DigiCert is one of the world’s largest public certificate authorities — they issue the TLS certificates that secure a significant portion of the internet’s HTTPS traffic. Their Trust Lifecycle Manager (TLM) is the CLM platform they built to manage those certificates (and certificates from other CAs) across enterprise infrastructure.
The fundamental question when evaluating DigiCert TLM: do you want your CLM from the same vendor that issues your public certificates? There are advantages to that tight integration — and significant trade-offs around vendor lock-in, CA-agnosticism, and pricing leverage.
Company Backgrounds
DigiCert
DigiCert was founded in 2003 in Lehi, Utah. They’re one of the “Big Three” public CAs (alongside Sectigo and GlobalSign) and the largest issuer of high-assurance (OV/EV) TLS certificates. In 2017, DigiCert acquired Symantec’s Website Security business (including the former VeriSign CA), making them the dominant enterprise CA.
DigiCert ONE is their unified platform that includes:
- CertCentral — public certificate issuance and management
- Trust Lifecycle Manager — CA-agnostic CLM for public and private certificates
- Device Trust Manager — IoT device certificate management
- Document Trust Manager — document signing
- Software Trust Manager — code signing
Key facts:
- Founded: 2003, Lehi, Utah
- Ownership: Private (Clearlake Capital + TA Associates acquired in 2019 for ~$1B)
- Revenue: Estimated $500M+ annually
- Customers: 89% of Fortune 500 use DigiCert certificates
- Products: DigiCert ONE platform (CertCentral, TLM, Device Trust, Software Trust, Document Trust)
- Heritage: Public CA → expanded to CLM and private PKI
- G2 Rating: 3.8/5 (11 reviews for TLM specifically)
- Gartner: Listed in CLM market guide, targets $1B-$10B companies
The CA-bundled CLM model: DigiCert TLM is designed to work best with DigiCert-issued certificates. It claims CA-agnosticism (managing certs from other CAs), but the tightest integration, fastest issuance, and best pricing come when you’re also buying DigiCert certificates. This creates a natural incentive to consolidate your public certificate purchases with DigiCert.
QCecuring
QCecuring is an enterprise cryptographic security company with no CA business. They don’t issue certificates — they manage them regardless of which CA issued them. This means zero incentive to push you toward any specific CA.
Key facts:
- Modern architecture: Spring Boot + MongoDB + Angular, single JAR deployment
- Products: CertSecure (CLM), SSH KLM, Code Signing, PKI-aaS, HSM-aaS, CBOM
- Focus: Mid-market to enterprise, government, MSPs
- No CA revenue — purely a management platform
- True CA-agnosticism (no commercial relationship with any CA)
The CA-Bundled vs CA-Agnostic Debate
This is the core architectural difference between these platforms:
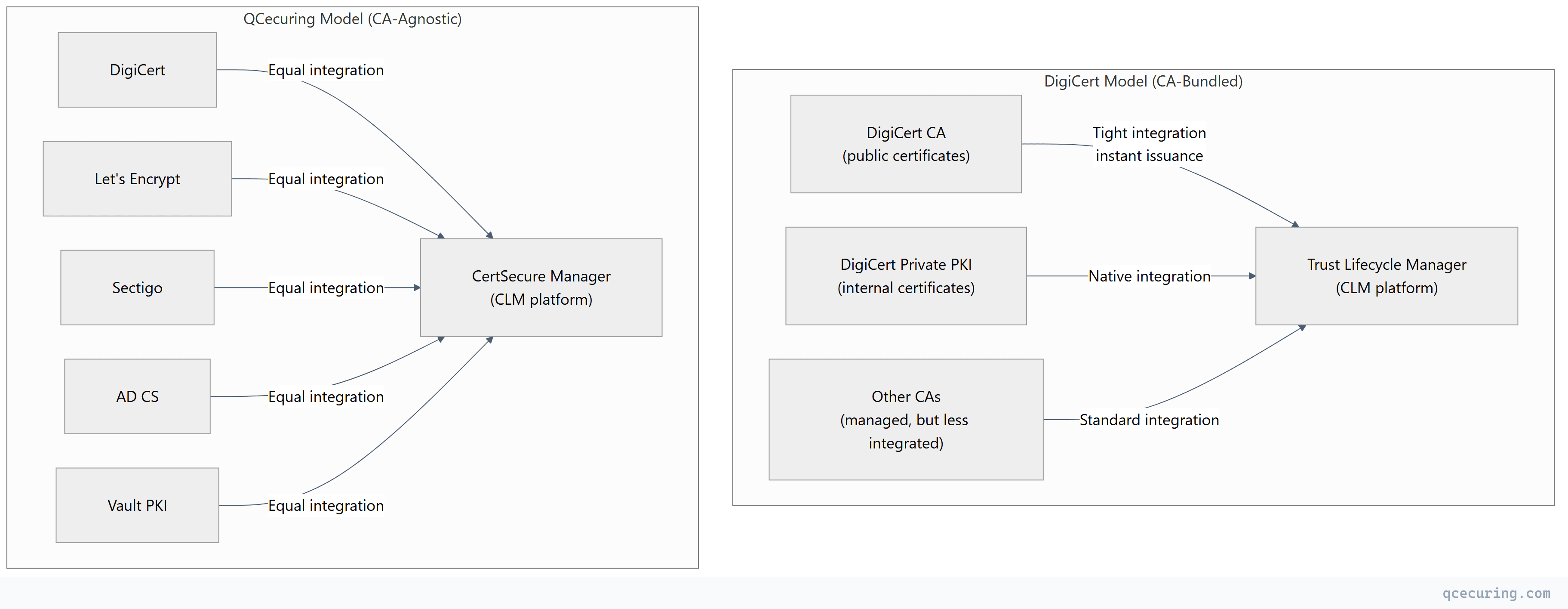
Advantages of CA-bundled (DigiCert):
- Single vendor for issuance + management = simpler procurement
- Tighter integration = faster operations for DigiCert certs
- Combined billing = potentially better pricing on certificates
- Single support contact for CA + CLM issues
Advantages of CA-agnostic (QCecuring):
- No vendor lock-in to any CA
- Equal management quality regardless of issuing CA
- Freedom to switch CAs based on pricing/features
- No conflict of interest (platform doesn’t benefit from you buying more certs from a specific CA)
- Better for multi-CA environments (most enterprises use 3-5 CAs)
Feature-by-Feature Comparison
Discovery
| Capability | QCecuring | DigiCert TLM |
|---|---|---|
| Network port scanning | Yes (7 methods) | Yes |
| Cloud API (AWS, Azure, GCP) | Yes (native) | Yes |
| AD CS / Microsoft PKI | Yes | Yes |
| Kubernetes | Roadmap | Limited |
| Certificate Transparency logs | Yes | Yes (strong — they operate CT logs) |
| DigiCert-issued cert discovery | Yes (via CT/network) | Native (instant — they issued them) |
| Non-DigiCert cert discovery | Yes (equal quality) | Yes (but less integrated) |
| CBOM (cryptographic inventory) | Yes (core feature) | No |
DigiCert’s CT log advantage: DigiCert operates several Certificate Transparency logs. They have instant visibility into every certificate they’ve issued, plus strong CT log monitoring for certificates from other CAs. This gives them a discovery advantage for public certificates specifically.
Automation & Lifecycle
| Capability | QCecuring | DigiCert TLM |
|---|---|---|
| ACME protocol | Yes (full v2) | Yes |
| DigiCert certificate issuance | Yes (via API) | Native (instant, no API hop) |
| Other CA issuance | Yes (equal) | Yes (standard integration) |
| AD CS enrollment | Yes | Yes |
| Zero-touch renewal | Yes | Yes |
| Deployment automation | Yes (web servers, cloud) | Yes |
| Approval workflows | Yes | Yes |
| Self-service portal | Yes | Yes |
| REST API | Yes (full) | Yes |
Private PKI
| Capability | QCecuring | DigiCert TLM |
|---|---|---|
| Built-in private CA | No (works with any) | Yes (DigiCert Private PKI) |
| Private CA hosting | No | Yes (DigiCert-managed) |
| AD CS integration | Yes | Yes |
| Vault PKI integration | Yes | Limited |
| Custom certificate profiles | Via CA configuration | Yes (DigiCert profiles) |
DigiCert offers a managed private CA service — they host and operate your internal CA infrastructure. This is convenient but creates deep vendor dependency. If you leave DigiCert, migrating your private CA is complex.
Compliance & Reporting
| Capability | QCecuring | DigiCert TLM |
|---|---|---|
| Compliance reports (PCI, HIPAA, SOC 2) | Yes (built-in) | Yes |
| CBOM for regulatory evidence | Yes | No |
| Audit trail | Complete | Complete |
| RBAC | Yes | Yes |
| SIEM integration | Yes | Yes |
| EU compliance (DORA, CRA) | Yes (built-in mapping) | Limited |
Where QCecuring Wins
1. True CA-Agnosticism
QCecuring has no CA business. They don’t benefit commercially from you buying certificates from any specific CA. Every CA integration gets equal engineering attention and equal feature depth.
DigiCert TLM works with other CAs, but the product is optimized for DigiCert certificates. Features like instant issuance, combined billing, and native private PKI only work with DigiCert. If 60% of your certificates come from Let’s Encrypt and AD CS, you’re not getting the full value of DigiCert TLM.
2. Deployment Flexibility
QCecuring deploys as a single JAR — self-hosted on any OS, Docker, Kubernetes, or air-gapped environments. DigiCert TLM is primarily a SaaS platform. While this is convenient, it means your certificate management data lives in DigiCert’s cloud. For organizations with data sovereignty requirements or air-gapped environments, this is a blocker.
3. Cost (Especially If You Don’t Use DigiCert Certificates)
DigiCert TLM’s pricing makes most sense when bundled with DigiCert certificate purchases. If you’re primarily using Let’s Encrypt (free), AD CS (included with Windows), or another CA, you’re paying DigiCert CLM pricing without the certificate bundle discount.
QCecuring’s pricing is independent of which CA you use — the platform cost is the same whether you issue from DigiCert, Sectigo, or Let’s Encrypt.
4. CBOM and PQC Readiness
QCecuring’s native CBOM provides a complete cryptographic inventory — not just certificates but all cryptographic assets, algorithms, and protocols. This maps directly to DORA, CRA, and CNSA 2.0 compliance requirements.
DigiCert TLM doesn’t offer equivalent cryptographic inventory capabilities. Their PQC story is primarily at the CA level (they can issue PQC test certificates) rather than at the CLM level (inventory and migration planning).
5. Multi-CA Environments
Most enterprises use 3-5 CAs: DigiCert or Sectigo for public certs, AD CS for internal Windows, Let’s Encrypt for automation-friendly services, maybe Vault for microservices. QCecuring treats all of these equally. DigiCert TLM has a natural bias toward consolidating everything on DigiCert.
Where DigiCert TLM Wins
1. Seamless Public Certificate Issuance
If you buy public TLS certificates from DigiCert (and many enterprises do — they’re the largest enterprise CA), TLM provides instant issuance without API configuration. Request a certificate in TLM → it’s issued by DigiCert CA → deployed to your server. One vendor, one workflow, no integration gaps.
2. Certificate Transparency Expertise
DigiCert operates CT logs and has deep expertise in certificate transparency monitoring. Their TLM platform can detect misissued certificates (from any CA) faster than most competitors because they’re embedded in the CT ecosystem.
3. Managed Private PKI
DigiCert offers a fully managed private CA service. They host the CA, manage the HSMs, handle CRL distribution, and provide the certificates. For organizations that don’t want to run their own CA infrastructure (AD CS, EJBCA, Vault), this is a turnkey solution.
4. Brand Trust and Procurement Simplicity
DigiCert is a household name in enterprise security. “We use DigiCert for our certificates and their CLM platform to manage them” is an easy story for procurement, auditors, and executives. One vendor, one contract, one support relationship.
5. IoT Device Trust Manager
DigiCert’s Device Trust Manager (part of DigiCert ONE) provides device certificate provisioning at manufacturing scale — hardware-backed identity, zero-touch onboarding, and MQTT/Matter ecosystem support. If you’re a device manufacturer needing production-scale certificate provisioning, this is a mature offering.
Pricing Comparison
| QCecuring | DigiCert TLM | |
|---|---|---|
| Pricing model | Platform license | Platform + certificate volume |
| Certificate cost | You pay your CA directly | Bundled (discount if buying DigiCert certs) |
| Private PKI | Use your own CA (no extra cost) | DigiCert Private PKI (additional cost) |
| SaaS | Available | Primary deployment model |
| Self-hosted | Yes (single JAR) | Limited (primarily SaaS) |
| Entry point | Mid-market accessible | Enterprise (targets $1B+ companies) |
| Year 1 TCO | $$ | $$$-$$$$ (depends on cert volume) |
The bundling trap: DigiCert TLM pricing often looks attractive when bundled with certificate purchases. But this creates lock-in — switching CAs later means losing the bundle discount AND potentially needing a new CLM platform. QCecuring’s independent pricing means you can switch CAs freely without CLM cost implications.
Decision Framework
| If You… | Choose |
|---|---|
| Already buy most certificates from DigiCert | DigiCert TLM (natural fit) |
| Want one vendor for CA + CLM + device trust | DigiCert TLM |
| Need managed private PKI (don’t want to run your own CA) | DigiCert TLM |
| Are a device manufacturer needing IoT provisioning | DigiCert TLM |
| Use multiple CAs and want equal management | QCecuring |
| Need self-hosted / air-gapped deployment | QCecuring |
| Are cost-sensitive or mid-market | QCecuring |
| Need CBOM for compliance/PQC planning | QCecuring |
| Want to avoid CA vendor lock-in | QCecuring |
| Use primarily Let’s Encrypt / AD CS / Vault | QCecuring |
| Need EU compliance mapping (DORA, CRA) | QCecuring |
| Are an MSP managing multiple clients | QCecuring |
The Vendor Lock-In Question
This deserves explicit discussion. When you use DigiCert TLM:
- Certificate data lives in DigiCert’s platform
- Private PKI (if used) is DigiCert-hosted — migrating means rebuilding your CA
- Pricing is optimized for DigiCert certificate purchases — switching CAs increases CLM cost
- Integrations are deepest for DigiCert-issued certificates
- Renewal automation works best for DigiCert certificates
None of this is malicious — it’s the natural result of a CA building a CLM platform. But it means switching away from DigiCert (CA or CLM) becomes progressively harder over time.
QCecuring has no such lock-in vector. Your certificates come from whatever CA you choose. Your data lives on your infrastructure (self-hosted) or in a neutral cloud. Switching CAs requires zero changes to your CLM platform.
FAQ
Q: Can DigiCert TLM manage Let’s Encrypt certificates?
Yes, DigiCert TLM claims CA-agnosticism and can discover and monitor certificates from any CA. However, the automated renewal workflow for Let’s Encrypt certificates (ACME) may not be as seamless as for DigiCert-issued certificates where issuance is native.
Q: Is DigiCert TLM worth it if I only use DigiCert for public certs?
If DigiCert is your sole CA for public certificates AND you also use their private PKI, TLM provides a unified experience. If you use DigiCert for public certs but AD CS for internal and Let’s Encrypt for automation — you’re only getting the “native” experience for a fraction of your certificates.
Q: Can I use QCecuring to manage DigiCert certificates?
Yes. QCecuring integrates with DigiCert’s CertCentral API for automated issuance, renewal, and revocation. You get full lifecycle management for DigiCert certificates without needing DigiCert’s own CLM platform.
Q: Does DigiCert TLM work on-premises?
DigiCert TLM is primarily SaaS. They offer some on-premises components (sensors/agents for discovery), but the management platform itself is cloud-hosted. For fully on-premises or air-gapped requirements, this is a limitation.
Q: Which is better for a multi-cloud environment?
QCecuring — it’s CA-agnostic and treats all environments equally. DigiCert TLM works in multi-cloud but is optimized for environments where DigiCert is the primary CA. If you use AWS ACM in one cloud and DigiCert in another, QCecuring provides more uniform management.
Q: How do G2/Gartner reviews compare?
DigiCert TLM has a 3.8/5 on G2 with only 11 reviews (relatively few for a major vendor). Gartner lists them in the CLM market guide targeting $1B-$10B companies. The limited review count suggests TLM is newer or less widely adopted as a standalone CLM compared to CertCentral (their certificate issuance platform which has many more reviews).
Related Reading:
