SSH key rotation, and compliance reporting. It’s a complete cryptographic lifecycle platform. AQtive Guard is discovery and assessment only — you need separate tools for lifecycle management.
6. EU Compliance Mapping
QCecuring has built-in mapping to DORA, CRA, and CNSA 2.0 requirements — generating audit-ready evidence for European regulators. AQtive Guard’s compliance focus is more US-centric (DoD, NIST).
Pricing Comparison
| SandboxAQ AQtive Guard | QCecuring CBOM | |
|---|---|---|
| Target market | Large enterprise, government | Mid-market to enterprise |
| Pricing model | Enterprise (custom) | Platform license (includes CBOM) |
| Entry point | $$$$$ (Alphabet-backed pricing) | $$ (part of CertSecure platform) |
| Standalone CBOM | Yes (primary product) | No (included with CLM platform) |
| Additional products | AI-SPM, NHI management | CLM, SSH KLM, Code Signing |
| Professional services | Yes (typically required) | Optional |
Decision Framework
| If You… | Choose |
|---|---|
| Need AI-driven crypto risk prioritization | SandboxAQ |
| Need source code / binary crypto scanning | SandboxAQ |
| Already use CrowdStrike and want frictionless discovery | SandboxAQ |
| Are US government/defense with clearance requirements | SandboxAQ |
| Need discovery + automated remediation (fix, not just find) | QCecuring |
| Need CycloneDX-standard CBOM output | QCecuring |
| Need self-hosted / air-gapped deployment | QCecuring |
| Are mid-market with budget constraints | QCecuring |
| Need CBOM integrated with certificate/key lifecycle | QCecuring |
| Need EU compliance mapping (DORA, CRA) | QCecuring |
| Want broader NHI management beyond crypto | SandboxAQ |
| Want a focused crypto lifecycle platform | QCecuring |
The Complementary Approach
These platforms can work together:
- SandboxAQ for deep discovery (source code, binaries, network traffic, NHI)
- QCecuring for lifecycle management (renew certs, rotate keys, enforce policy)
SandboxAQ finds the problems. QCecuring fixes them. The CBOM from either platform feeds into your PQC migration planning.
FAQ
Q: Is SandboxAQ just for post-quantum migration?
No longer. AQtive Guard has expanded to cover Non-Human Identity management and AI Security Posture Management. PQC migration is one use case, but the platform now addresses broader cryptographic and identity security. QCecuring’s CBOM is more focused on the crypto lifecycle specifically.
Q: Do I need both a CBOM tool and a CLM tool?
Ideally they’re integrated. A CBOM without remediation capability is just a report. A CLM without cryptographic inventory has blind spots. QCecuring integrates both. If you use SandboxAQ for CBOM, you still need a separate CLM for certificate/key lifecycle management.
Q: How does SandboxAQ’s AI actually help?
The AI prioritizes remediation — instead of a flat list of 10,000 cryptographic assets, it ranks them by actual risk (considering data sensitivity, exposure, algorithm weakness, and migration complexity). It also provides remediation guidance specific to each finding. This reduces the “where do I start?” paralysis.
Q: Can QCecuring’s CBOM scan source code?
No. QCecuring discovers cryptography at the infrastructure level — certificates, keys, TLS configurations, SSH keys. For source code crypto scanning (finding hardcoded algorithms, deprecated library calls), you’d need SandboxAQ, Snyk, or similar code analysis tools.
Q: Which is better for CNSA 2.0 compliance?
Both support CNSA 2.0 assessment. SandboxAQ provides AI-driven prioritization of quantum-vulnerable assets. QCecuring provides standards-based inventory with compliance mapping. For generating audit evidence, QCecuring’s CycloneDX output is more structured. For understanding risk priority, SandboxAQ’s AI scoring is more sophisticated.
Q: Is $500M in funding a good sign or a red flag?
It means SandboxAQ has runway and resources to invest in the product. But it also means they need to justify that valuation — which typically means enterprise-only pricing and aggressive growth targets. For mid-market organizations, this pricing pressure may make SandboxAQ inaccessible.
Related Reading:
