Cryptographic Bills of Materials (CBOMs) went from academic concept to compliance requirement in under two years. NIST’s post-quantum standards are finalized, the EU Cyber Resilience Act mandates cryptographic transparency, and enterprises are realizing they can’t migrate what they can’t find.
The CBOM tooling market has responded. From AI-driven platforms backed by $500M+ in funding to open-source projects from the Linux Foundation, organizations now have real options for cryptographic discovery and inventory. This comparison covers the six tools that matter in 2026, when each fits, and how to choose between them.
Why CBOM Tools Matter Now
Three regulatory and technical drivers are forcing action:
- NIST PQC migration deadlines — CNSA 2.0 requires hybrid key exchange by 2027 and full PQC by 2033. You can’t migrate algorithms you haven’t inventoried.
- EU Cyber Resilience Act (CRA) — Requires manufacturers to document cryptographic components in products. CBOM is the mechanism.
- 47-day certificate lifetimes — Shorter lifetimes expose weak automation. Discovery tools identify certificates that lack automated renewal.
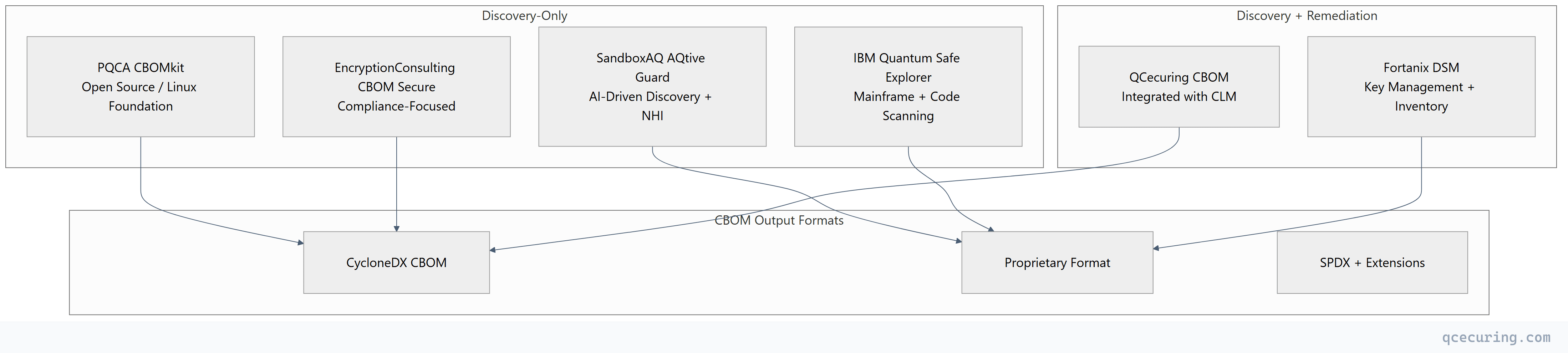
The market splits into two categories: discovery-only tools that find and catalog cryptographic assets, and discovery + remediation platforms that can also fix what they find.
Tool Comparison Overview
1. SandboxAQ AQtive Guard
Background: Spun out of Alphabet (Google) in 2022, SandboxAQ has raised over $500M in funding and secured partnerships with the U.S. Department of Defense and multiple NATO allies. Their approach combines AI/ML for cryptographic vulnerability detection with non-human identity (NHI) management.
What it does:
- Network traffic analysis to identify cryptographic protocols in use
- Code repository scanning for hardcoded algorithms and weak crypto
- AI-driven risk prioritization based on quantum vulnerability timelines
- Non-human identity discovery (service accounts, API keys, machine certificates)
- Integration with SIEM/SOAR for automated alerting
Strengths:
| Capability | Detail |
|---|---|
| AI-driven discovery | ML models identify crypto usage patterns in network traffic without agents |
| Scale | Designed for Fortune 500 / government scale (100K+ endpoints) |
| NHI management | Unique combination of crypto discovery + machine identity |
| Threat intelligence | Quantum risk scoring based on “harvest now, decrypt later” timelines |
| Government validated | DoD partnership provides credibility for regulated industries |
Limitations:
- Discovery only — cannot remediate (rotate certificates, update algorithms)
- Proprietary output format (not native CycloneDX/SPDX)
- Enterprise pricing starts in six figures annually
- Requires significant professional services for deployment
- AI models need training period for accurate results in custom environments
Best for: Large enterprises and government agencies that need AI-powered discovery at massive scale and have separate tools for remediation.
2. IBM Quantum Safe Explorer
Background: Part of IBM’s broader Quantum Safe portfolio, QSE focuses on identifying cryptographic vulnerabilities in enterprise codebases and mainframe environments — a niche no other tool covers well.
What it does:
- Static code analysis for cryptographic API usage (Java, C/C++, Python, COBOL)
- Mainframe cryptographic inventory (z/OS ICSF, RACF key rings)
- Dependency scanning for vulnerable crypto libraries
- Migration planning with algorithm replacement recommendations
- Integration with IBM z/OS and IBM Cloud Pak
Strengths:
| Capability | Detail |
|---|---|
| Mainframe support | Only tool with deep z/OS ICSF and RACF integration |
| Code scanning | Identifies crypto at the source code level, not just network |
| COBOL analysis | Critical for financial services with legacy mainframe code |
| Migration planning | Provides specific algorithm replacement paths |
| IBM ecosystem | Tight integration with IBM Cloud, z/OS, and MQ |
Limitations:
- Heavily IBM-ecosystem focused — less useful outside IBM shops
- Limited network-level discovery (primarily code and config scanning)
- No certificate lifecycle management integration
- Proprietary reporting format
- Requires IBM consulting engagement for complex deployments
Best for: Financial services and enterprises with significant mainframe infrastructure running z/OS, CICS, and COBOL applications.
3. QCecuring CBOM
Background: QCecuring’s CBOM capability is integrated directly into the QCecuring SSL Certificate Lifecycle Management platform. Rather than being a standalone discovery tool, it extends the CLM platform with cryptographic inventory and generates standard CycloneDX CBOMs.
What it does:
- Certificate and key discovery across hybrid infrastructure (on-prem, cloud, Kubernetes)
- Algorithm inventory with PQC readiness scoring
- CycloneDX CBOM generation for compliance reporting
- Direct remediation — when weak crypto is found, the CLM platform can rotate/renew
- Continuous monitoring with drift detection
- Integration with CI/CD pipelines for build-time CBOM generation
Strengths:
| Capability | Detail |
|---|---|
| Discovery + remediation | Only platform that finds weak crypto AND fixes it automatically |
| CycloneDX native | Standard CBOM format for supply chain compliance |
| CLM integration | Certificate rotation triggered directly from CBOM findings |
| Continuous monitoring | Not a point-in-time scan — ongoing drift detection |
| Lightweight deployment | Single JAR, no complex infrastructure |
| Multi-CA visibility | Discovers certs from AD CS, Vault, Let’s Encrypt, cloud CAs |
Limitations:
- Focused on certificates and TLS — less depth on code-level crypto analysis
- Smaller company compared to SandboxAQ or IBM
- No mainframe-specific scanning
- NHI management is certificate-focused (not broader service account discovery)
Best for: Organizations that want a single platform for cryptographic discovery AND certificate lifecycle management, especially those already evaluating CLM solutions.
4. PQCA CBOMkit (Open Source)
Background: Developed under the Post-Quantum Cryptography Alliance (PQCA), a Linux Foundation project. CBOMkit is fully open source and designed as a reference implementation for CycloneDX CBOM generation.
What it does:
- Java/Python library scanning for cryptographic dependencies
- CycloneDX CBOM generation from source code analysis
- Integration with SBOM tools (Syft, Trivy, Grype)
- Cryptographic algorithm identification in compiled binaries
- Community-maintained vulnerability database
Strengths:
| Capability | Detail |
|---|---|
| Open source | Free, auditable, no vendor lock-in |
| CycloneDX native | Reference implementation for the CBOM standard |
| SBOM integration | Plugs into existing SBOM pipelines (Syft, Trivy) |
| Community-driven | Linux Foundation governance, multi-vendor contributions |
| CI/CD friendly | Designed for pipeline integration from day one |
| Extensible | Plugin architecture for custom scanners |
Limitations:
- No network-level discovery (code/dependency scanning only)
- No remediation capability
- Requires engineering effort to deploy and maintain
- Limited enterprise support (community-only unless you engage a contributor)
- No GUI — CLI and API only
- Smaller vulnerability database compared to commercial tools
Best for: Engineering teams that want to integrate CBOM generation into CI/CD pipelines, organizations with strong DevSecOps practices, and those evaluating CBOM standards before committing to a commercial tool.
5. EncryptionConsulting CBOM Secure
Background: EncryptionConsulting launched CBOM Secure in early 2026 as a compliance-focused cryptographic discovery platform. The company has deep roots in PKI consulting and compliance advisory.
What it does:
- Network scanning for TLS/SSH/IPsec cryptographic configurations
- Certificate discovery and expiry tracking
- Compliance mapping to NIST, CRA, DORA, and PCI DSS requirements
- CycloneDX CBOM export
- Executive reporting and risk dashboards
- Consulting-led deployment with managed service option
Strengths:
| Capability | Detail |
|---|---|
| Compliance-first | Built-in mapping to CRA, DORA, NIST frameworks |
| Managed service | Available as a fully managed offering |
| Executive reporting | Non-technical dashboards for CISO/board reporting |
| CycloneDX output | Standard format for supply chain requirements |
| Consulting integration | Same team that deploys can advise on remediation strategy |
Limitations:
- Newer product (launched 2026) — less battle-tested
- No automated remediation
- Limited code-level scanning (primarily network and configuration)
- Smaller customer base means fewer integrations
- Pricing not publicly available
Best for: Organizations that want a managed CBOM service with strong compliance reporting, especially those already working with EncryptionConsulting for PKI advisory.
6. Fortanix Data Security Manager (DSM)
Background: Fortanix DSM is primarily a key management and HSM-as-a-service platform, but its cryptographic inventory capabilities make it relevant for CBOM use cases — particularly for organizations that need key management and crypto discovery in one platform.
What it does:
- Centralized key management (HSM-backed)
- Cryptographic inventory of all keys managed through DSM
- Algorithm usage reporting and weak-key identification
- Integration with cloud KMS (AWS, Azure, GCP)
- Tokenization and encryption services
- Runtime key usage monitoring
Strengths:
| Capability | Detail |
|---|---|
| Key management + inventory | Unified platform for managing and inventorying keys |
| HSM-backed | FIPS 140-2 Level 3 for managed keys |
| Cloud KMS integration | Discovers keys across AWS KMS, Azure Key Vault, GCP KMS |
| Runtime monitoring | Sees actual key usage, not just configuration |
| Established platform | Production-proven at scale |
Limitations:
- Crypto inventory limited to keys managed through or integrated with DSM
- Not a full CBOM tool — doesn’t scan code or network traffic
- No certificate lifecycle management
- Proprietary reporting (not CycloneDX native)
- Primarily a KMS that happens to have inventory features
Best for: Organizations that need a key management platform with built-in cryptographic inventory, especially those consolidating HSM and KMS infrastructure.
Comparison Table
| Feature | SandboxAQ AQtive Guard | IBM QSE | QCecuring CBOM | PQCA CBOMkit | EncryptionConsulting | Fortanix DSM |
|---|---|---|---|---|---|---|
| Discovery method | Network + AI | Code + mainframe | Network + config | Code + deps | Network + config | Key management |
| Remediation | No | No | Yes (via CLM) | No | No | Partial (key rotation) |
| CBOM format | Proprietary | Proprietary | CycloneDX | CycloneDX | CycloneDX | Proprietary |
| Code scanning | Yes | Yes (deep) | Limited | Yes | Limited | No |
| Network scanning | Yes (AI) | Limited | Yes | No | Yes | No |
| Mainframe support | No | Yes | No | No | No | No |
| Kubernetes/cloud | Yes | Limited | Yes | Yes (CI/CD) | Limited | Yes (KMS) |
| Open source | No | No | No | Yes | No | No |
| Managed service | Yes | Yes (IBM) | No | No | Yes | Yes |
| Pricing | $$$$ | $$$ | $$ | Free | $$-$$$ | $$$ |
| Deployment time | Weeks-months | Weeks | Days | Hours | Weeks | Days-weeks |
| Best for | Large enterprise/gov | Mainframe shops | Mid-enterprise CLM | DevSecOps teams | Compliance-focused | KMS consolidation |
Selection Criteria: How to Choose
Decision Framework
Start with your primary use case:
| If you need… | Choose… | Why |
|---|---|---|
| AI-powered discovery at massive scale | SandboxAQ AQtive Guard | Unmatched scale and AI capabilities |
| Mainframe crypto inventory | IBM Quantum Safe Explorer | Only tool with deep z/OS support |
| Discovery AND automated remediation | QCecuring CBOM | Integrated CLM means findings become actions |
| Open-source CBOM in CI/CD | PQCA CBOMkit | Free, standard, pipeline-native |
| Compliance reporting + managed service | EncryptionConsulting CBOM Secure | Built for auditors and CISOs |
| Key management + crypto inventory | Fortanix DSM | Unified KMS with inventory |
Evaluation Checklist
Before selecting a tool, answer these questions:
- What are you scanning? Network traffic, source code, configurations, or all three?
- Do you need remediation? Or just discovery and reporting?
- What’s your compliance driver? CRA, DORA, NIST, or internal policy?
- What format do you need? CycloneDX (standard) or proprietary (vendor-specific)?
- What’s your budget? Free (CBOMkit) to six figures (SandboxAQ)?
- Do you have mainframes? If yes, IBM QSE is likely required regardless of other choices.
- Do you already have CLM? If not, QCecuring CBOM gives you both in one platform.
Combining Tools: The Multi-Layer Approach
Many enterprises use more than one tool:
| Layer | Tool | Purpose |
|---|---|---|
| Code/build time | PQCA CBOMkit | Generate CBOM during CI/CD |
| Runtime/network | SandboxAQ or QCecuring | Discover crypto in production traffic |
| Certificate management | QCecuring CLM | Manage lifecycle of discovered certificates |
| Key management | Fortanix DSM | Manage and inventory encryption keys |
| Compliance reporting | EncryptionConsulting or QCecuring | Map findings to regulatory frameworks |
The combination of CBOMkit (free, CI/CD) + QCecuring CBOM (runtime discovery + remediation) covers most enterprise needs without the six-figure price tag of AQtive Guard.
Market Trajectory
The CBOM market is consolidating around a few patterns:
- Discovery is commoditizing — Network scanning for TLS configurations is table stakes. Differentiation comes from code analysis depth, AI-driven prioritization, and remediation.
- CycloneDX is winning — OWASP’s CycloneDX format is becoming the de facto standard for CBOMs. Tools that output proprietary formats will need to add CycloneDX export.
- Integration beats standalone — Standalone discovery tools create “yet another dashboard.” Tools integrated with CLM, KMS, or SBOM platforms provide more value.
- Open source sets the floor — PQCA CBOMkit establishes what’s freely available. Commercial tools must justify their premium with scale, AI, or remediation.
FAQ
Q: Do I need a CBOM tool if I already have an SBOM tool? A: Yes. SBOMs (Software Bills of Materials) list software components and their versions. CBOMs specifically catalog cryptographic algorithms, key sizes, certificate chains, and protocol configurations. An SBOM tells you that you use OpenSSL 3.2.1. A CBOM tells you that OpenSSL is configured with RSA-2048 keys and TLS 1.2 with specific cipher suites. Some SBOM tools (Syft, Trivy) are adding CBOM extensions, but dedicated CBOM tools provide deeper cryptographic analysis.
Q: Is CycloneDX the only CBOM standard? A: CycloneDX (from OWASP) is the most mature CBOM standard with dedicated cryptographic component types. SPDX (from Linux Foundation) is adding cryptographic extensions but isn’t as far along. For compliance purposes, CycloneDX is the safer choice today. Most tools that output proprietary formats can export to CycloneDX on request.
Q: How often should I regenerate my CBOM? A: Continuously for network-discovered assets (certificates expire, configurations change). For code-level CBOMs, regenerate on every build or at minimum every release. Point-in-time CBOMs are useful for compliance snapshots but miss drift between scans.
Q: Can open-source CBOMkit replace commercial tools? A: For CI/CD pipeline CBOM generation, yes. CBOMkit handles dependency scanning and code-level crypto identification well. For network discovery, runtime monitoring, and automated remediation, you’ll need commercial tools. Many organizations use CBOMkit for build-time and a commercial tool for runtime — they complement rather than compete.
Q: What’s the relationship between SandboxAQ and Google? A: SandboxAQ was incubated within Alphabet (Google’s parent company) and spun out as an independent company in 2022. It retained some Google AI/ML technology and talent but operates independently. The Alphabet connection provides credibility and access to AI research, but SandboxAQ is a separate entity with its own investors and governance.
Q: How do CBOM tools handle encrypted traffic they can’t inspect? A: Network-based tools (SandboxAQ, QCecuring, EncryptionConsulting) analyze TLS handshakes — the cipher suite negotiation happens in plaintext before encryption begins. They can identify algorithms, key sizes, and certificate details without decrypting payload traffic. For internal east-west traffic, some tools integrate with service mesh sidecars (Envoy, Istio) that have access to plaintext configuration.
Related Reading:
