NIST SP 800-57 is the foundational document for cryptographic key management. Published in three parts, it defines how keys should be generated, used, rotated, archived, and destroyed — and critically, how long each key should remain in active use (the “crypto period”). If your organization handles regulated data, your auditors will reference this document. If you’re designing a key management system, this is where you start.
This guide covers the practical implementation of SP 800-57’s recommendations — not just what the standard says, but how to map it to real systems like AWS KMS, HashiCorp Vault, and enterprise key managers.
SP 800-57 Structure
The standard is published in three parts:
| Part | Title | Covers |
|---|---|---|
| Part 1 (Rev 5) | General | Key types, crypto periods, states, algorithm recommendations |
| Part 2 (Rev 1) | Best Practices for Key Management Organizations | Policies, roles, documentation, audit |
| Part 3 (Rev 1) | Application-Specific Key Management Guidance | Per-protocol guidance (TLS, IPsec, etc.) |
Part 1 is what most engineers need. It answers: “What key should I use, how long should it live, and what do I do with it when it expires?”
Key Types and Their Purposes
SP 800-57 categorizes keys by their function:
| Key Type | Purpose | Example |
|---|---|---|
| Private signature key | Create digital signatures | CA signing key, code signing key |
| Public signature verification key | Verify digital signatures | Certificate public key |
| Symmetric authentication key | Generate/verify MACs | HMAC keys for API authentication |
| Private authentication key | Prove identity | TLS client certificate key |
| Symmetric data encryption key (DEK) | Encrypt/decrypt data | AES key for database encryption |
| Symmetric key-wrapping key (KEK) | Protect other keys | Master key that encrypts DEKs |
| Key-agreement private key | Establish shared secrets | ECDH private key in TLS |
| Key-transport private key | Decrypt transported keys | RSA private key (legacy key exchange) |
| Random bit generator (RBG) key | Seed random number generators | DRBG seed key |
Crypto Periods (Key Lifetimes)
The crypto period is the time span during which a key is authorized for use. SP 800-57 defines recommended crypto periods based on key type and security requirements:
Recommended Crypto Periods
| Key Type | Originator Usage Period | Recipient Usage Period | Total Lifetime |
|---|---|---|---|
| Symmetric DEK | ≤ 2 years | ≤ 2 years beyond originator | ≤ 4 years |
| Symmetric authentication key | ≤ 2 years | ≤ 2 years + verification period | ≤ 4 years |
| Symmetric KEK (key-wrapping) | ≤ 2 years | ≤ 2 years beyond originator | ≤ 4 years |
| Asymmetric signature (private) | 1-3 years | N/A (private key signs only) | 1-3 years |
| Asymmetric signature (public) | N/A | Indefinite (verification) | Certificate lifetime |
| Key-agreement (private) | 1-2 years | N/A | 1-2 years |
| Key-transport (private) | ≤ 2 years | ≤ 2 years beyond originator | ≤ 4 years |
| CA signing key | Depends on hierarchy level | N/A | 5-20 years |
| Root CA key | 10-20 years | N/A | 10-20 years |
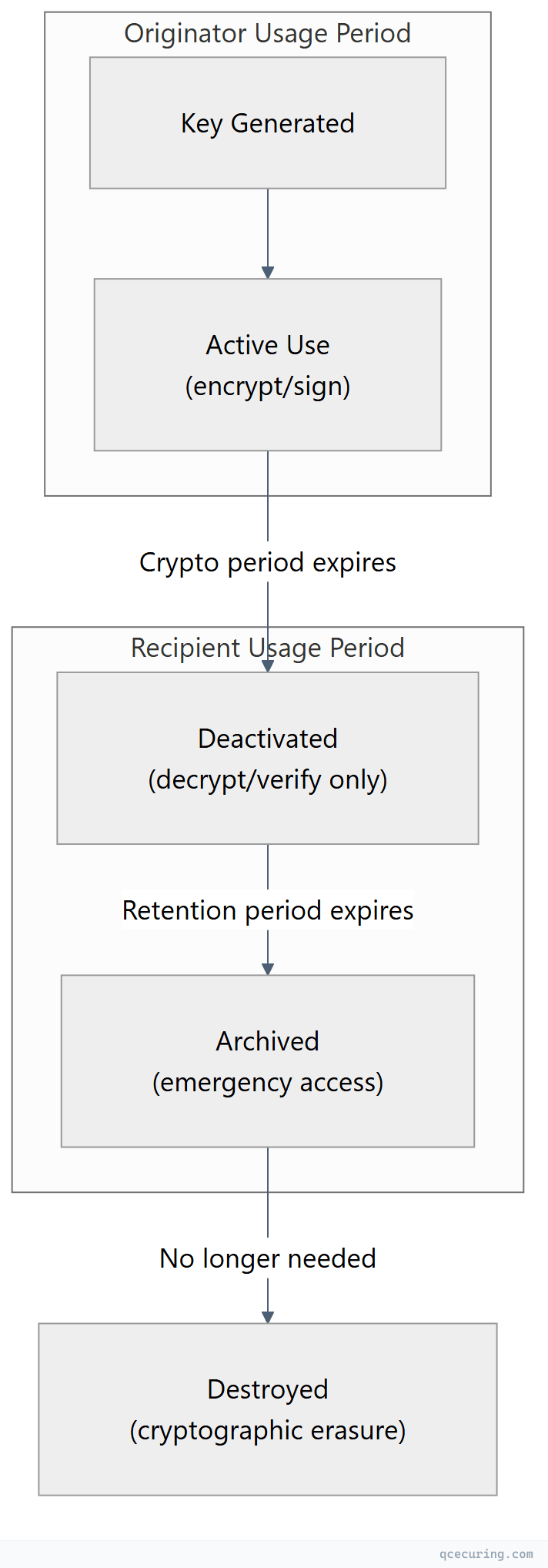
Key distinction: The originator usage period is how long you can use the key to create new protected data (encrypt, sign). The recipient usage period is how long the key remains available to process existing protected data (decrypt, verify). A key can be “deactivated” for new operations while still being available for decryption.
Factors That Shorten Crypto Periods
SP 800-57 lists conditions that require shorter key lifetimes:
- High-value data: Financial transactions, classified information
- High-volume encryption: Keys encrypting large amounts of data wear out faster (statistical attacks)
- Increased threat level: Suspected compromise, new attack techniques
- Regulatory requirements: PCI DSS, HIPAA may mandate shorter periods
- Algorithm aging: As computational power increases, keys become weaker over time
Key States
SP 800-57 defines a state machine for cryptographic keys:
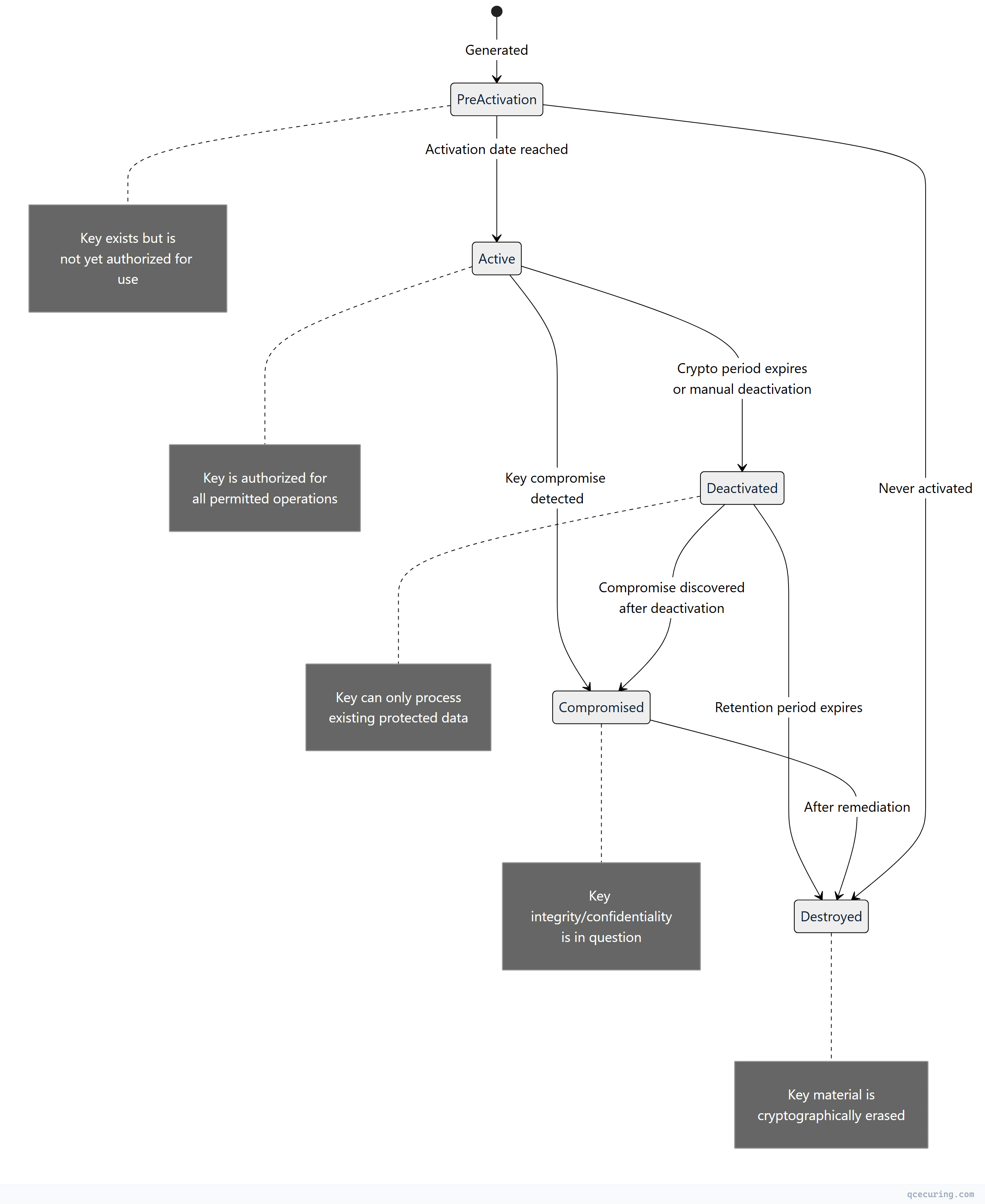
State Transitions in Practice
| Transition | Trigger | Action Required |
|---|---|---|
| Pre-activation → Active | Scheduled activation date | Verify key integrity, enable for use |
| Active → Deactivated | Crypto period expiry | Stop new encryption/signing, keep for decryption |
| Active → Compromised | Incident detection | Immediate: stop all use, assess impact, re-encrypt data |
| Deactivated → Destroyed | Retention period ends | Cryptographic erasure (zeroize) |
| Compromised → Destroyed | After data re-protection | Zeroize, document incident |
Algorithm Recommendations (2026)
SP 800-57 Part 1 Rev 5 (2020) provides algorithm guidance. Combined with SP 800-131A Rev 2 and CNSA 2.0:
Symmetric Algorithms
| Algorithm | Key Size | Status | Use Until |
|---|---|---|---|
| AES-256 | 256 bits | Approved | Indefinite (quantum-safe at 128-bit effective) |
| AES-192 | 192 bits | Approved | Indefinite |
| AES-128 | 128 bits | Approved | Through 2030 (64-bit effective post-quantum) |
| 3DES | 168 bits | Deprecated | Do not use for new systems |
Asymmetric Algorithms
| Algorithm | Key Size | Security Strength | Status |
|---|---|---|---|
| RSA-2048 | 2048 bits | 112 bits | Acceptable through 2030 |
| RSA-3072 | 3072 bits | 128 bits | Recommended minimum |
| RSA-4096 | 4096 bits | ~140 bits | Recommended for long-lived keys |
| ECDSA P-256 | 256 bits | 128 bits | Recommended |
| ECDSA P-384 | 384 bits | 192 bits | Recommended for high-security |
| Ed25519 | 256 bits | 128 bits | Recommended (not yet in SP 800-57) |
| ML-KEM-768 | — | 192 bits | Approved (FIPS 203, post-quantum) |
| ML-DSA-65 | — | 192 bits | Approved (FIPS 204, post-quantum) |
Hash Functions
| Algorithm | Output Size | Security Strength | Status |
|---|---|---|---|
| SHA-256 | 256 bits | 128 bits (collision) | Approved |
| SHA-384 | 384 bits | 192 bits (collision) | Approved |
| SHA-512 | 512 bits | 256 bits (collision) | Approved |
| SHA-3-256 | 256 bits | 128 bits (collision) | Approved |
| SHA-1 | 160 bits | < 80 bits (broken) | NOT approved for signatures |
Mapping SP 800-57 to Real Systems
AWS KMS
| SP 800-57 Concept | AWS KMS Implementation |
|---|---|
| Key generation | CreateKey (hardware RNG in HSM) |
| Crypto period | Key rotation policy (annual automatic) |
| Active state | Key enabled, KeyState: Enabled |
| Deactivated state | DisableKey (can still decrypt) |
| Destroyed state | ScheduleKeyDeletion (7-30 day waiting period) |
| Key-wrapping key | KMS CMK wraps data keys (envelope encryption) |
| Audit trail | CloudTrail logs every key operation |
# Set rotation policy (annual — meets SP 800-57 for most use cases)
aws kms enable-key-rotation --key-id alias/my-key
# Disable a key (deactivate — can still decrypt existing data)
aws kms disable-key --key-id alias/my-key
# Schedule destruction (minimum 7-day waiting period)
aws kms schedule-key-deletion --key-id alias/my-key --pending-window-in-days 30HashiCorp Vault
| SP 800-57 Concept | Vault Implementation |
|---|---|
| Key generation | Transit engine create or PKI generate |
| Crypto period | auto_rotate_period on transit keys |
| Active state | Latest key version (encrypts + decrypts) |
| Deactivated state | Older key versions (decrypt only) |
| Destroyed state | vault write transit/keys/name/config min_decryption_version=N |
| Key-wrapping key | Vault master key (wraps all stored keys) |
| Audit trail | Audit device (file, syslog, socket) |
# Set auto-rotation (90-day crypto period)
vault write transit/keys/my-key auto_rotate_period=90d
# Check key versions and rotation history
vault read transit/keys/my-key
# Destroy old key versions (after re-wrapping all data)
vault write transit/keys/my-key/config min_decryption_version=5
# Versions 1-4 are now destroyed — data encrypted with them is unrecoverableKMIP-Compliant Key Managers
| SP 800-57 Concept | KMIP Operation |
|---|---|
| Key generation | Create |
| Pre-activation | Object state: Pre-Active |
| Active | Activate → state: Active |
| Deactivated | Deactivate → state: Deactivated |
| Compromised | Revoke → state: Compromised |
| Destroyed | Destroy → state: Destroyed |
| Crypto period | ActivationDate + DeactivationDate attributes |
Implementing Key Lifecycle Policies
Policy Document Template
# key-management-policy.yaml
policy:
name: "Enterprise Key Management Policy"
version: "2.0"
reference: "NIST SP 800-57 Part 1 Rev 5"
last_reviewed: "2026-05-01"
key_classes:
- name: "Data Encryption Keys (DEK)"
algorithm: "AES-256-GCM"
crypto_period: "365 days"
rotation: "automatic"
storage: "AWS KMS / Vault Transit"
destruction: "30 days after last decryption need"
- name: "Key Encryption Keys (KEK)"
algorithm: "AES-256"
crypto_period: "730 days"
rotation: "manual with approval"
storage: "HSM (PKCS#11)"
destruction: "After all wrapped keys are re-wrapped"
- name: "TLS Certificate Keys"
algorithm: "ECDSA P-256"
crypto_period: "90 days (public CA) / 365 days (internal)"
rotation: "automatic via cert-manager / ACME"
storage: "Kubernetes Secrets / Vault PKI"
destruction: "Immediate after certificate expiry + 30 days"
- name: "CA Signing Keys"
algorithm: "RSA-4096 or ECDSA P-384"
crypto_period: "5 years (issuing) / 20 years (root)"
rotation: "manual key ceremony"
storage: "HSM (FIPS 140-2 Level 3)"
destruction: "After all issued certificates expire"
- name: "Code Signing Keys"
algorithm: "RSA-4096 or ECDSA P-384"
crypto_period: "3 years"
rotation: "manual with dual control"
storage: "HSM or cloud signing service"
destruction: "After timestamp validity period"
roles:
key_custodian: "Generates and stores keys"
key_owner: "Authorizes key use and rotation"
key_user: "Uses keys for cryptographic operations"
auditor: "Reviews key usage logs and compliance"Automation Script: Key Rotation Compliance Check
#!/usr/bin/env python3
"""Check key rotation compliance against SP 800-57 crypto periods."""
import boto3
from datetime import datetime, timedelta
# Define crypto periods per key class
CRYPTO_PERIODS = {
"DEK": timedelta(days=365),
"KEK": timedelta(days=730),
"SIGNING": timedelta(days=1095),
"TLS": timedelta(days=90),
}
def check_kms_key_rotation(key_id: str, key_class: str) -> dict:
"""Check if a KMS key exceeds its crypto period."""
kms = boto3.client('kms')
key_info = kms.describe_key(KeyId=key_id)
creation_date = key_info['KeyMetadata']['CreationDate']
key_state = key_info['KeyMetadata']['KeyState']
age = datetime.now(creation_date.tzinfo) - creation_date
max_period = CRYPTO_PERIODS.get(key_class, timedelta(days=365))
rotation_status = kms.get_key_rotation_status(KeyId=key_id)
return {
"key_id": key_id,
"key_class": key_class,
"age_days": age.days,
"max_period_days": max_period.days,
"compliant": age <= max_period,
"auto_rotation": rotation_status['KeyRotationEnabled'],
"state": key_state,
"action_needed": "ROTATE" if age > max_period else "OK"
}
# Check all keys
kms = boto3.client('kms')
keys = kms.list_keys()['Keys']
non_compliant = []
for key in keys:
result = check_kms_key_rotation(key['KeyId'], "DEK")
if not result['compliant']:
non_compliant.append(result)
print(f"NON-COMPLIANT: {result['key_id']} — {result['age_days']} days old "
f"(max: {result['max_period_days']})")
if not non_compliant:
print("All keys within crypto period limits.")Key Destruction Requirements
SP 800-57 requires that key destruction be irreversible. The method depends on the storage medium:
| Storage Medium | Destruction Method | Verification |
|---|---|---|
| HSM | Zeroize command (PKCS#11 C_DestroyObject) | HSM audit log confirms deletion |
| AWS KMS | ScheduleKeyDeletion (7-30 day wait) | CloudTrail event |
| Vault | min_decryption_version or delete | Audit log |
| Software (file) | Overwrite with random data, then delete | Not fully reliable on SSDs |
| SSD/Flash | Cryptographic erase (ATA Secure Erase) | Vendor-specific verification |
| Paper (key shares) | Cross-cut shredding | Witnessed destruction |
Critical: On SSDs and flash storage, simple file deletion doesn’t destroy the key — wear leveling may retain copies. Use full-disk encryption with a separate KEK, then destroy the KEK to render all data (including old key copies) unrecoverable.
Compliance Mapping
| Regulation | SP 800-57 Relevance |
|---|---|
| PCI DSS 4.0 (Req 3.6-3.7) | Key management procedures must align with SP 800-57 crypto periods |
| HIPAA (§164.312) | Encryption key management for PHI — SP 800-57 is the referenced standard |
| FedRAMP | Directly requires SP 800-57 compliance for key management |
| SOX (Section 404) | Key management controls must be documented and auditable |
| GDPR (Art 32) | “State of the art” encryption — SP 800-57 defines the state of the art |
| FIPS 140-3 | Key lifecycle management within cryptographic modules |
| ISO 27001 (A.10) | Cryptographic controls — SP 800-57 provides the implementation detail |
FAQ
Q: Is SP 800-57 mandatory for private companies?
Not directly — it’s mandatory for federal agencies and their contractors. However, it’s the de facto standard that auditors reference for PCI DSS, HIPAA, SOC 2, and ISO 27001 compliance. If an auditor asks “what’s your key rotation policy based on?”, SP 800-57 is the defensible answer.
Q: What’s the difference between crypto period and key lifetime?
The crypto period is the time a key is authorized for its primary function (encrypting new data, signing). The key lifetime includes the crypto period plus any additional time the key exists for secondary functions (decrypting old data, verifying old signatures). A key’s lifetime is always ≥ its crypto period.
Q: Does SP 800-57 require annual key rotation?
Not universally. The recommended crypto period depends on the key type and use case. Symmetric DEKs: ≤ 2 years. Asymmetric signing keys: 1-3 years. CA root keys: 10-20 years. “Annual rotation” is a common simplification that satisfies most requirements but isn’t the actual recommendation for all key types.
Q: How does SP 800-57 handle key compromise?
A compromised key must immediately transition to the “Compromised” state. All data protected by that key must be re-protected with a new key. The compromised key should only be retained long enough to decrypt existing data for re-encryption, then destroyed. The incident must be documented including: when compromise occurred, when detected, what data was affected, and remediation actions.
Q: What’s the relationship between SP 800-57 and SP 800-131A?
SP 800-57 defines key management lifecycle practices. SP 800-131A defines which algorithms and key sizes are acceptable (transitioning algorithms). They work together: SP 800-57 tells you how to manage keys, SP 800-131A tells you which algorithms those keys should use. Both must be satisfied for compliance.
Q: How do I handle keys that protect data with 10+ year retention requirements?
The key’s recipient usage period must cover the data retention period. Options: (1) Use a long-lived KEK to wrap short-lived DEKs — rotate DEKs frequently, keep KEK for the retention period. (2) Re-encrypt data with new keys periodically. (3) Archive the key securely for the retention period with strict access controls. Option 1 (envelope encryption) is the standard approach.
Related Reading:
