Sectigo is the world’s largest commercial certificate authority by volume. Originally Comodo CA (the name behind millions of DV certificates), it was acquired by Francisco Partners in 2017 and rebranded to Sectigo in 2018. Their Certificate Manager (SCM) platform evolved from a tool for managing Sectigo-issued certificates into a CA-agnostic CLM that also manages certificates from DigiCert, Let’s Encrypt, Microsoft AD CS, AWS, and Google.
Like DigiCert TLM, Sectigo SCM is a CA-bundled CLM — it works best when you’re also buying Sectigo certificates. But unlike DigiCert (which targets the high-assurance enterprise market), Sectigo has historically been the volume player — more certificates, lower price points, broader market reach from SMB to enterprise.
Company Backgrounds
Sectigo
Sectigo’s history is intertwined with Comodo, one of the internet’s original certificate authorities. The CA business was carved out from Comodo Group and acquired by Francisco Partners (a technology-focused PE firm) in October 2017. The rebrand to Sectigo happened in November 2018 to distance from Comodo’s mixed reputation (Comodo had both a CA business and a controversial security software business).
Key facts:
- Founded: 1998 as Comodo CA, rebranded 2018 as Sectigo
- Headquarters: Roseland, New Jersey
- Ownership: Francisco Partners (private equity)
- Market position: Largest commercial CA by certificate volume
- Products: SCM Enterprise (CLM), SCM Pro (SMB), public/private CA, code signing, email certificates
- Architecture: Cloud-native SaaS platform
- Integrations: 50+ technology integrations
- Recent: Added Private PQC certificates (April 2026), strong 47-day cert messaging
- Tiers: SCM Pro (SMB, flat-rate DV/OV) and SCM Enterprise (full CLM)
- Gartner: Ranked #3 in CLM market (behind Venafi and Keyfactor)
Sectigo’s positioning in 2026: They’ve leaned heavily into the 47-day certificate narrative — positioning SCM as the automation platform that makes short-lived certificates manageable. They’ve also been early with PQC, offering private post-quantum certificates within SCM for testing. Their SCM Pro tier targets SMBs who need basic automation without enterprise complexity.
QCecuring
QCecuring is a pure-play certificate and key management company with no CA business. They don’t issue certificates — they manage them regardless of source.
Key facts:
- Modern architecture: Spring Boot + MongoDB + Angular, single JAR
- Products: CertSecure (CLM), SSH KLM, Code Signing, PKI-aaS, HSM-aaS, CBOM
- Focus: Mid-market to enterprise, government, MSPs
- No CA revenue — zero incentive to push any specific CA
- Self-hosted, cloud, or hybrid deployment
The Sectigo SCM Tiers
Sectigo offers two distinct products that serve different markets:
| SCM Pro | SCM Enterprise | |
|---|---|---|
| Target | SMBs, small IT teams | Large enterprise |
| Certificates | DV and OV (Sectigo-issued) | Any CA (CA-agnostic) |
| Pricing | Flat-rate, domain-based plans | Custom enterprise pricing |
| Discovery | Limited | Full network + cloud scanning |
| Automation | ACME-based | Full lifecycle automation |
| Multi-CA | Sectigo only | Yes (AD CS, AWS, GCP, DigiCert, etc.) |
| Deployment | SaaS only | SaaS (with agents/connectors) |
| Onboarding | Guided, self-service | Professional services available |
QCecuring competes primarily with SCM Enterprise — the full-featured CA-agnostic CLM platform. SCM Pro is a different product for a different market (basic DV/OV automation for small businesses).
Architecture Comparison
| Component | QCecuring | Sectigo SCM Enterprise |
|---|---|---|
| Deployment | Self-hosted (JAR/Docker) or SaaS | SaaS only (cloud-native) |
| Database | MongoDB | Cloud-managed (not disclosed) |
| Agent model | Lightweight mTLS agents | Sectigo Connector + MS Agent |
| On-premises option | Yes (full platform) | No (agents only, platform is cloud) |
| Air-gapped support | Yes | No (requires cloud connectivity) |
| API | REST (OpenAPI) | REST API |
| Multi-tenancy | Yes (MSP-friendly) | Yes (organization/department model) |
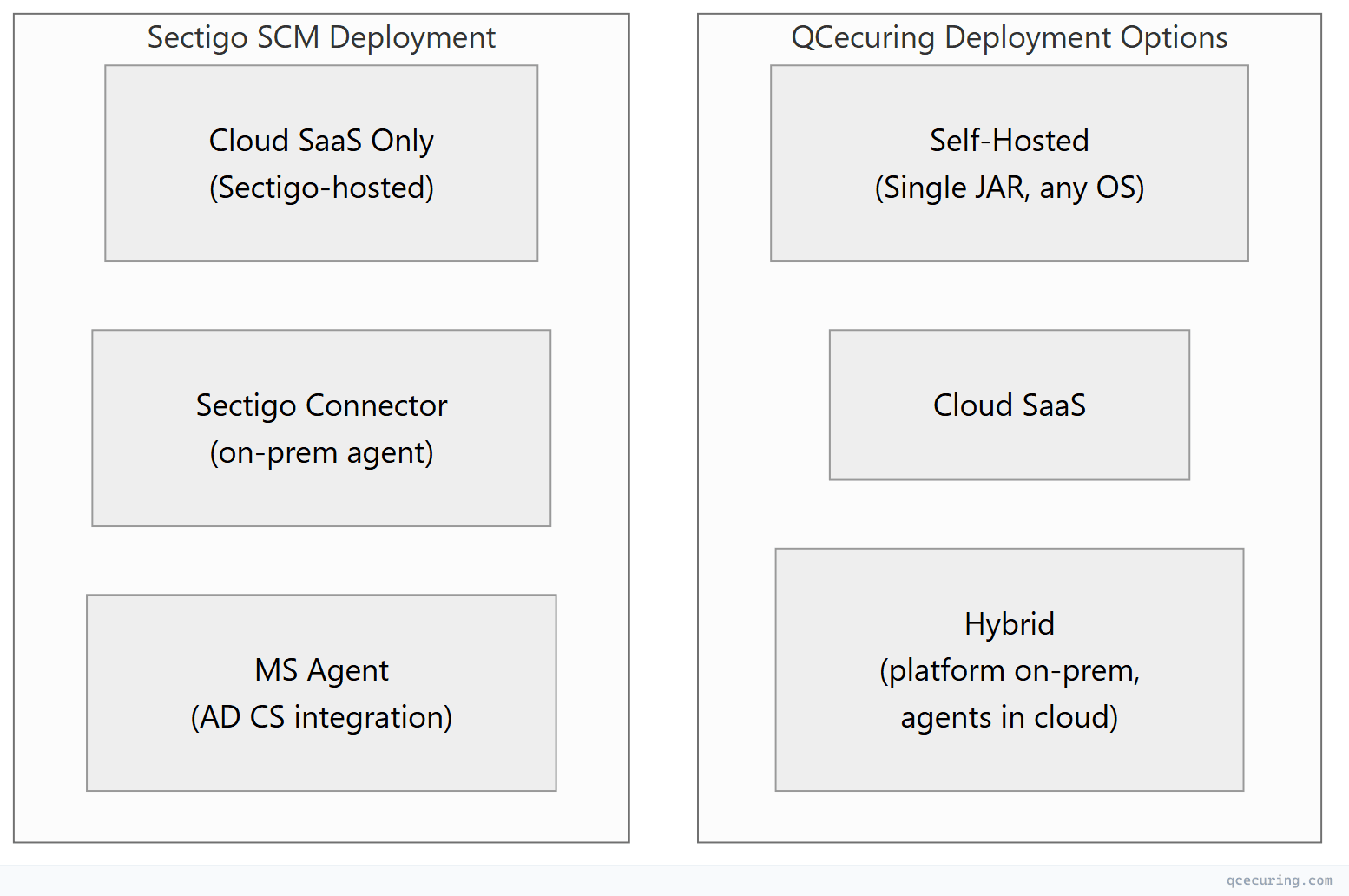
The deployment model is a key differentiator. Sectigo SCM is SaaS-only — your certificate management data lives in Sectigo’s cloud. For organizations with data sovereignty requirements, air-gapped environments, or strict policies about certificate metadata leaving their network, this is a hard blocker. QCecuring offers full self-hosted deployment where nothing leaves your infrastructure.
Feature-by-Feature Comparison
Discovery
| Capability | QCecuring | Sectigo SCM Enterprise |
|---|---|---|
| Network port scanning | Yes (7 methods) | Yes |
| Cloud API (AWS, Azure, GCP) | Yes (native) | Yes |
| AD CS discovery | Yes | Yes (via MS Agent) |
| Kubernetes | Roadmap | Limited |
| Certificate Transparency logs | Yes | Yes |
| Continuous scanning | Yes | Yes |
| CBOM (cryptographic inventory) | Yes (core feature) | No |
Automation & Lifecycle
| Capability | QCecuring | Sectigo SCM Enterprise |
|---|---|---|
| ACME protocol | Yes (full v2) | Yes |
| Sectigo certificate issuance | Yes (via API) | Native (instant) |
| Other CA issuance | Yes (equal) | Yes (CA-agnostic) |
| AD CS enrollment | Yes | Yes (via MS Agent) |
| Zero-touch renewal | Yes | Yes |
| Deployment automation | Yes | Yes (50+ integrations) |
| Approval workflows | Yes | Yes |
| Self-service portal | Yes | Yes |
| REST API | Yes | Yes |
| 47-day certificate support | Yes | Yes (heavily marketed) |
Post-Quantum Readiness
| Capability | QCecuring | Sectigo SCM |
|---|---|---|
| CBOM (cryptographic inventory) | Yes (core) | No |
| Private PQC certificates | Roadmap | Yes (launched April 2026) |
| PQC algorithm testing | Yes (via CBOM) | Yes (issue PQC test certs in SCM) |
| Crypto-agility assessment | Yes | Limited |
| Migration planning | Yes | Limited |
Sectigo’s PQC advantage: They can issue private PQC certificates (ML-DSA, ML-KEM) directly within SCM for testing. This lets organizations test post-quantum certificates in live environments without deploying new infrastructure. QCecuring’s PQC story is at the inventory/planning level (CBOM) rather than certificate issuance.
Compliance & Reporting
| Capability | QCecuring | Sectigo SCM |
|---|---|---|
| Pre-built compliance reports | Yes (PCI, HIPAA, SOC 2, DORA) | Yes |
| CBOM for regulatory evidence | Yes | No |
| Audit trail | Complete | Complete |
| RBAC | Yes | Yes (organization/department model) |
| SIEM integration | Yes | Yes |
| EU compliance (DORA, CRA) | Yes (built-in mapping) | Limited |
Where QCecuring Wins
1. Self-Hosted / On-Premises Deployment
Sectigo SCM is cloud-only. The platform, your certificate inventory, automation rules, and audit logs all live in Sectigo’s cloud. QCecuring offers full self-hosted deployment — single JAR on your own infrastructure, air-gapped capable, zero external dependencies.
For government, defense, healthcare (HIPAA), and organizations with strict data residency policies, this is often a dealbreaker for Sectigo.
2. True CA-Agnosticism (No CA Revenue Bias)
Sectigo is a CA first, CLM second. Their business model depends on you buying Sectigo certificates. While SCM Enterprise manages other CAs, the tightest integration, best pricing, and fastest issuance come with Sectigo certificates.
QCecuring has no CA business. Every CA integration gets equal attention. There’s no commercial incentive to steer you toward any specific CA.
3. CBOM and Crypto-Agility Assessment
QCecuring’s CBOM provides a complete cryptographic inventory — algorithms, key sizes, protocols, and compliance mapping. This is essential for DORA, CRA, and CNSA 2.0 compliance. Sectigo doesn’t offer equivalent cryptographic inventory capabilities.
4. Cost for Non-Sectigo Certificate Environments
If most of your certificates come from Let’s Encrypt, AD CS, or other CAs, Sectigo SCM’s value proposition weakens — you’re paying for a CLM platform optimized for Sectigo certificates without the bundle benefit. QCecuring’s pricing is independent of which CA you use.
5. MSP / Multi-Tenant Model
QCecuring’s architecture supports true multi-tenancy for MSPs managing certificates across multiple clients. Sectigo’s organization/department model works for single enterprises but isn’t designed for MSP use cases with strict tenant isolation.
Where Sectigo Wins
1. Integration Breadth (50+ Integrations)
Sectigo has invested heavily in integrations — 50+ technology partners covering load balancers, cloud platforms, DevOps tools, and network devices. Their connector ecosystem is mature and well-documented.
2. Private PQC Certificates (First-Mover)
Sectigo launched private PQC certificates within SCM in April 2026 — organizations can issue and manage post-quantum certificates using existing workflows. This is a genuine first-mover advantage for organizations that want to test PQC in production environments today.
3. SCM Pro for SMBs
Sectigo offers a simplified, flat-rate CLM product (SCM Pro) for small businesses that just need basic DV/OV automation. QCecuring doesn’t have an equivalent ultra-simplified tier for very small organizations (< 50 certificates).
4. Volume Certificate Pricing
As the largest commercial CA by volume, Sectigo offers aggressive certificate pricing — especially for DV certificates. If you’re buying thousands of certificates annually, the combined SCM + certificate bundle pricing can be very competitive.
5. 47-Day Certificate Messaging
Sectigo has been the most vocal vendor about 47-day certificate readiness. They endorsed Apple’s proposal and have built their entire 2026 marketing around “automation is no longer optional.” Their platform is well-tested for high-frequency renewal scenarios.
6. Zero Infrastructure (Pure SaaS)
For organizations that don’t want to manage any infrastructure — no servers, no databases, no patching — Sectigo’s pure SaaS model means zero operational overhead for the CLM platform itself. You just use it.
Pricing Comparison
| QCecuring | Sectigo SCM | |
|---|---|---|
| Model | Platform license | Platform + certificate volume |
| Certificate cost | Pay your CA directly | Bundled (discount with Sectigo certs) |
| SMB tier | Mid-market entry point | SCM Pro (flat-rate, domain-based) |
| Enterprise tier | Competitive | Custom pricing |
| Self-hosted | Yes (included) | No (SaaS only) |
| Infrastructure cost | Minimal (single JAR) | Zero (SaaS) |
| Year 1 TCO | $$ | $$-$$$ (depends on cert volume) |
Decision Framework
| If You… | Choose |
|---|---|
| Need self-hosted / on-premises / air-gapped | QCecuring |
| Buy most certificates from Sectigo already | Sectigo SCM |
| Need CBOM for compliance (DORA, CRA, CNSA 2.0) | QCecuring |
| Want zero infrastructure (pure SaaS) | Sectigo SCM |
| Are an MSP managing multiple clients | QCecuring |
| Want to test PQC certificates in production now | Sectigo SCM |
| Use primarily Let’s Encrypt / AD CS / Vault | QCecuring |
| Need 50+ pre-built integrations | Sectigo SCM |
| Have data sovereignty / residency requirements | QCecuring |
| Are a small business needing basic DV automation | Sectigo SCM Pro |
| Want CA-agnostic with no vendor bias | QCecuring |
| Need EU compliance mapping built-in | QCecuring |
The CA-Bundled CLM Pattern (Sectigo vs DigiCert vs QCecuring)
Both Sectigo and DigiCert follow the same model: CA that also sells CLM. The comparison:
| Sectigo SCM | DigiCert TLM | QCecuring | |
|---|---|---|---|
| CA heritage | Volume CA (DV/OV focus) | High-assurance CA (OV/EV focus) | No CA |
| Certificate pricing | Aggressive (volume discounts) | Premium (enterprise pricing) | N/A (you choose your CA) |
| CLM approach | CA-agnostic (but optimized for Sectigo) | CA-agnostic (but optimized for DigiCert) | Truly CA-agnostic |
| Target market | SMB to enterprise | Enterprise ($1B+ companies) | Mid-market to enterprise |
| Deployment | SaaS only | SaaS primarily | Self-hosted or SaaS |
| PQC | Private PQC certs (issuance) | PQC test certs (issuance) | CBOM + migration planning |
| Lock-in risk | Medium (cert pricing tied to CLM) | High (private PKI dependency) | Low (no CA dependency) |
FAQ
Q: Can Sectigo SCM manage Let’s Encrypt certificates?
Yes. SCM Enterprise is CA-agnostic and can discover, monitor, and manage certificates from any CA including Let’s Encrypt. However, automated renewal for Let’s Encrypt uses ACME protocol which works independently of SCM — the value SCM adds is visibility and monitoring rather than issuance automation (which Certbot/cert-manager already handle).
Q: Is Sectigo SCM the same as Comodo Certificate Manager?
Sectigo SCM is the successor to Comodo Certificate Manager (CCM). It was rebuilt as a cloud-native platform after the Sectigo rebrand. If you’re on legacy CCM, Sectigo offers migration paths to SCM. The architecture is fundamentally different — CCM was older, SCM is modern cloud-native.
Q: Does Sectigo SCM work without buying Sectigo certificates?
Yes — SCM Enterprise is CA-agnostic. But the product experience and pricing are optimized for Sectigo certificate customers. If you’re using exclusively non-Sectigo CAs, you’re paying for a platform whose deepest integrations you won’t use.
Q: Which is better for a startup or small business?
Sectigo SCM Pro is purpose-built for SMBs — flat-rate pricing, guided onboarding, DV/OV automation. QCecuring’s entry point is higher (mid-market). For very small organizations (< 50 certs), SCM Pro or just Certbot may be sufficient.
Q: How does Sectigo’s PQC offering compare to QCecuring’s?
Different layers. Sectigo can issue PQC certificates (ML-DSA signed) for testing within SCM — useful for organizations that want to deploy and test PQC certs in live environments. QCecuring provides cryptographic inventory (CBOM) and migration planning — useful for understanding your current crypto posture and planning the transition. Ideally you need both: inventory (QCecuring) + test certificates (Sectigo or another PQC-capable CA).
Q: Can I use QCecuring to manage Sectigo-issued certificates?
Yes. QCecuring integrates with Sectigo’s API for automated issuance, renewal, and revocation. You get full lifecycle management for Sectigo certificates without needing Sectigo’s own CLM platform.
Related Reading:
