The PKI tooling landscape in 2026 spans everything from free open-source CAs you run on a Raspberry Pi to enterprise platforms managing millions of certificates across global infrastructure. Choosing the right tool depends on your scale, compliance requirements, team expertise, and whether you need a CA, a certificate manager, or both.
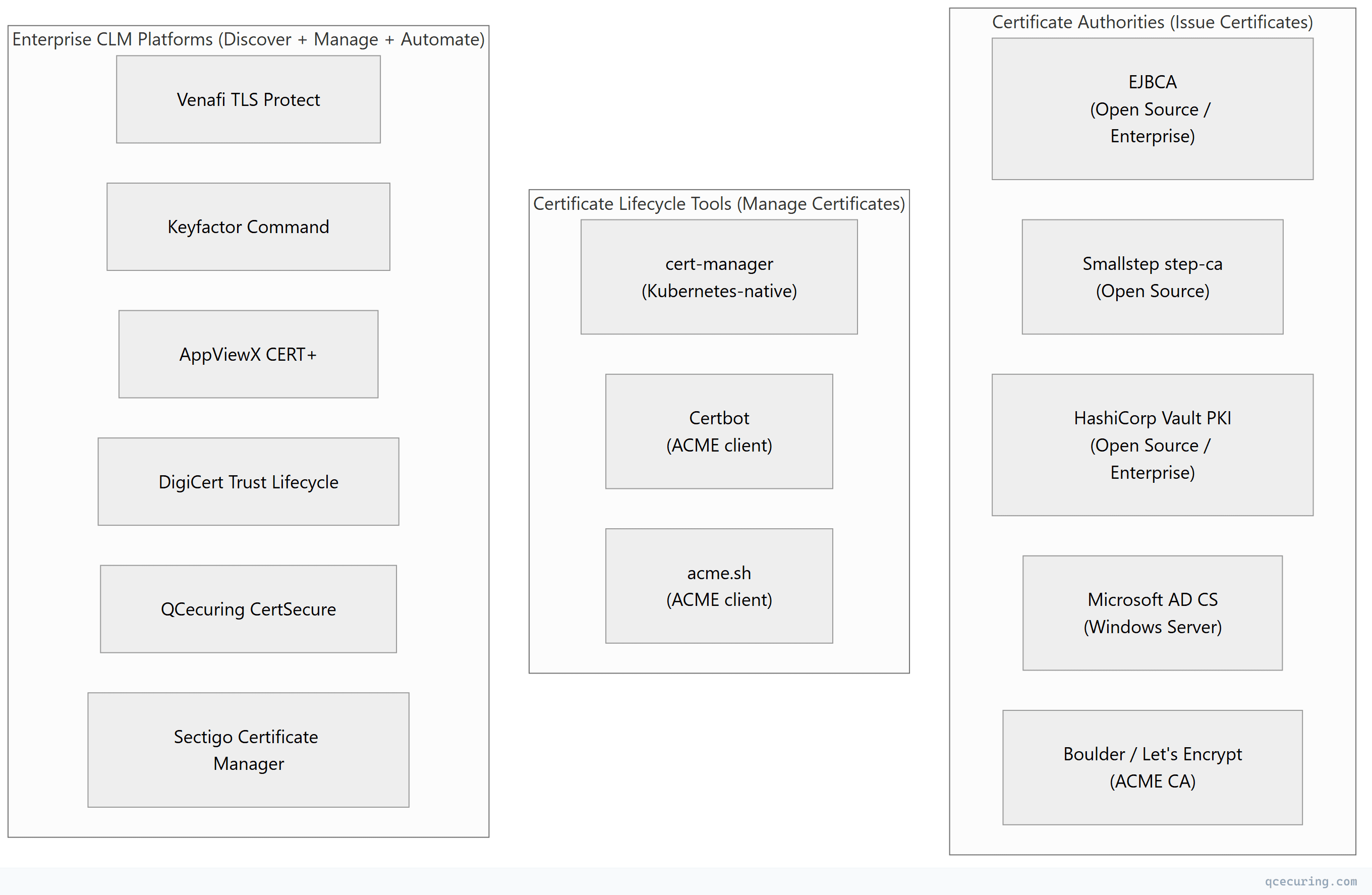
This comparison covers the major options across three categories: open-source CAs, cloud-native tools, and enterprise CLM platforms.
Tool Categories
Open Source CA Comparison
| Feature | EJBCA Community | Smallstep step-ca | HashiCorp Vault PKI | Boulder (Let’s Encrypt) |
|---|---|---|---|---|
| License | LGPL 2.1 | Apache 2.0 | MPL 2.0 (BSL for Enterprise) | MPL 2.0 |
| Primary use | Enterprise internal CA | Modern internal CA | Dynamic short-lived certs | Public ACME CA |
| Protocol support | ACME, SCEP, CMP, EST, REST | ACME, OIDC, SSH | API-only (REST) | ACME only |
| HSM support | Yes (PKCS#11) | Yes (KMS, PKCS#11) | Yes (Enterprise only) | Yes |
| Clustering/HA | Yes (Enterprise) | Yes (with DB backend) | Yes (Raft) | Yes |
| Web UI | Yes (full admin) | Minimal | Vault UI | No |
| Certificate profiles | Extensive (like AD CS templates) | Basic | Role-based | Fixed (DV only) |
| OCSP/CRL | Built-in | Built-in | Built-in | Built-in |
| Kubernetes-native | Via Helm | Via Helm | Via Helm + CSI | No |
| Learning curve | High (Java, complex config) | Low (Go, simple config) | Medium (Vault ecosystem) | N/A (not self-hosted typically) |
| Best for | Regulated enterprises needing full PKI | DevOps teams, internal ACME | Vault-centric environments | Public TLS automation |
When to Choose Each
EJBCA — You need a full-featured CA with certificate profiles, approval workflows, SCEP for devices, and compliance reporting. You have Java expertise and need to replicate AD CS functionality on Linux.
Smallstep step-ca — You want a modern, lightweight internal CA with ACME support. Your team is comfortable with Go/CLI tools. You need SSH certificates alongside X.509.
HashiCorp Vault PKI — You already use Vault for secrets management. You want short-lived certificates issued via API. You need dynamic credentials for microservices.
Boulder — You’re building a public ACME CA (rare). For consuming Let’s Encrypt, use Certbot or cert-manager instead.
Cloud-Native Tools Comparison
| Feature | cert-manager | Certbot | acme.sh | AWS ACM | GCP CAS |
|---|---|---|---|---|---|
| Platform | Kubernetes | Any Linux/macOS | Any Unix | AWS only | GCP only |
| CA support | Any (ACME, Vault, CA, self-signed) | ACME only | ACME only | AWS-managed | GCP-managed |
| Automation | Fully declarative (CRDs) | Cron-based | Cron-based | Fully managed | Fully managed |
| Wildcard certs | Yes (DNS-01) | Yes (DNS-01) | Yes (DNS-01) | Yes | Yes |
| Private CA | Yes (any issuer) | No | No | Yes (ACM PCA, $400/mo) | Yes (CAS, $0.30/cert) |
| Multi-cluster | Per-cluster install | Per-server | Per-server | Per-region | Per-project |
| Cost | Free | Free | Free | Free (public) / $400/mo (private) | $0.30/cert/mo |
| Best for | Kubernetes workloads | Traditional servers | Scripted environments | AWS-native | GCP-native |
Enterprise CLM Platform Comparison
| Feature | Venafi TLS Protect | Keyfactor Command | AppViewX CERT+ | DigiCert TLM | Sectigo CM | QCecuring CertSecure |
|---|---|---|---|---|---|---|
| Discovery | Network + cloud + CT logs | Network + cloud + AD | Network + cloud | DigiCert certs + network | Sectigo certs + network | Network + cloud + K8s |
| Multi-CA | Yes (any CA) | Yes (any CA) | Yes (any CA) | DigiCert-centric | Sectigo-centric | Yes (any CA) |
| Kubernetes | Yes (via integration) | Yes (via integration) | Yes | Limited | Limited | Yes (native) |
| ACME support | Yes | Yes | Yes | Yes | Yes | Yes |
| AD CS integration | Yes | Yes (deep) | Yes | Yes | Yes | Yes |
| Deployment automation | Yes (extensive) | Yes | Yes | Yes | Yes | Yes |
| Post-quantum readiness | CBOM/crypto inventory | Crypto inventory | Limited | Limited | Limited | CBOM + PQC planning |
| Pricing model | Per-certificate | Per-certificate | Per-certificate | Per-certificate | Per-certificate | Per-certificate |
| Deployment | On-prem + SaaS | On-prem + SaaS | On-prem + SaaS | SaaS | SaaS | On-prem + SaaS |
| Best for | Large enterprise, complex environments | Microsoft-heavy, AD CS shops | Multi-cloud, DevOps | DigiCert customers | Sectigo customers | Hybrid, cloud-native |
Selection Decision Framework
By Organization Size
| Size | Recommended Approach | Tools |
|---|---|---|
| Startup (< 50 certs) | ACME automation | Certbot + Let’s Encrypt |
| Small (50-200 certs) | ACME + basic monitoring | cert-manager + Certbot + uptime monitoring |
| Medium (200-2,000 certs) | CLM platform or open-source CA | Smallstep/EJBCA + CLM platform |
| Large (2,000-20,000 certs) | Enterprise CLM | Venafi / Keyfactor / QCecuring + existing CAs |
| Enterprise (20,000+ certs) | Enterprise CLM + federated model | Enterprise platform + local automation |
By Primary Environment
| Environment | Best Tools |
|---|---|
| Pure Kubernetes | cert-manager + Vault PKI or step-ca |
| Pure AWS | ACM + ACM PCA (or cert-manager on EKS) |
| Pure Azure | Azure Key Vault + App Service Managed Certs |
| Windows/AD-heavy | AD CS + enterprise CLM for visibility |
| Multi-cloud | Enterprise CLM platform (vendor-neutral) |
| Hybrid (on-prem + cloud) | Enterprise CLM + cert-manager + AD CS |
By Compliance Requirement
| Requirement | Must-Have |
|---|---|
| FIPS 140-2/3 | HSM-backed CA (EJBCA + HSM, Vault Enterprise + HSM) |
| PCI DSS | Audit trail, key rotation tracking, quarterly scans |
| HIPAA | Encryption inventory, access controls, audit logs |
| FedRAMP | FIPS-validated crypto, NIST SP 800-52 compliance |
| SOC 2 | Change management, monitoring, incident response |
Total Cost of Ownership (3-Year)
| Solution | License/Subscription | Infrastructure | Personnel | 3-Year TCO |
|---|---|---|---|---|
| Certbot + scripts | $0 | $0 | 0.5 FTE ($225K) | $225K |
| cert-manager + Vault | $0 (OSS) | $20K/yr | 0.5 FTE ($225K) | $285K |
| EJBCA Enterprise | $50K/yr | $30K/yr | 0.3 FTE ($135K) | $375K |
| Enterprise CLM (mid-tier) | $80K/yr | Included (SaaS) | 0.2 FTE ($90K) | $330K |
| Enterprise CLM (top-tier) | $200K/yr | Included (SaaS) | 0.2 FTE ($90K) | $690K |
Hidden costs of “free” tools:
- Engineering time to build integrations
- On-call burden for certificate-related incidents
- Compliance audit preparation (manual evidence gathering)
- Outage costs when automation gaps cause expiry
Migration Paths
From Spreadsheets to Automation
- Week 1-2: Deploy discovery tool (even a free one) to build inventory
- Week 3-4: Identify critical certificates (expiring soon, high-value systems)
- Month 2: Automate renewal for the easiest targets (ACME-capable servers)
- Month 3: Evaluate CLM platforms with your real inventory data
- Month 4-6: Deploy platform, migrate remaining certificates
From AD CS to Modern PKI
- Keep AD CS for Windows auto-enrollment (domain controllers, user certs)
- Add ACME CA (step-ca or EJBCA) for Linux/cloud workloads
- Deploy CLM platform for unified visibility across both
- Gradually migrate workloads from AD CS to ACME where possible
- AD CS becomes one CA among many, not the only CA
FAQ
Q: Can I use multiple tools together?
Yes — and most organizations do. A common stack: AD CS for Windows, cert-manager for Kubernetes, Certbot for standalone Linux servers, and an enterprise CLM platform for visibility and compliance across all of them. The CLM platform doesn’t replace the issuance tools; it orchestrates them.
Q: Is Vault PKI a replacement for a dedicated CA like EJBCA?
For short-lived, API-issued certificates (microservices, mTLS) — yes. For traditional PKI needs (long-lived certs, SCEP for devices, complex certificate profiles, CRL distribution) — no. Vault PKI is optimized for dynamic, ephemeral certificates. EJBCA is optimized for traditional enterprise PKI.
Q: Do I need an enterprise CLM if I only use Let’s Encrypt?
If all your certificates are Let’s Encrypt and managed by Certbot/cert-manager with proper monitoring, you may not need a CLM platform. But most organizations also have internal certificates (AD CS, self-signed), cloud-managed certificates (ACM, Azure), and device certificates that Let’s Encrypt doesn’t cover. The CLM provides visibility across all of them.
Q: What’s the difference between a CA and a CLM?
A CA (Certificate Authority) issues certificates. A CLM (Certificate Lifecycle Manager) manages certificates regardless of which CA issued them. Think of it as: CA = factory that makes certificates. CLM = supply chain management that tracks every certificate from creation to destruction.
Q: How do open-source tools handle compliance reporting?
Most open-source CAs (EJBCA, Vault, step-ca) provide audit logs but not compliance-formatted reports. You’ll need to build reporting on top (ELK stack, Grafana dashboards, custom scripts). Enterprise CLM platforms include pre-built compliance reports for PCI DSS, HIPAA, SOC 2, etc.
Q: Which tool has the best Kubernetes integration?
cert-manager is purpose-built for Kubernetes and has the deepest integration (CRDs, Ingress annotations, Gateway API). Enterprise CLM platforms integrate with cert-manager rather than replacing it — they add cross-cluster visibility and policy enforcement on top.
Related Reading:
